SSH RemoteIoT tutorial is a crucial guide for anyone looking to secure their IoT devices through remote access. The Internet of Things (IoT) has revolutionized how we interact with technology, but with this advancement comes the need for robust security measures. By leveraging SSH (Secure Shell), users can establish encrypted connections between devices, ensuring data integrity and privacy.
In this ever-connected world, IoT devices are increasingly integrated into daily life, from smart homes to industrial applications. However, securing these devices remains a challenge. This tutorial will provide step-by-step guidance on setting up SSH for remote IoT devices, ensuring your data remains safe from unauthorized access.
This SSH RemoteIoT tutorial is designed for beginners and professionals alike, offering in-depth insights into the setup process, best practices, troubleshooting tips, and advanced configurations. By the end of this guide, you will have a solid understanding of how to implement SSH for remote IoT connectivity effectively.
Read also:Hdhub4uin Movie Your Ultimate Destination For Highquality Films
Table of Contents
- Introduction to SSH RemoteIoT
- Why Use SSH for IoT Devices?
- Prerequisites for Setting Up SSH
- Installing SSH on IoT Devices
- Configuring SSH for IoT
- Accessing IoT Devices Remotely
- Enhancing SSH Security
- Troubleshooting Common Issues
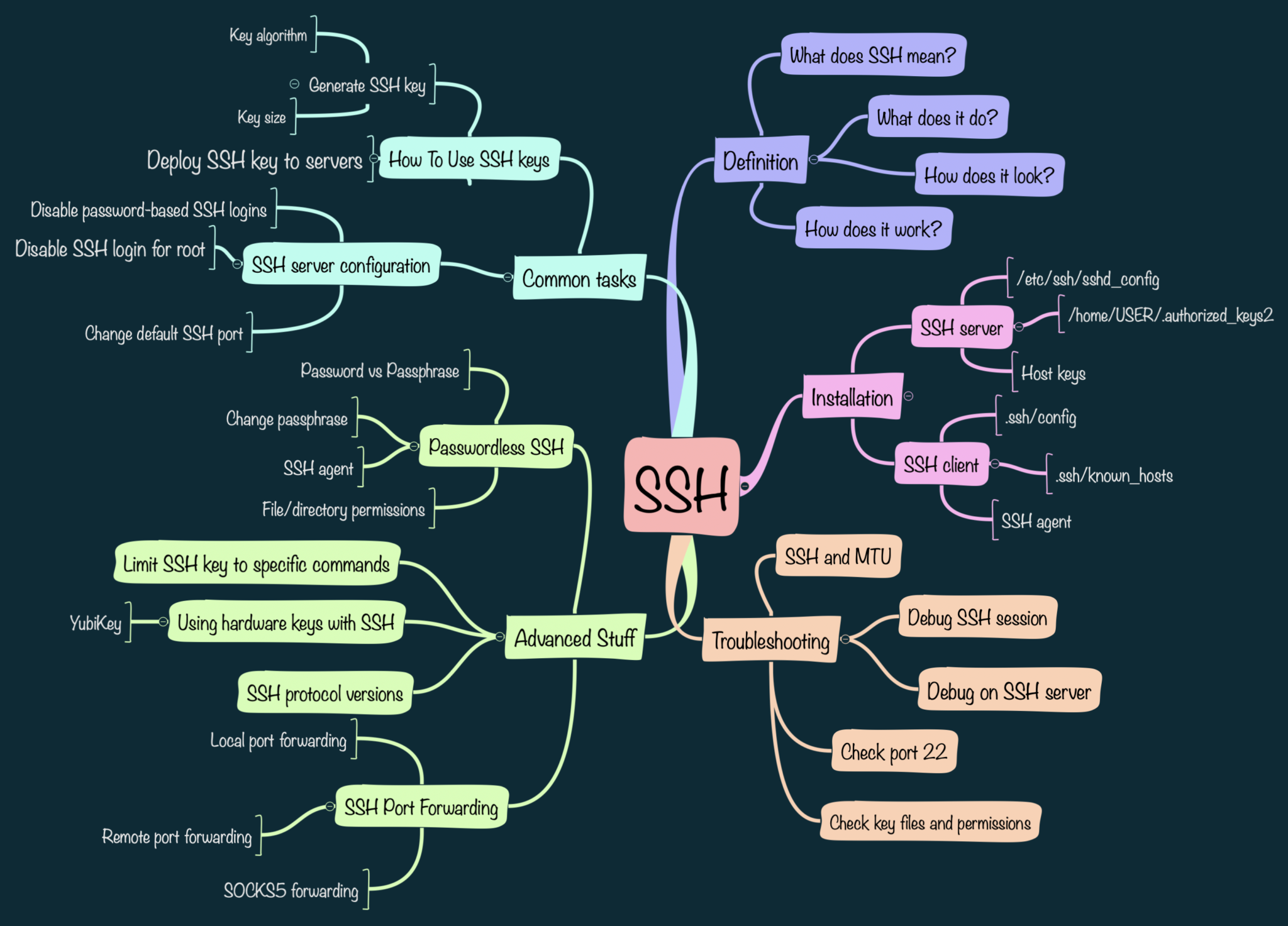
- Advanced SSH Configurations
- Conclusion and Call to Action
Introduction to SSH RemoteIoT
The Internet of Things (IoT) has transformed how devices communicate and interact, creating a network of interconnected systems. However, ensuring secure communication between these devices is paramount. SSH RemoteIoT tutorial provides a comprehensive guide to securing IoT devices through remote access using SSH.
