In the era of interconnected devices, securely connecting remote IoT (Internet of Things) devices using P2P (Peer-to-Peer) SSH on an Ubuntu server is crucial for maintaining data integrity and privacy. As more businesses and individuals adopt IoT solutions, ensuring secure communication between devices has become a top priority. This article will provide a detailed guide to setting up and managing secure remote IoT connections using SSH on an Ubuntu server.
IoT devices are transforming industries by enabling smart automation and real-time data exchange. However, these devices are often vulnerable to cyber threats if not properly secured. By leveraging SSH (Secure Shell) and P2P protocols, you can create a robust and encrypted connection between IoT devices and your Ubuntu server, ensuring that your data remains safe from unauthorized access.
This guide will walk you through the technical aspects of setting up a secure connection, from configuring SSH on an Ubuntu server to implementing best practices for IoT security. Whether you're a developer, system administrator, or IT professional, this article will equip you with the knowledge and tools needed to safeguard your IoT infrastructure.
Read also:Exploring The Legacy Of Vince Offer And The Iconic Shamwow
Table of Contents
- Introduction to Secure Remote IoT Connections
- Understanding SSH and Its Importance
- Setting Up an Ubuntu Server for IoT
- Implementing P2P SSH for IoT Devices
- Security Best Practices for IoT Connections
- Common Issues and Troubleshooting
- Optimizing Performance for Remote Connections
- Scaling Your IoT Infrastructure
- Protecting Data in Transit
- Conclusion and Next Steps
Introduction to Secure Remote IoT Connections
As IoT adoption continues to grow, the need for secure remote connections becomes increasingly important. Remote IoT devices often rely on SSH for encrypted communication, ensuring that data transmitted between devices and servers remains confidential. Ubuntu servers, with their robust security features and ease of configuration, are ideal for managing these connections.
In this section, we will explore the basics of remote IoT connections and why SSH is the preferred method for securing these interactions. We'll also discuss the role of Ubuntu servers in facilitating secure communication between IoT devices.
Why SSH for IoT?
SSH provides a secure channel for communication by encrypting data at both ends. This ensures that even if data is intercepted, it cannot be deciphered without the proper decryption keys. For IoT devices, which often operate in unsecured environments, SSH offers a reliable solution for maintaining data integrity.
Understanding SSH and Its Importance
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication over unsecured networks. It is widely used for remote server management, file transfers, and secure command execution. For IoT devices, SSH serves as a vital tool for ensuring that communication between devices and servers is both secure and reliable.
How SSH Works
SSH operates by creating an encrypted tunnel between two endpoints. This tunnel ensures that all data transmitted between the client and server is protected from eavesdropping and tampering. Key components of SSH include:
- Public-Key Cryptography: Ensures secure authentication between devices.
- Encryption Algorithms: Protects data in transit using advanced encryption standards.
- Integrity Checks: Verifies that data has not been altered during transmission.
Setting Up an Ubuntu Server for IoT
Ubuntu is a popular choice for server environments due to its stability, security features, and ease of use. Setting up an Ubuntu server for IoT involves several steps, including installation, configuration, and security hardening. This section will guide you through the process of preparing your Ubuntu server for secure IoT connections.
