As the world becomes increasingly interconnected, the Internet of Things (IoT) continues to play a pivotal role in transforming how we interact with devices and systems. One of the most sought-after solutions for IoT enthusiasts and professionals is the use of remote IoT platforms combined with secure SSH keys on Raspberry Pi devices. This powerful combination not only enhances device management but also ensures robust security measures are in place.
The integration of remote IoT platforms with Raspberry Pi has revolutionized how users can monitor, control, and automate their IoT setups from anywhere in the world. By leveraging SSH keys, users can establish secure, encrypted connections that protect sensitive data and prevent unauthorized access. This article dives deep into the best remote IoT platforms that work seamlessly with SSH keys on Raspberry Pi, offering practical tips and actionable insights for users at all levels.
Whether you're a beginner exploring the possibilities of IoT or an experienced developer looking to enhance your projects, this guide will equip you with the knowledge and tools needed to make informed decisions. From understanding the fundamentals of SSH keys to exploring top-tier platforms, we'll cover everything you need to know to maximize the potential of your Raspberry Pi-based IoT projects.
Read also:Desiremovies Movies Bollywood Your Ultimate Guide To Bollywood Cinema
Understanding the Role of SSH Keys in IoT
SSH (Secure Shell) keys are cryptographic keys used to authenticate secure connections between devices. In the context of IoT, SSH keys play a critical role in ensuring that communication between devices remains secure and tamper-proof. When paired with Raspberry Pi, SSH keys provide an added layer of security by eliminating the need for password-based authentication, which is often vulnerable to brute-force attacks.
Why SSH Keys Are Essential for IoT Security
- SSH keys eliminate the risk of password-based vulnerabilities.
- They ensure encrypted communication between devices, making it difficult for attackers to intercept sensitive data.
- SSH keys are easy to implement and manage, even for beginners.
How SSH Keys Work with Raspberry Pi
Setting up SSH keys on Raspberry Pi involves generating a public-private key pair. The public key is shared with the server or device you want to connect to, while the private key remains securely stored on your Raspberry Pi. Once configured, you can establish secure connections without needing to enter passwords repeatedly.
Best RemoteIoT Platforms for Raspberry Pi
Choosing the right remote IoT platform is crucial for ensuring seamless connectivity and efficient device management. Below, we explore some of the best platforms available for Raspberry Pi users, focusing on their compatibility with SSH keys and overall functionality.
1. PlatformIO
PlatformIO is a versatile IoT development platform that supports multiple programming languages and frameworks. It offers seamless integration with Raspberry Pi and provides robust tools for managing IoT projects. With built-in support for SSH, PlatformIO ensures secure connections and easy device management.
2. ThingsBoard
ThingsBoard is an open-source IoT platform designed for scalable and secure device management. It supports SSH-based connections, making it an ideal choice for Raspberry Pi users who prioritize security. The platform also offers advanced analytics and visualization tools, enabling users to monitor and analyze IoT data effectively.
3. Ubidots
Ubidots is a cloud-based IoT platform that simplifies the process of building and managing IoT applications. It offers seamless integration with Raspberry Pi and supports SSH-based authentication for secure device connections. With its user-friendly interface and extensive documentation, Ubidots is perfect for both beginners and experienced developers.
Read also:5movierulz Telugu 2025 Your Ultimate Guide To Telugu Movies And Beyond
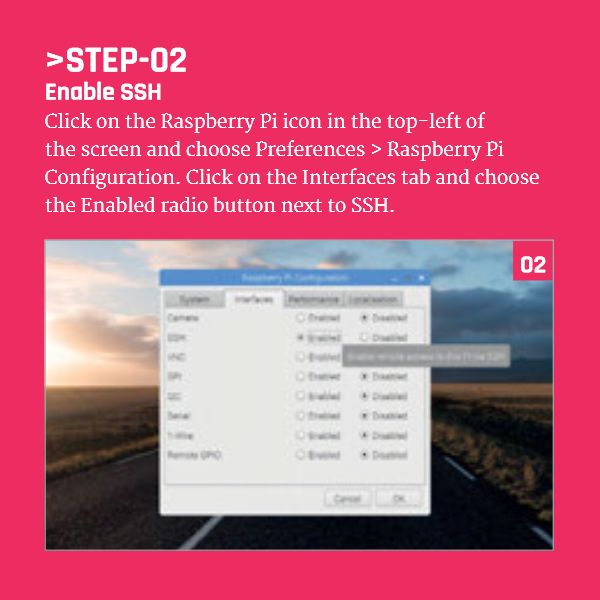
Setting Up SSH Keys on Raspberry Pi
Configuring SSH keys on your Raspberry Pi is a straightforward process that involves a few simple steps. Below, we outline the process to help you set up SSH keys effectively.