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication over an unsecured network. It is widely used for remote login and command execution, making it an ideal choice for securing IoT devices. By following this tutorial, users can establish a secure connection to their IoT devices from anywhere in the world.
Why Use SSH for IoT Devices?
SSH offers several advantages for IoT devices, including encryption, authentication, and data integrity. These features make it an essential tool for securing IoT networks.
Encryption
SSH encrypts all data transmitted between devices, ensuring that sensitive information remains confidential. This encryption protects against eavesdropping and man-in-the-middle attacks.
Authentication
SSH provides robust authentication mechanisms, allowing users to verify the identity of both the client and server. This ensures that only authorized users can access IoT devices.
Read also:Hdhub4u In Bollywood Your Ultimate Guide To Movie Downloads And Entertainment
Data Integrity
SSH ensures that data transmitted between devices remains intact and unaltered during transmission. This is crucial for maintaining the reliability of IoT systems.
Prerequisites for Setting Up SSH
Before setting up SSH for IoT devices, there are several prerequisites to consider. These include the necessary hardware, software, and network configurations.
- Hardware Requirements: Ensure your IoT devices have sufficient processing power and memory to support SSH.
- Software Requirements: Install a compatible operating system on your IoT devices, such as Linux or a lightweight IoT OS.
- Network Configuration: Configure your network to allow SSH traffic, ensuring that firewalls and routers are set up correctly.
Installing SSH on IoT Devices
Installing SSH on IoT devices involves several steps, depending on the operating system used. Below is a guide for installing SSH on a Linux-based IoT device.
Step 1: Update the System
Begin by updating your IoT device's operating system to ensure all packages are up to date.
sudo apt update && sudo apt upgrade
Step 2: Install SSH Server
Install the OpenSSH server package, which provides the necessary tools for SSH communication.
sudo apt install openssh-server
Step 3: Start and Enable SSH Service
Start the SSH service and enable it to start automatically on boot.
sudo systemctl start sshsudo systemctl enable ssh
Configuring SSH for IoT
Once SSH is installed, it's essential to configure it properly for optimal performance and security.
SSH Configuration File
The SSH configuration file, located at /etc/ssh/sshd_config, allows users to customize various settings. Below are some key configurations to consider:
- Port Number: Change the default SSH port (22) to a custom port for added security.
- Password Authentication: Disable password authentication and use public key authentication instead.
- Root Login: Disable root login to prevent unauthorized access.
Port 2222PasswordAuthentication noPermitRootLogin no
Accessing IoT Devices Remotely
With SSH configured, users can now access their IoT devices remotely. This section provides guidance on connecting to IoT devices from different platforms.
Using SSH from Linux/Mac
From a Linux or Mac terminal, use the following command to connect to your IoT device:
ssh username@ip_address -p port_number
Using SSH from Windows
Windows users can use tools like PuTTY or the built-in SSH client in Windows 10 to connect to IoT devices.
Enhancing SSH Security
While SSH provides a secure communication channel, additional measures can further enhance its security.
Use Public Key Authentication
Public key authentication eliminates the need for passwords, reducing the risk of brute-force attacks.
Implement Firewall Rules
Configure firewall rules to restrict access to the SSH port, allowing only trusted IP addresses.
Regularly Update SSH
Keep the SSH server software up to date to protect against vulnerabilities.
Troubleshooting Common Issues
Despite careful configuration, issues may arise when setting up SSH for IoT devices. Below are some common problems and their solutions.
- Connection Refused: Ensure the SSH service is running and the port is open.
- Authentication Failed: Verify the username, password, or public key is correct.
- Timeout Errors: Check network connectivity and firewall settings.
Advanced SSH Configurations
For users seeking more advanced configurations, SSH offers several options to optimize performance and security.
SSH Tunneling
SSH tunneling allows users to securely access services on remote IoT devices, such as web servers or databases.
SSH Port Forwarding
Port forwarding enables users to redirect traffic from one port to another, enhancing security and flexibility.
SSH Key Management
Implementing a centralized SSH key management system can simplify key distribution and revocation.
Conclusion and Call to Action
This SSH RemoteIoT tutorial has provided a comprehensive guide to securing IoT devices through remote access. By following the steps outlined, users can establish a secure connection to their IoT devices, ensuring data integrity and privacy.
We encourage readers to share their experiences and ask questions in the comments section below. Additionally, explore other articles on our site for more insights into IoT security and best practices.
References: