In today's interconnected world, securely connect remote IoT P2P SSH download Windows has become a critical need for businesses and individuals alike. The Internet of Things (IoT) continues to expand, with billions of devices now connected globally, and ensuring secure communication is paramount. This guide aims to provide a detailed overview of how to establish secure connections for remote IoT devices using SSH on Windows.
As technology advances, so do the methods used by cybercriminals to exploit vulnerabilities in connected systems. Securing remote IoT devices is no longer an option but a necessity. In this article, we will explore various techniques and tools that can help you achieve robust security while connecting IoT devices remotely using SSH on Windows.
This guide is designed for both beginners and advanced users who want to understand the intricacies of remote IoT security. By the end of this article, you will have a comprehensive understanding of how to securely connect remote IoT devices using P2P SSH on Windows, along with practical steps and tips to protect your data.
Read also:Exploring The Legacy Of Vince Offer And The Iconic Shamwow
Understanding Remote IoT Connections
Remote IoT connections enable devices to communicate and share data over the internet without requiring physical interaction. These connections are essential for monitoring, managing, and controlling IoT devices from distant locations. However, the security of these connections is vital to prevent unauthorized access and data breaches.
Key Challenges in Remote IoT Connections
- Data interception and eavesdropping
- Unauthorized access to devices
- Vulnerabilities in communication protocols
- Insufficient encryption mechanisms
Addressing these challenges requires a robust security framework, which is where SSH comes into play. SSH provides a secure channel for communication, ensuring that data transmitted between devices remains encrypted and protected from prying eyes.
What is SSH and Why Use It?
SSH, or Secure Shell, is a cryptographic protocol used to secure network services over an unsecured network. It provides strong authentication and encrypted data communications, making it ideal for securing remote IoT connections. By using SSH, you can ensure that your IoT devices are protected from potential threats.
Benefits of Using SSH for IoT
- Encryption of data in transit
- Strong authentication mechanisms
- Protection against man-in-the-middle attacks
- Compatibility with multiple platforms
SSH is widely regarded as one of the most secure methods for remote communication, making it a preferred choice for securing IoT devices.
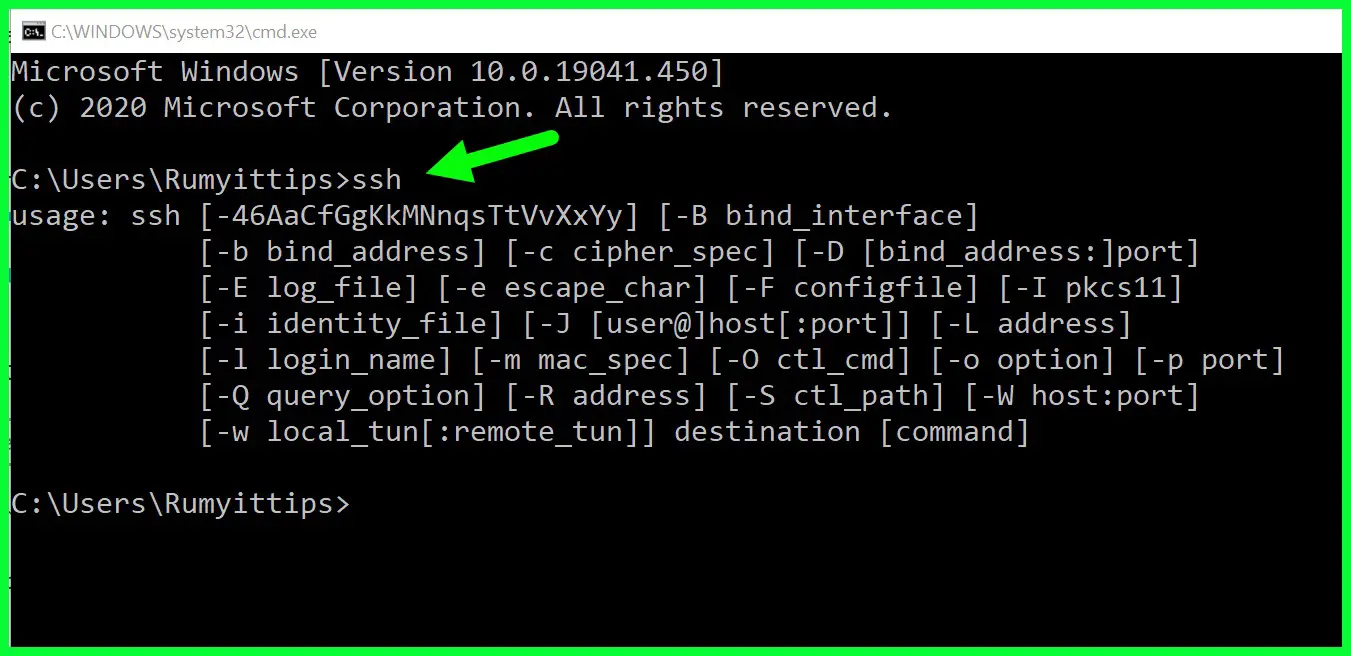
Setting Up SSH on Windows
Windows 10 and later versions come with built-in support for SSH, making it easier than ever to set up secure connections. Below are the steps to enable SSH on your Windows machine:
Enabling OpenSSH on Windows
- Open the Start menu and go to Settings.
- Select "Apps" and then click on "Optional features."
- Click on "Add a feature" and search for "OpenSSH Client."
- Select "OpenSSH Client" and click "Install."
Once installed, you can use the SSH client from the command line or PowerShell to establish secure connections.
Read also:5movierulz Telugu Your Ultimate Guide To Exploring Telugu Movies
Securing IoT Devices with SSH
Securing IoT devices involves more than just enabling SSH. It requires a multi-layered approach that includes configuring firewalls, setting up strong passwords, and regularly updating firmware. Below are some best practices for securing IoT devices using SSH:
Best Practices for SSH Security
- Use strong, unique passwords or SSH keys for authentication.
- Disable password authentication and rely solely on SSH keys.
- Limit access to specific IP addresses using firewall rules.
- Regularly update SSH clients and servers to patch vulnerabilities.
Implementing these practices will significantly enhance the security of your IoT devices when using SSH for remote connections.
Peer-to-Peer (P2P) Connections in IoT
P2P connections allow IoT devices to communicate directly with each other without the need for a central server. This architecture can reduce latency and improve efficiency, making it ideal for certain IoT applications. However, securing P2P connections requires careful consideration of encryption and authentication methods.
Securing P2P IoT Connections
- Use end-to-end encryption for all data transmissions.
- Implement mutual authentication to verify the identity of both devices.
- Regularly update security protocols to address emerging threats.
By securing P2P connections, you can ensure that your IoT devices remain protected while maintaining optimal performance.
Download and Install SSH Clients on Windows
While Windows includes a built-in SSH client, there are several third-party clients available that offer additional features and functionality. Below are some popular SSH clients for Windows:
Popular SSH Clients for Windows
- PuTTY: A lightweight and easy-to-use SSH client.
- WinSCP: A powerful SFTP client that supports file transfers over SSH.
- Bitvise SSH Client: A feature-rich client with support for SSH tunnels and port forwarding.
Choosing the right SSH client depends on your specific needs and preferences. Each client has its own strengths, so it's worth exploring them to find the best fit for your use case.
Configuring SSH for IoT Devices
Configuring SSH for IoT devices involves several steps, including setting up the SSH server, generating SSH keys, and configuring firewall rules. Below is a step-by-step guide to configuring SSH on an IoT device:
Step-by-Step SSH Configuration
- Install an SSH server on your IoT device.
- Generate SSH keys for authentication.
- Configure firewall rules to allow SSH traffic.
- Test the connection using an SSH client.
By following these steps, you can ensure that your IoT devices are securely configured for remote access.
Troubleshooting Common SSH Issues
Like any technology, SSH can sometimes encounter issues that prevent it from functioning correctly. Below are some common SSH issues and their solutions:
Solutions to Common SSH Problems
- Connection refused: Ensure the SSH server is running and the port is open.
- Authentication failure: Verify that the correct credentials or SSH keys are being used.
- Timeout errors: Check network connectivity and ensure no firewalls are blocking the connection.
Addressing these issues promptly can help ensure that your SSH connections remain stable and reliable.
Best Practices for Secure IoT Deployment
Deploying IoT devices securely requires a comprehensive approach that includes both hardware and software considerations. Below are some best practices for deploying IoT devices securely:
IoT Deployment Best Practices
- Use secure communication protocols like SSH and TLS.
- Regularly update firmware and software to patch vulnerabilities.
- Implement strong authentication mechanisms for all devices.
- Monitor devices for suspicious activity and address issues promptly.
Following these best practices will help ensure that your IoT deployment remains secure and resilient against potential threats.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using P2P SSH on Windows is a critical aspect of modern IoT deployments. By understanding the challenges and implementing the best practices outlined in this guide, you can ensure that your IoT devices remain protected while maintaining optimal performance.
We encourage you to take action by implementing the steps discussed in this article. Whether you're a beginner or an advanced user, securing your IoT devices is essential for protecting your data and maintaining trust with your users.
Feel free to leave a comment below if you have any questions or would like to share your experiences. Additionally, don't forget to explore our other articles for more insights into IoT security and related topics.
Table of Contents
- Securely Connect Remote IoT P2P SSH Download Windows: A Comprehensive Guide
- Understanding Remote IoT Connections
- Key Challenges in Remote IoT Connections
- What is SSH and Why Use It?
- Benefits of Using SSH for IoT
- Setting Up SSH on Windows
- Enabling OpenSSH on Windows
- Securing IoT Devices with SSH
- Best Practices for SSH Security
- Peer-to-Peer (P2P) Connections in IoT
- Securing P2P IoT Connections
- Download and Install SSH Clients on Windows
- Popular SSH Clients for Windows
- Configuring SSH for IoT Devices
- Step-by-Step SSH Configuration
- Troubleshooting Common SSH Issues
- Solutions to Common SSH Problems
- Best Practices for Secure IoT Deployment
- IoT Deployment Best Practices
- Conclusion and Call to Action