In today's interconnected world, the ability to remotely access IoT devices from an Android device using SSH has become increasingly essential. Whether you're a tech enthusiast, a developer, or a professional managing IoT systems, understanding how to leverage SSH for remote device access can significantly enhance your productivity and security. This article will guide you through the intricacies of SSH remote IoT device access on Android APK, providing step-by-step instructions, expert tips, and valuable insights to help you master this critical skill.
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. As IoT devices continue to grow in popularity, the demand for secure remote access solutions has surged. This is where SSH comes into play, offering a robust and encrypted way to interact with IoT devices from anywhere in the world.
Whether you're configuring a smart home system, monitoring industrial sensors, or managing a fleet of connected devices, this article will equip you with the knowledge and tools you need to harness the full potential of SSH remote IoT device access on Android APK. Let's dive in!
Read also:Kaitlan Collins Husband A Comprehensive Guide To Her Personal Life
Table of Contents
- Introduction to SSH
- Benefits of SSH for Remote IoT Device Access
- Android APK for SSH Remote Access
- How to Set Up SSH on IoT Devices
- Connecting IoT Devices via SSH
- Securing SSH Connections
- Common Issues and Troubleshooting
- Best Practices for SSH Remote IoT Access
- Alternatives to SSH for IoT Access
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a network protocol designed to provide secure communication between two devices over an unsecured network. It encrypts all data transmitted between the client and server, ensuring confidentiality and integrity. SSH is widely used for remote login, command execution, file transfer, and more, making it an indispensable tool for IT professionals and developers alike.
For IoT devices, SSH offers a secure way to manage and interact with devices remotely. Unlike traditional methods that rely on unencrypted protocols, SSH ensures that sensitive information remains protected from unauthorized access and eavesdropping.
Why SSH is Critical for IoT
- Encryption: SSH encrypts all data, preventing interception and tampering.
- Authentication: SSH supports various authentication methods, including passwords and public key authentication.
- Portability: SSH is supported on a wide range of platforms, including Linux, Windows, macOS, and Android.
Benefits of SSH for Remote IoT Device Access
Using SSH for remote IoT device access comes with numerous advantages that enhance both security and convenience. Below are some of the key benefits:
Enhanced Security
SSH employs strong encryption algorithms to secure data transmission, making it one of the most secure methods for remote access. This is particularly important for IoT devices, which often handle sensitive data and require robust protection against cyber threats.
Reliability
SSH connections are reliable and resilient, ensuring that you can maintain a stable connection even in challenging network conditions. This reliability is crucial for managing IoT devices that may be located in remote or hard-to-reach areas.
Flexibility
SSH supports a wide range of functionalities, including command execution, file transfer, and tunneling. This flexibility allows you to perform various tasks on your IoT devices remotely, from simple configuration changes to complex troubleshooting.
Read also:Camilla Arauacutejo Nudes Unveiling The Truth And Debunking Myths
Android APK for SSH Remote Access
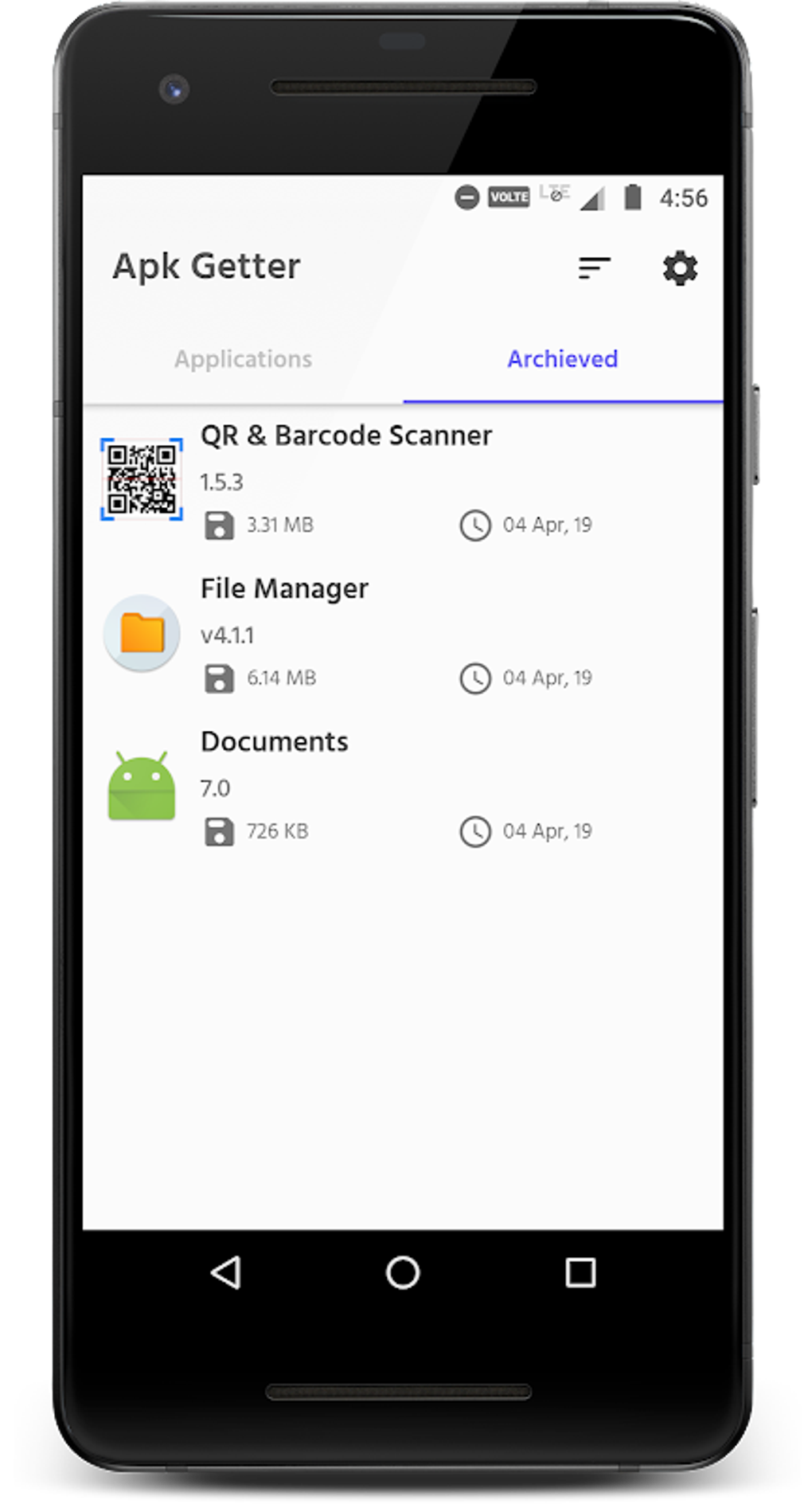
For Android users, several APKs (Android Package Kits) are available that enable SSH remote access to IoT devices. These apps provide a user-friendly interface and a range of features to simplify the process of connecting to and managing IoT devices.