Read also:Vegamoviesrs Your Ultimate Guide To Streaming Movies Online
Installing Ubuntu Server
Begin by downloading the latest version of Ubuntu Server from the official website. Follow the installation instructions, ensuring that you select the appropriate options for your hardware and use case. Once installed, update your system to ensure all packages are up to date:
sudo apt update && sudo apt upgrade
Configuring SSH
After installing Ubuntu, enable SSH by installing the OpenSSH server:
sudo apt install openssh-server
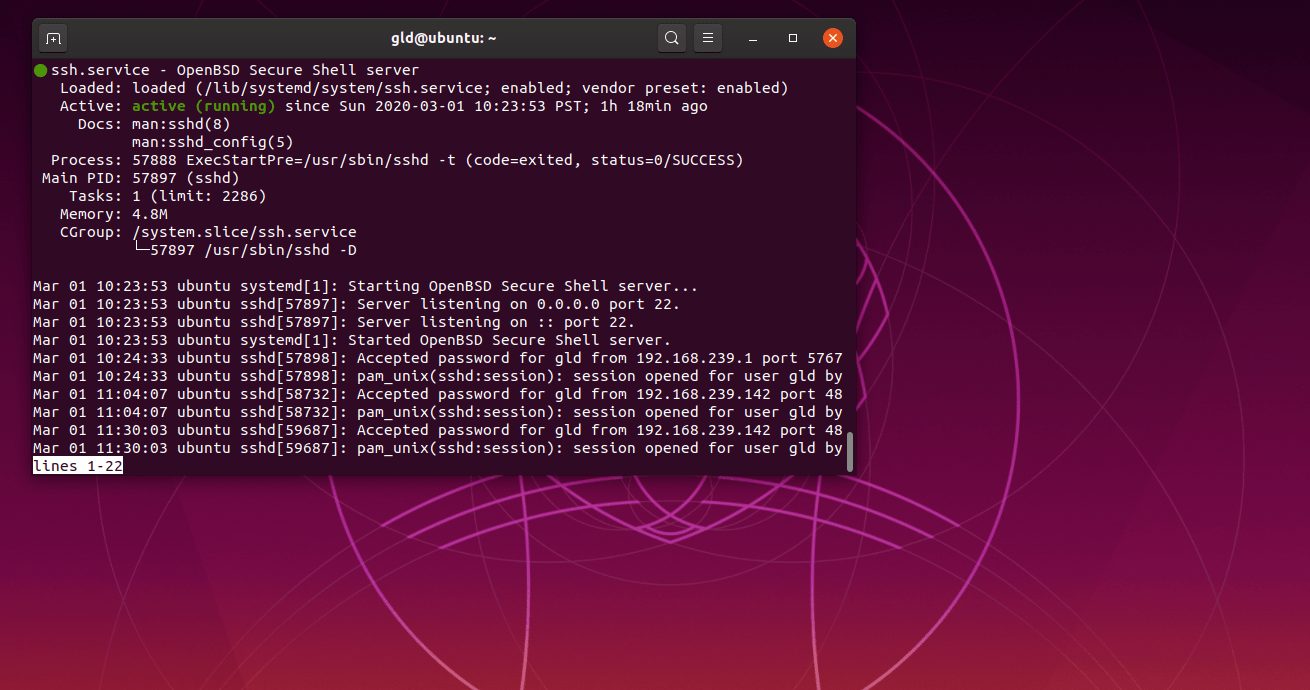
Verify that SSH is running by checking the service status:
sudo systemctl status ssh
Implementing P2P SSH for IoT Devices
Peer-to-Peer (P2P) SSH allows IoT devices to communicate directly with each other without relying on a central server. This approach reduces latency and improves efficiency, making it ideal for applications requiring real-time data exchange.
