Experiencing issues with your RemoteIoT platform SSH key not working can be frustrating, especially when managing remote devices or servers. SSH keys play a vital role in secure and efficient communication between systems. However, problems with SSH keys can disrupt workflows and compromise security. Understanding the root cause of the issue and learning how to resolve it is essential for IT professionals and system administrators.
SSH (Secure Shell) keys are cryptographic keys that allow users to authenticate securely to remote servers without using passwords. When these keys stop functioning, it can lead to significant operational challenges. In this article, we will explore common reasons why RemoteIoT platform SSH keys may fail and provide actionable solutions to fix the issue.
Whether you're troubleshooting SSH keys for the first time or looking to enhance your knowledge of secure remote access, this guide will help you identify and resolve problems effectively. Let’s dive into the details and ensure your RemoteIoT platform runs smoothly.
Read also:Hdhub4u In Movie Hindi Your Ultimate Guide To Streaming Bollywood Movies
Table of Contents
- Introduction to RemoteIoT Platform and SSH Keys
- Common Issues with SSH Keys
- Step-by-Step Troubleshooting for SSH Keys
- File Permissions and Ownership
- Proper SSH Key Generation
- SSH Configuration File Settings
- Network and Firewall Issues
- Software Updates and Compatibility
- Enhancing Security with SSH Keys
- Best Practices for Managing SSH Keys
- Conclusion and Call to Action
Introduction to RemoteIoT Platform and SSH Keys
The RemoteIoT platform is a powerful tool designed for managing and monitoring IoT devices remotely. It enables seamless communication between devices and servers, ensuring efficient data exchange and control. SSH keys are an integral part of this platform, providing secure authentication without the need for passwords.
SSH keys consist of a private key (kept secret) and a public key (shared with servers). When the RemoteIoT platform SSH key is not working, it often indicates a misconfiguration or security issue. Understanding how SSH keys function is the first step in resolving such problems.
Common Issues with SSH Keys
Incorrect Key Format
One common issue with SSH keys is incorrect formatting. The public key must be correctly formatted and placed in the authorized_keys file on the server. If the key is malformed, the server will reject the connection.
Key Mismatch
Another frequent problem is key mismatch, where the public key on the server does not match the private key on the client. This can occur if keys are regenerated or improperly copied.
Expired Keys
In some cases, SSH keys may expire, especially if they are time-limited. Ensuring that keys remain valid is crucial for uninterrupted access to the RemoteIoT platform.
Step-by-Step Troubleshooting for SSH Keys
When your RemoteIoT platform SSH key is not working, follow these steps to diagnose and fix the issue:
Read also:Mastering Remoteiot Vpc Ssh A Comprehensive Guide To Raspberry Pi And Windows 10 Integration
- Verify the SSH key pair on both the client and server.
- Check the authorized_keys file for proper formatting and content.
- Test the SSH connection using the verbose option (-v) to identify errors.
- Review server logs for any authentication-related messages.
File Permissions and Ownership
Correct File Permissions
File permissions are critical for SSH key functionality. The authorized_keys file and the .ssh directory must have the correct permissions to ensure secure access. Incorrect permissions can lead to authentication failures.
Ownership of Files
Ensure that the .ssh directory and its contents are owned by the correct user. Misaligned ownership can prevent the SSH daemon from reading the keys properly.
