Connecting remote IoT devices using SSH on Ubuntu has become increasingly essential for managing distributed systems securely. In today's interconnected world, ensuring secure communication between devices is paramount to protect sensitive data and maintain operational integrity. This article will guide you step-by-step on how to securely connect remote IoT devices using peer-to-peer (P2P) SSH on Ubuntu.
As the Internet of Things (IoT) continues to grow, the need for secure communication protocols becomes more critical. IoT devices often operate in environments where security vulnerabilities can lead to significant risks. Understanding how to establish a secure connection using SSH on Ubuntu will help mitigate these risks and ensure robust protection for your devices.
This guide is designed for individuals and organizations looking to enhance their IoT network security. Whether you're a developer, system administrator, or IT professional, this article will provide you with practical knowledge and actionable steps to implement secure connections using SSH on Ubuntu.
Read also:5movierulz Telugu 2025 Your Ultimate Guide To Telugu Movies And Beyond
Understanding IoT and Its Security Challenges
IoT refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to collect and exchange data. However, with the increasing number of connected devices, security challenges have emerged. Hackers can exploit vulnerabilities in IoT devices, leading to data breaches and unauthorized access.
Some of the primary security challenges in IoT include:
- Limited processing power and memory in IoT devices, making encryption and security protocols harder to implement.
- Poor default security settings, such as weak passwords and outdated firmware.
- Difficulty in monitoring and managing large numbers of distributed devices.
To address these challenges, implementing secure communication protocols like SSH is crucial. SSH provides a secure channel over an unsecured network, ensuring encrypted data transfer and authentication between devices.
What is SSH and Why Use It for IoT?
SSH, or Secure Shell, is a cryptographic network protocol used to securely operate network services over an unsecured network. It provides strong authentication and secure data communication, making it ideal for managing remote IoT devices.
Using SSH for IoT offers several advantages:
- Encryption: SSH encrypts all data transmitted between devices, preventing eavesdropping and data tampering.
- Authentication: SSH ensures that only authorized users and devices can access the system, reducing the risk of unauthorized access.
- Remote Management: SSH allows administrators to manage IoT devices remotely, simplifying maintenance and troubleshooting.
By leveraging SSH, organizations can enhance the security and reliability of their IoT networks, protecting sensitive data and maintaining operational integrity.
Read also:Telugu Movierulz 2025 The Ultimate Guide To Telugu Movies And Beyond
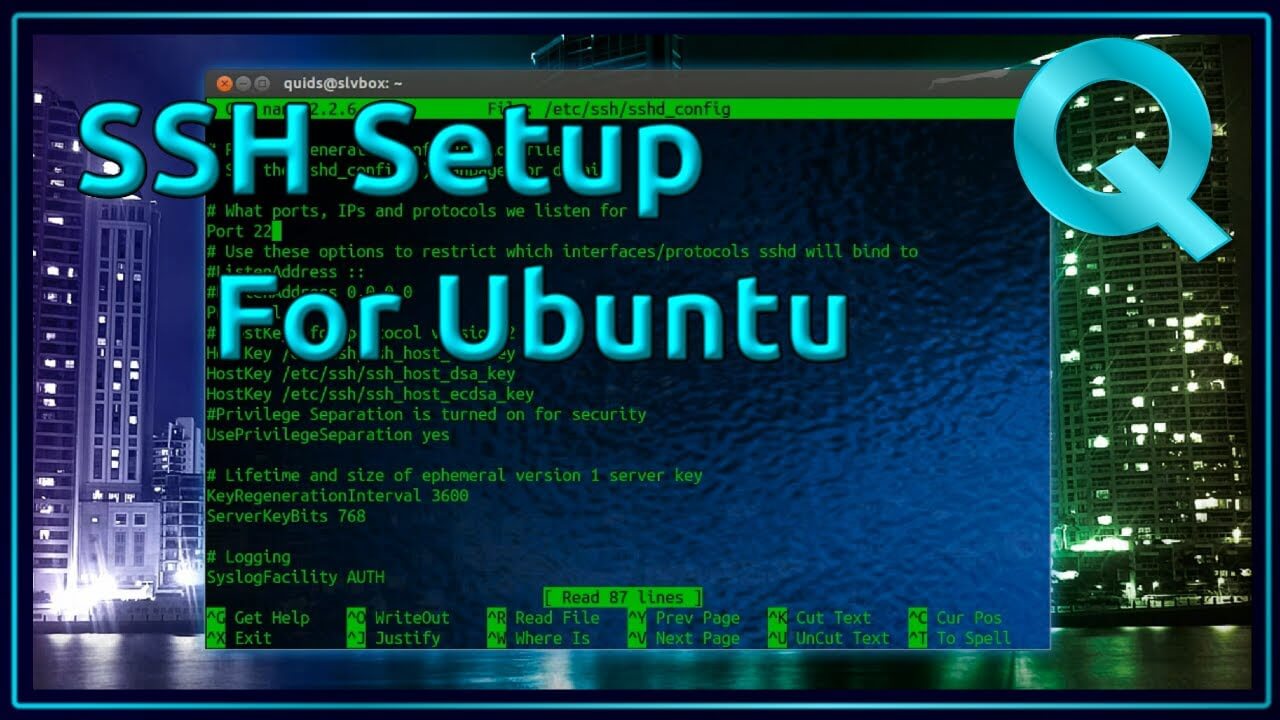
Setting Up SSH on Ubuntu
Installing OpenSSH on Ubuntu
Before connecting IoT devices via SSH, you need to install the OpenSSH server on your Ubuntu machine. Follow these steps:
- Open the terminal on your Ubuntu system.