Step-by-Step Guide to Generating SSH Keys
- Open the terminal on your Raspberry Pi.
- Run the command
ssh-keygento generate a key pair. - Follow the prompts to specify a file location and passphrase (optional).
- Copy the public key to the server or device you want to connect to using the
ssh-copy-idcommand.
Common Issues and Solutions
- Problem: SSH connection fails due to incorrect key permissions.
Solution: Ensure the private key file has the correct permissions by runningchmod 600 ~/.ssh/id_rsa. - Problem: Public key not recognized by the server.
Solution: Verify that the public key has been correctly added to the server's authorized_keys file.
Top Features of Leading RemoteIoT Platforms
When evaluating remote IoT platforms for use with Raspberry Pi, it's essential to consider the features they offer. Below, we highlight the key features of some of the top platforms in the market.
Data Analytics and Visualization
Platforms like ThingsBoard and Ubidots excel in providing advanced analytics and visualization tools. These features enable users to gain deeper insights into their IoT data, helping them make informed decisions.
Scalability and Flexibility
PlatformIO stands out for its scalability and flexibility, supporting a wide range of programming languages and frameworks. This makes it an ideal choice for developers working on complex IoT projects.
Security and Authentication
All leading remote IoT platforms prioritize security, offering robust authentication mechanisms such as SSH keys. This ensures that devices remain secure and protected from unauthorized access.
Comparing Popular RemoteIoT Platforms
Choosing the right platform depends on your specific needs and requirements. Below, we compare some of the most popular remote IoT platforms based on key criteria.
Platform Comparison Table
| Platform | Key Features | SSH Support | Cost |
|---|---|---|---|
| PlatformIO | Versatile, supports multiple languages | Yes | Free |
| ThingsBoard | Advanced analytics, open-source | Yes | Free (open-source), paid options available |
| Ubidots | User-friendly interface, cloud-based | Yes | Free trial, paid plans |
Best Practices for Using SSH Keys with Raspberry Pi
To ensure optimal performance and security when using SSH keys with Raspberry Pi, it's important to follow best practices. Below, we outline some key tips to help you get the most out of this powerful combination.
1. Use Strong Passphrases
While not mandatory, using a passphrase for your private key adds an extra layer of security. This ensures that even if your private key is compromised, attackers won't be able to use it without the passphrase.
2. Regularly Update Software
Keeping your Raspberry Pi's software up to date is crucial for maintaining security. Regular updates ensure that any vulnerabilities are patched, reducing the risk of attacks.
3. Limit Access to Authorized Devices
Restrict SSH access to only those devices that require it. This minimizes the attack surface and ensures that unauthorized devices cannot connect to your Raspberry Pi.
Security Considerations for RemoteIoT Platforms
When using remote IoT platforms, security should always be a top priority. Below, we discuss some key considerations to keep in mind.
Data Encryption
All data transmitted between devices should be encrypted to prevent interception by attackers. Ensure that the platform you choose supports end-to-end encryption for maximum security.
Regular Audits and Monitoring
Conducting regular security audits and monitoring your IoT setup can help identify and address potential vulnerabilities before they are exploited.
Future Trends in RemoteIoT Platforms
The field of remote IoT platforms is evolving rapidly, with new technologies and innovations emerging regularly. Below, we explore some of the key trends shaping the future of this space.
Edge Computing
Edge computing is gaining traction as a way to reduce latency and improve performance in IoT setups. By processing data closer to the source, edge computing enables faster decision-making and reduces reliance on cloud-based solutions.
AI and Machine Learning Integration
AI and machine learning are increasingly being integrated into remote IoT platforms to enhance functionality and improve user experiences. These technologies enable platforms to learn from data and make predictions, providing valuable insights to users.
Conclusion
In conclusion, the combination of remote IoT platforms and SSH keys on Raspberry Pi offers a powerful solution for managing and securing IoT projects. By understanding the fundamentals of SSH keys and exploring the best platforms available, users can create robust, secure setups that meet their specific needs.
We encourage readers to take action by experimenting with the platforms and techniques discussed in this article. Whether you're a beginner or an experienced developer, there's always something new to learn and explore in the world of IoT. Don't forget to share your thoughts and experiences in the comments section below, and consider exploring other articles on our site for more insights into IoT and related technologies.
Table of Contents
- Understanding the Role of SSH Keys in IoT
- Best RemoteIoT Platforms for Raspberry Pi
- Setting Up SSH Keys on Raspberry Pi
- Top Features of Leading RemoteIoT Platforms
- Comparing Popular RemoteIoT Platforms
- Best Practices for Using SSH Keys with Raspberry Pi
- Security Considerations for RemoteIoT Platforms
- Future Trends in RemoteIoT Platforms
- Conclusion