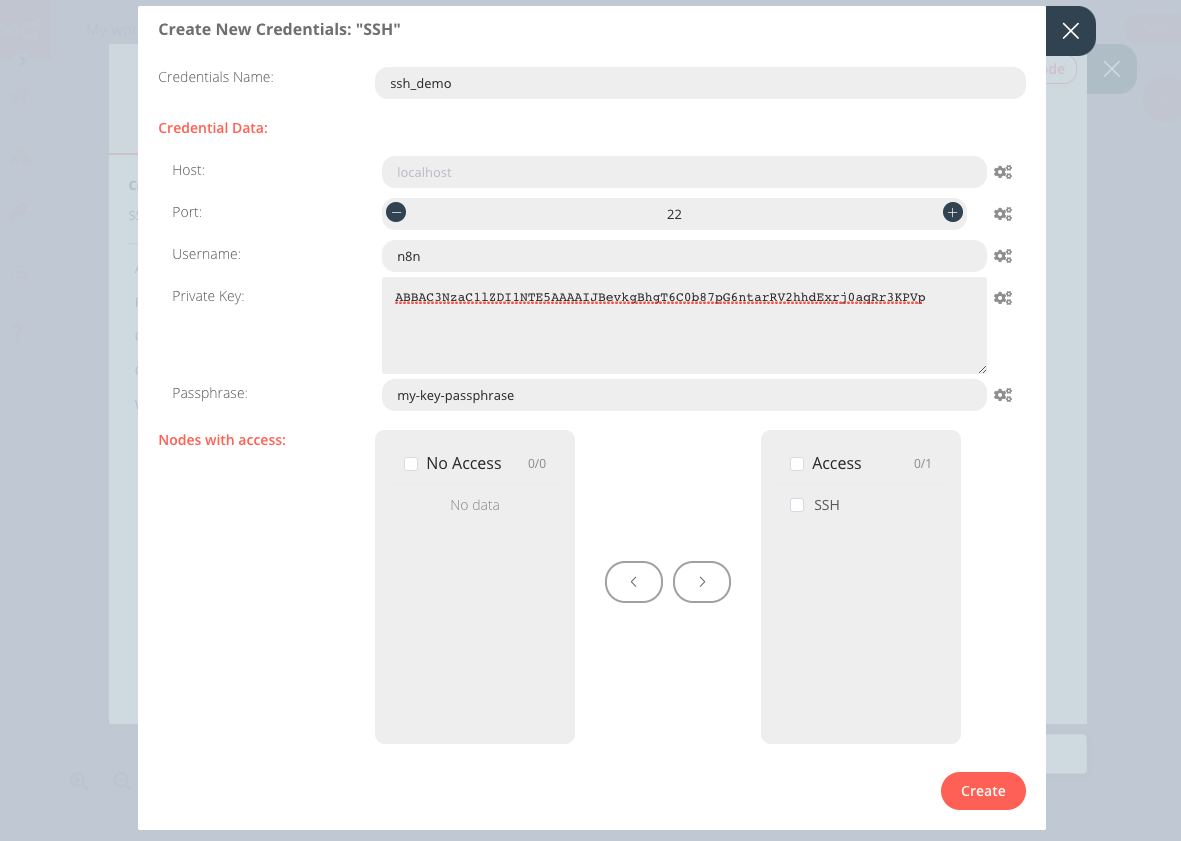
Proper SSH Key Generation
Generating SSH keys correctly is essential for their functionality. Use the following command to create a secure SSH key pair:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com"
This command generates a 4096-bit RSA key with a comment for easy identification.
SSH Configuration File Settings
Configuring SSH Client
The SSH client configuration file (~/.ssh/config) can be customized to simplify connections. Add entries for your RemoteIoT platform to streamline access:
Host remoteiot HostName your.remoteiot.server User yourusername IdentityFile ~/.ssh/your_key
Server Configuration
On the server side, ensure that the SSH daemon is configured to accept key-based authentication. Check the /etc/ssh/sshd_config file for the following settings:
- PubkeyAuthentication yes
- AuthorizedKeysFile .ssh/authorized_keys
Network and Firewall Issues
Firewall Rules
Firewall rules can block SSH connections, even if the keys are correctly configured. Ensure that the necessary ports (usually 22) are open and accessible.
Network Latency
High network latency can cause timeouts during SSH connections. Monitor network performance to rule out this issue.
Software Updates and Compatibility
Updating SSH Software
Regularly updating SSH software on both the client and server ensures compatibility and security. Outdated versions may not support modern key formats or algorithms.
Compatibility Issues
Sometimes, differences in SSH implementations between the client and server can cause issues. Verify that both systems are using compatible versions of OpenSSH or other SSH software.
Enhancing Security with SSH Keys
Two-Factor Authentication
Combine SSH keys with two-factor authentication for added security. This approach ensures that even if a key is compromised, unauthorized access remains difficult.
Key Revocation
Implement a key revocation strategy to quickly disable compromised keys. Regularly audit and update your list of authorized keys to maintain security.
Best Practices for Managing SSH Keys
Adopting best practices for SSH key management can prevent issues and enhance security:
- Use strong, unique keys for each user or device.
- Regularly rotate SSH keys to minimize the risk of compromise.
- Limit the use of passphrase-less keys to trusted environments.
- Monitor key usage and access logs for suspicious activity.
Conclusion and Call to Action
In conclusion, resolving issues with your RemoteIoT platform SSH key not working requires a systematic approach. By understanding common problems, following troubleshooting steps, and implementing best practices, you can ensure secure and reliable access to your systems.
We encourage you to share your experiences and solutions in the comments below. Additionally, explore other articles on our site for more insights into IoT security and management. Together, we can build a safer and more efficient digital ecosystem.
References:
- OpenSSH Documentation: https://www.openssh.com/
- SSH Key Management Best Practices: https://www.ssh.com/academy/ssh/key-management
- RemoteIoT Platform Documentation: https://remoteiot.com/docs