- Update your package list by running the command:
sudo apt update. - Install OpenSSH server using the command:
sudo apt install openssh-server. - Verify that SSH is running with the command:
sudo systemctl status ssh.
Once installed, your Ubuntu system will be ready to accept SSH connections.
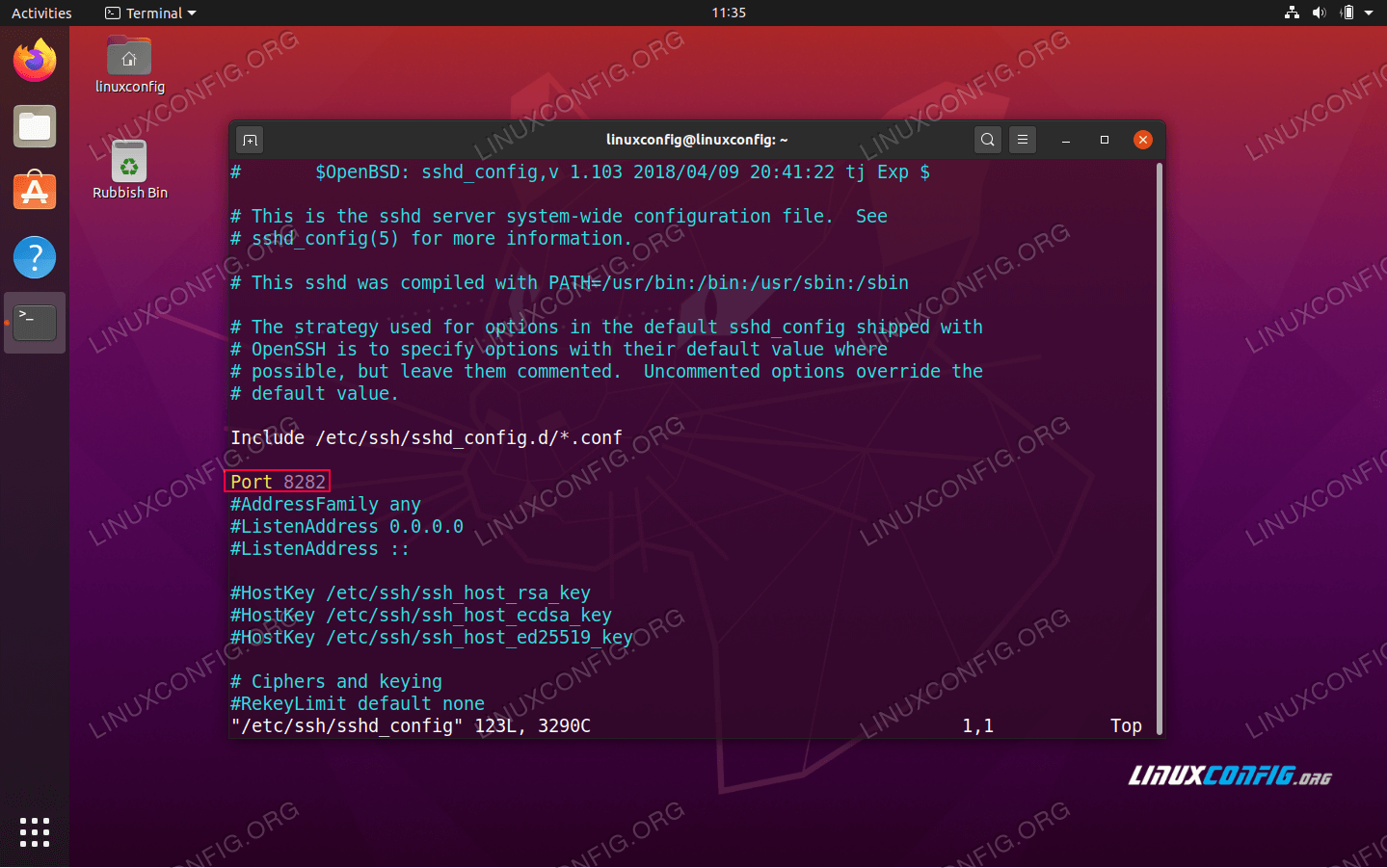
Configuring SSH for Security
After installing SSH, it's essential to configure it for optimal security. Here are some recommendations:
- Disable Root Login: Modify the SSH configuration file (
/etc/ssh/sshd_config) to disable root login by settingPermitRootLogin no. - Use Key-Based Authentication: Generate SSH keys and configure your system to use them instead of passwords.