Popular SSH APKs for Android
- Termux: A powerful terminal emulator and Linux environment app that supports SSH and other command-line tools.
- JSCH SSH Client: A lightweight SSH client that offers basic SSH functionality and is easy to use for beginners.
- ConnectBot: A feature-rich SSH client that supports public key authentication, port forwarding, and more.
How to Set Up SSH on IoT Devices
Before you can remotely access your IoT devices via SSH, you need to ensure that SSH is properly configured on the devices. Below is a step-by-step guide to setting up SSH on common IoT platforms:
Step 1: Enable SSH on Your IoT Device
Most IoT devices come with SSH pre-installed but disabled by default. To enable SSH, you typically need to access the device's configuration settings and activate the SSH service.
Step 2: Configure SSH Settings
Once SSH is enabled, configure the necessary settings, such as port number, authentication method, and access permissions. It's recommended to use non-standard port numbers and strong authentication methods to enhance security.
Step 3: Test the Connection
After configuring SSH, test the connection by attempting to log in to the device from another machine. This will ensure that SSH is working correctly and that you can access the device remotely.
Connecting IoT Devices via SSH
Once SSH is set up on your IoT devices, you can connect to them remotely using an SSH client on your Android device. Below are the steps to establish a connection:
Using Termux
- Install Termux from the Google Play Store.
- Open Termux and type the command: `ssh username@device_ip`.
- Enter the password or use public key authentication to log in.
Using ConnectBot
- Download and install ConnectBot on your Android device.
- Enter the device's IP address and port number in the connection settings.
- Choose the authentication method and establish the connection.
Securing SSH Connections
While SSH provides a secure method for remote access, it's essential to implement additional security measures to protect your IoT devices. Below are some best practices for securing SSH connections:
Use Public Key Authentication
Public key authentication is more secure than password-based authentication and eliminates the risk of brute-force attacks. Generate a public-private key pair and configure your IoT devices to accept only public key authentication.
Disable Root Login
Disallowing root login reduces the risk of unauthorized access and ensures that users must log in with a regular account before escalating privileges.
Implement Firewall Rules
Configure firewall rules to restrict SSH access to trusted IP addresses and limit the number of failed login attempts.
Common Issues and Troubleshooting
Despite its robustness, SSH connections can sometimes encounter issues. Below are some common problems and their solutions:
Connection Refused
This issue typically occurs when the SSH service is not running on the IoT device or when the device's IP address is incorrect. Verify that the SSH service is active and double-check the IP address and port number.
Authentication Failed
If you receive an authentication failed error, ensure that you're using the correct username and password or that your public key is properly configured on the IoT device.
Best Practices for SSH Remote IoT Access
To maximize the benefits of SSH remote IoT access, follow these best practices:
Regularly Update Firmware
Keep your IoT devices' firmware up to date to ensure compatibility with the latest SSH protocols and security patches.
Monitor Logs
Regularly review SSH logs to detect and respond to suspicious activity promptly.
Backup Configuration
Regularly back up your IoT devices' configuration settings to prevent data loss in case of a failure or misconfiguration.
Alternatives to SSH for IoT Access
While SSH is the most widely used method for remote IoT device access, there are alternative solutions that may suit specific use cases:
Web-Based Interfaces
Some IoT devices offer web-based interfaces that allow remote access through a browser. While convenient, these interfaces may not provide the same level of security as SSH.
MQTT
MQTT (Message Queuing Telemetry Transport) is a lightweight protocol designed for IoT devices. It's ideal for low-bandwidth environments but lacks the security features of SSH.
Conclusion
SSH remote IoT device access on Android APK offers a secure, reliable, and flexible way to manage and interact with IoT devices from anywhere in the world. By following the guidelines and best practices outlined in this article, you can harness the full potential of SSH and ensure the security and efficiency of your IoT systems.
We encourage you to experiment with the various SSH clients available on Android and explore the advanced features they offer. Don't hesitate to leave a comment or share this article with others who may benefit from it. For more in-depth guides and tutorials, explore our other articles on IoT and cybersecurity.
Data Source: SSH Official Website, Linux Foundation