Connecting remotely to your IoT devices using SSH is essential for managing and maintaining them effectively. Whether you're a hobbyist or a professional, securing your IoT network is paramount. This guide will walk you through the steps to securely connect your Raspberry Pi for free, ensuring your data remains protected while enabling seamless remote access.
In today's interconnected world, the Internet of Things (IoT) has become a cornerstone of innovation. From smart homes to industrial automation, IoT devices are transforming the way we live and work. However, with this convenience comes the responsibility to secure these devices against potential threats.
This article is designed to provide comprehensive guidance on securely connecting remote IoT devices using peer-to-peer (P2P) SSH on a Raspberry Pi without any subscription fees. By the end, you'll have the knowledge and tools necessary to protect your network and enjoy hassle-free remote access.
Read also:5 Movierulz 2025 Telugu Your Ultimate Guide To Telugu Movies
Table of Contents
- Introduction to IoT and SSH
- Raspberry Pi Basics
- Understanding P2P SSH
- Steps to Securely Connect IoT Devices
- Free Tools for Remote Access
- Best Practices for Security
- Troubleshooting Common Issues
- Data Protection Techniques
- Cost-Effectiveness of Free Solutions
- Future Trends in IoT Security
- Conclusion
Introduction to IoT and SSH
Why IoT Security Matters
The Internet of Things (IoT) has revolutionized the way we interact with technology. However, as more devices connect to the internet, the risk of cyberattacks increases. SSH (Secure Shell) plays a vital role in securing these connections by encrypting data transmitted between devices.
Keyword: Securely connect remote IoT devices using SSH ensures that unauthorized access is minimized, protecting sensitive information from malicious actors.
Raspberry Pi Basics
What Is Raspberry Pi?
The Raspberry Pi is a low-cost, credit-card-sized computer that has gained immense popularity among hobbyists and professionals alike. Its versatility makes it an ideal platform for experimenting with IoT projects.
Some key features of the Raspberry Pi include:
- Compact and affordable design
- Support for multiple operating systems
- Wide range of GPIO pins for hardware integration
Understanding P2P SSH
What Is P2P SSH?
Peer-to-peer (P2P) SSH allows direct communication between two devices without the need for a central server. This method enhances security by reducing the number of intermediaries involved in the connection process.
Using P2P SSH for remote IoT connections provides several advantages, including:
Read also:Bolly4u Org Your Ultimate Guide To Bollywood Movies And Entertainment
- Enhanced security through direct links
- Reduced latency and improved performance
- Lower costs compared to traditional server-based solutions
Steps to Securely Connect IoT Devices
Setting Up SSH on Raspberry Pi
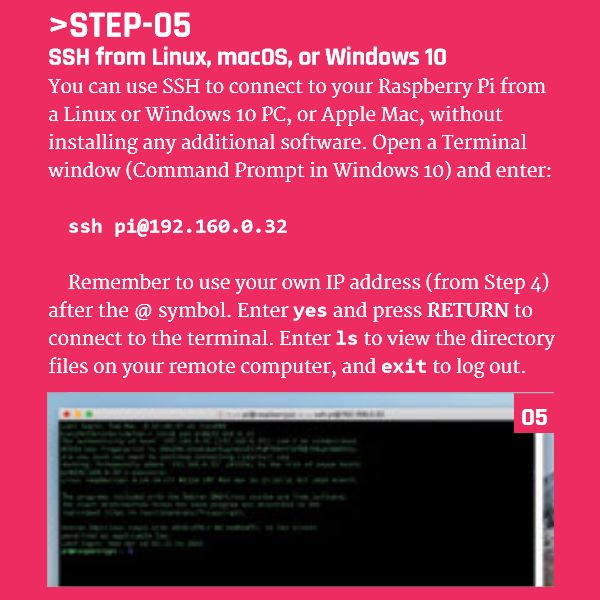
Configuring SSH on your Raspberry Pi is a straightforward process. Follow these steps to get started:
- Install the latest version of Raspberry Pi OS on your device.
- Enable SSH by creating an empty file named "ssh" in the boot directory.
- Connect your Raspberry Pi to the internet and note its IP address.
Securing Your Connection
To ensure the security of your remote IoT P2P SSH connection, consider implementing the following measures:
- Use strong, unique passwords or public key authentication.
- Disable root login to prevent unauthorized access.
- Regularly update your operating system and software.
Free Tools for Remote Access
Exploring Open Source Solutions
Several free tools are available to facilitate remote access to your Raspberry Pi. Some popular options include:
- OpenSSH: A widely-used SSH server and client.
- Tailscale: A secure, easy-to-use mesh networking solution.
- ngrok: A tool for creating secure tunnels to local servers.
These tools enable you to securely connect to your Raspberry Pi without incurring subscription fees, making them ideal for budget-conscious users.
Best Practices for Security
Implementing Strong Authentication
Using strong authentication methods is crucial for protecting your remote IoT connections. Consider the following best practices:
- Enable two-factor authentication (2FA) whenever possible.
- Limit login attempts to prevent brute-force attacks.
- Regularly review and update your security policies.
Monitoring Network Activity
Regularly monitoring network activity can help identify potential security threats. Tools like fail2ban and log2ram can assist in detecting and mitigating suspicious behavior.
Troubleshooting Common Issues
Connection Problems
If you encounter issues while setting up your remote IoT P2P SSH connection, consider the following troubleshooting steps:
- Verify that SSH is enabled on your Raspberry Pi.
- Check your network configuration and ensure proper IP assignment.
- Test connectivity using tools like ping or telnet.
Security Alerts
Receiving security alerts can be alarming, but they often indicate potential vulnerabilities in your setup. Address these alerts promptly by:
- Updating your software and firmware.
- Reviewing your firewall rules and access controls.
- Consulting documentation or seeking support from online communities.
Data Protection Techniques
Encrypting Sensitive Information
Data encryption is a critical component of securing your remote IoT connections. Implement encryption protocols like AES or TLS to safeguard sensitive data during transmission.
Additionally, consider using secure storage solutions such as VeraCrypt or LUKS to protect data at rest.
Cost-Effectiveness of Free Solutions
Evaluating Free vs. Paid Options
While paid solutions may offer additional features, free tools like OpenSSH and Tailscale provide robust functionality for most users. By leveraging these resources, you can achieve secure, reliable remote IoT P2P SSH connections without breaking the bank.
When assessing cost-effectiveness, consider factors such as:
- Initial setup and configuration complexity.
- Ongoing maintenance and support requirements.
- Scalability for future expansion.
Future Trends in IoT Security
Emerging Technologies
The field of IoT security is rapidly evolving, with new technologies emerging to address existing challenges. Some promising developments include:
- Blockchain-based authentication systems.
- AI-driven threat detection and response mechanisms.
- Quantum-resistant encryption algorithms.
Staying informed about these trends will help you adapt your strategies and ensure the long-term security of your remote IoT P2P SSH connections.
Conclusion
In conclusion, securely connecting remote IoT devices using P2P SSH on a Raspberry Pi is both achievable and cost-effective. By following the steps outlined in this guide and adhering to best practices, you can protect your network and enjoy seamless remote access.
We encourage you to share your thoughts and experiences in the comments below. Additionally, explore our other articles for more insights into IoT security and related topics. Together, let's build a safer, smarter connected world!