Setting Up P2P SSH
To implement P2P SSH, follow these steps:
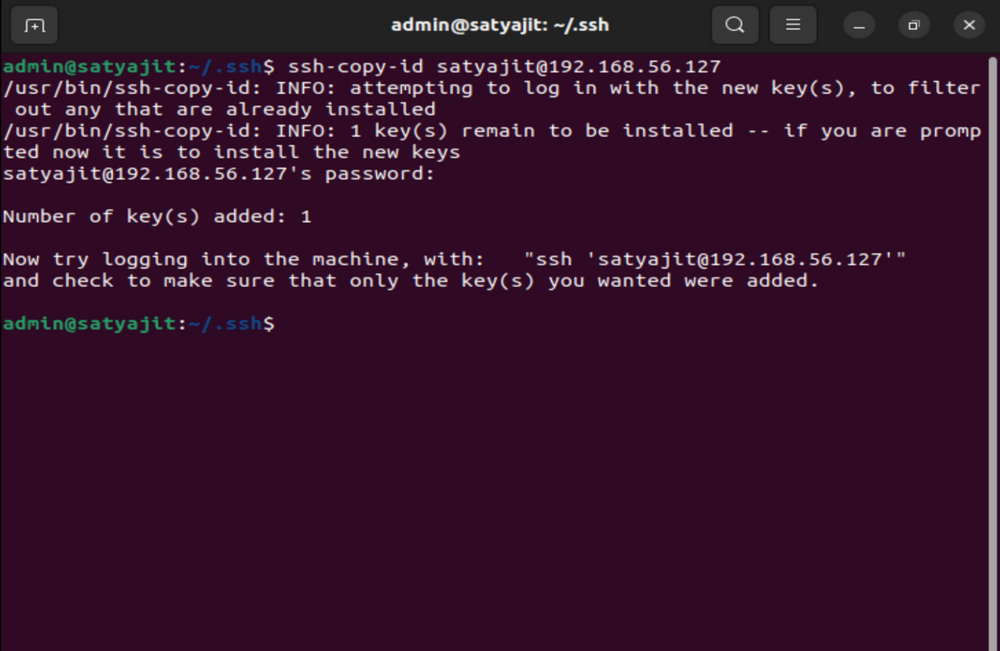
- Generate SSH keys for each IoT device.
- Exchange public keys between devices to establish trust.
- Configure SSH settings to allow direct connections between devices.
Security Best Practices for IoT Connections
Securing IoT connections requires a multi-layered approach. In addition to using SSH, it's essential to implement best practices to protect your devices and data. These include:
- Regular Updates: Keep your Ubuntu server and IoT devices updated with the latest security patches.
- Strong Passwords: Use complex passwords and consider implementing multi-factor authentication (MFA).
- Network Segmentation: Isolate IoT devices on a separate network to limit potential damage in case of a breach.
Common Issues and Troubleshooting
Even with proper configuration, issues can arise when setting up secure IoT connections. Common problems include connection failures, authentication errors, and performance bottlenecks. This section will address these issues and provide solutions.
Connection Failures
If you encounter connection failures, check the following:
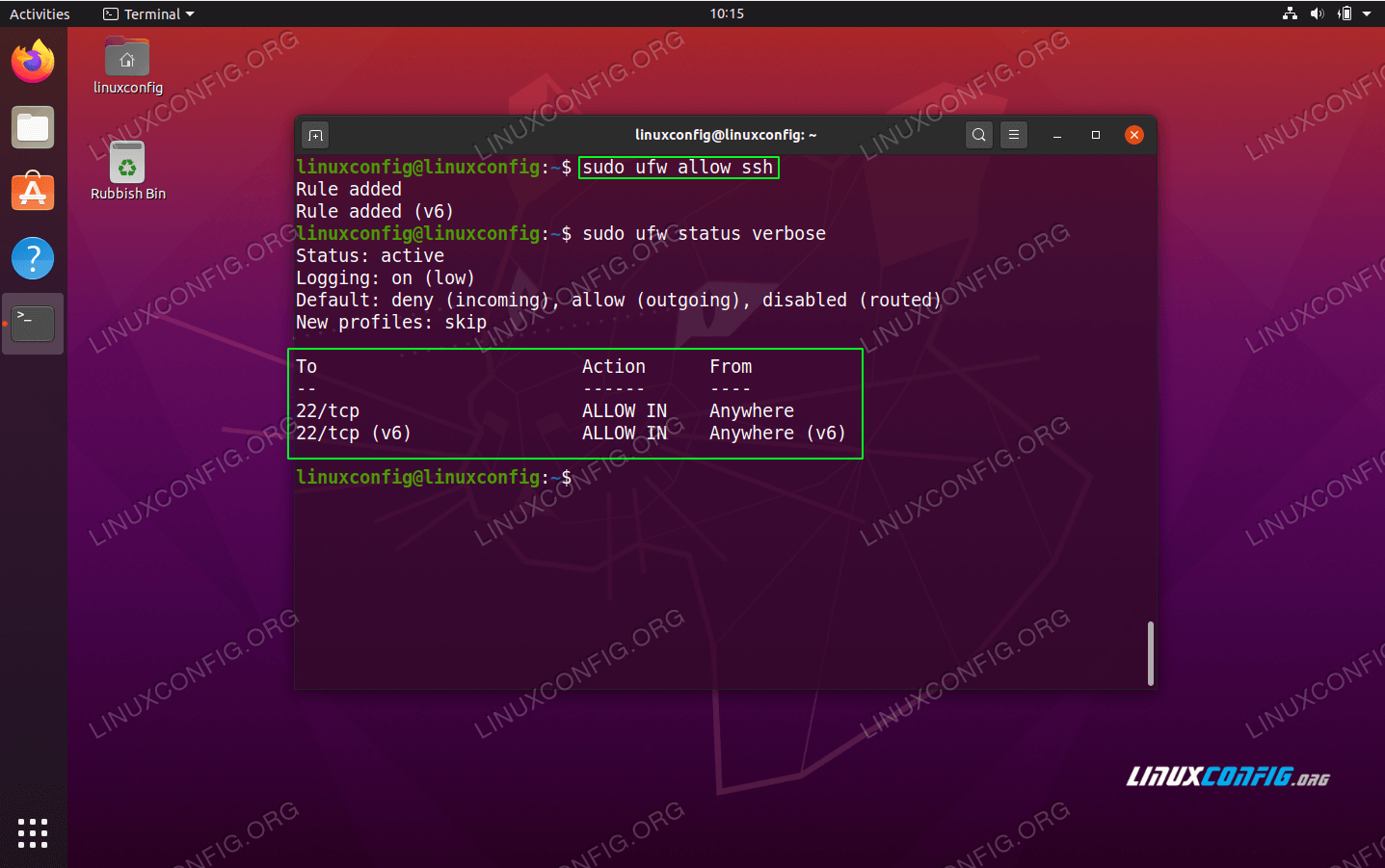
- Ensure that the SSH service is running on the server.
- Verify that firewall rules allow SSH traffic.
- Check that the correct IP address and port number are being used.
Optimizing Performance for Remote Connections
To ensure optimal performance for remote IoT connections, consider the following strategies:
- Compression: Enable SSH compression to reduce data transfer times.
- Bandwidth Management: Monitor and allocate bandwidth to prioritize critical IoT communications.
- Caching: Implement caching mechanisms to reduce the load on your server.
Scaling Your IoT Infrastructure
As your IoT deployment grows, scaling your infrastructure becomes essential. Ubuntu servers can be easily scaled to accommodate additional devices and increased traffic. Consider using cloud-based solutions or load balancers to distribute the workload efficiently.
Protecting Data in Transit
Data protection is a critical aspect of secure IoT connections. In addition to using SSH, consider implementing additional measures such as:
- Encryption: Use end-to-end encryption for all data transmissions.
- Access Controls: Limit access to sensitive data by implementing strict access controls.
- Monitoring: Continuously monitor your IoT infrastructure for suspicious activity.
Conclusion and Next Steps
Securing remote IoT connections using P2P SSH on an Ubuntu server is a critical step in protecting your data and ensuring the integrity of your IoT infrastructure. By following the guidelines outlined in this article, you can create a robust and secure environment for your IoT devices.
We encourage you to take the following actions:
- Review and implement the security best practices discussed in this article.
- Regularly update your Ubuntu server and IoT devices to address potential vulnerabilities.
- Share your thoughts and experiences in the comments section below.
Thank you for reading, and we hope this guide has been informative and helpful. For more articles on IoT security and related topics, explore our website further.