- Change Default Port: Change the default SSH port (22) to a custom port to reduce automated attacks.
These configurations will help strengthen the security of your SSH connections, making it more difficult for attackers to gain unauthorized access.
Peer-to-Peer (P2P) SSH Connections
Traditional SSH connections involve a client-server architecture, where the client connects to the server. However, in some IoT scenarios, peer-to-peer (P2P) connections may be more appropriate. P2P SSH allows devices to connect directly without relying on a central server.
To establish a P2P SSH connection:
- Ensure both devices have SSH installed and configured.
- Exchange public keys between the devices to enable key-based authentication.
- Use the SSH command to connect directly to the peer device, specifying its IP address or hostname.
P2P SSH can simplify network architecture and reduce the need for intermediary servers, making it an attractive option for IoT deployments.
Example: Securely Connect Remote IoT Devices Using SSH on Ubuntu
Scenario Overview
Imagine you have two IoT devices running Ubuntu: Device A and Device B. You want to establish a secure connection between them using SSH. Follow these steps:
- Install OpenSSH on both devices as described earlier.
- Generate SSH keys on Device A using the command:
ssh-keygen -t rsa. - Copy the public key from Device A to Device B using the command:
ssh-copy-id user@deviceB. - Test the connection by running:
ssh user@deviceB.
This example demonstrates how to securely connect remote IoT devices using SSH on Ubuntu, ensuring encrypted communication and authentication.
Best Practices for Secure Connections
When establishing secure connections between IoT devices, consider the following best practices:
- Regularly Update Firmware: Keep your IoT devices and Ubuntu systems up to date to protect against known vulnerabilities.
- Monitor Connections: Use tools like fail2ban to monitor and block suspicious SSH connection attempts.
- Limit Access: Restrict SSH access to specific IP addresses or subnets to minimize exposure.
Implementing these best practices will enhance the security of your IoT network and protect against potential threats.
Data Security in IoT Networks
Data security is a critical aspect of IoT network management. When securely connecting remote IoT devices using SSH on Ubuntu, it's essential to consider data encryption, access control, and network segmentation.
Some key strategies for ensuring data security include:
- End-to-End Encryption: Use SSH to encrypt all data transmitted between devices, ensuring confidentiality and integrity.
- Role-Based Access Control: Implement access controls to ensure that only authorized users and devices can access sensitive data.
- Network Segmentation: Isolate IoT devices from other network segments to limit the potential impact of a security breach.
By prioritizing data security, organizations can protect sensitive information and maintain the trust of their customers and stakeholders.
Monitoring and Managing IoT Devices
Effectively monitoring and managing IoT devices is crucial for maintaining network security and operational efficiency. Tools like SSH can play a vital role in this process by enabling remote access and management.
To monitor and manage IoT devices:
- Use SSH for Remote Access: Leverage SSH to securely access and manage IoT devices from remote locations.
- Implement Logging: Configure logging on your IoT devices to track activities and detect potential security threats.
- Automate Tasks: Use SSH scripts to automate routine tasks, such as backups and firmware updates.
These strategies will help streamline IoT device management and ensure consistent security practices across your network.
Future Trends in IoT Security
As IoT technology continues to evolve, new security trends and innovations are emerging. Some of the key trends to watch include:
- Blockchain for IoT Security: Blockchain technology can enhance IoT security by providing tamper-proof records of device interactions.
- Artificial Intelligence (AI) for Threat Detection: AI-powered tools can analyze network traffic and detect anomalies, helping to identify potential security threats.
- Quantum Cryptography: Advances in quantum cryptography may lead to more secure encryption methods for IoT devices.
Staying informed about these trends will help organizations prepare for the future of IoT security and ensure their networks remain protected.
Conclusion
In conclusion, securely connecting remote IoT devices using SSH on Ubuntu is a critical step in ensuring the security and reliability of your IoT network. By following the steps outlined in this guide, you can establish encrypted communication channels, implement robust authentication mechanisms, and enhance overall network security.
We encourage readers to take action by implementing the best practices discussed in this article. If you found this guide helpful, please leave a comment or share it with others who may benefit from the information. Additionally, feel free to explore other articles on our site for more insights into IoT security and related topics.
Table of Contents
- Understanding IoT and Its Security Challenges
- What is SSH and Why Use It for IoT?
- Setting Up SSH on Ubuntu
- Peer-to-Peer (P2P) SSH Connections
- Example: Securely Connect Remote IoT Devices Using SSH on Ubuntu
- Data Security in IoT Networks
- Monitoring and Managing IoT Devices
- Future Trends in IoT Security
- Conclusion