RemoteIoT VPC SSH AWS has become a pivotal topic in the world of cloud computing and IoT deployment. Organizations are increasingly adopting Amazon Web Services (AWS) to manage their IoT devices securely and efficiently. By leveraging VPC and SSH, businesses can ensure robust network security and seamless device communication. This article delves into the intricacies of remote IoT management on AWS, providing you with the tools and knowledge to enhance your cloud infrastructure.
In today's rapidly evolving technological landscape, managing IoT devices remotely is not just a convenience—it’s a necessity. With the proliferation of connected devices, ensuring secure communication between devices and the cloud has never been more critical. This guide aims to provide a comprehensive overview of how to set up and manage RemoteIoT VPC SSH AWS environments effectively.
Whether you're a seasoned IT professional or someone new to the world of cloud computing, this article will walk you through the essential steps to secure your IoT infrastructure using AWS Virtual Private Cloud (VPC) and SSH protocols. Let's dive in and explore how you can optimize your IoT deployments.
Read also:Kylie Jenner Dob Exploring The Life And Journey Of A Global Icon
Table of Contents:
- Introduction to VPC
- RemoteIoT Basics
- AWS SSH Overview
- VPC and SSH Integration
- Securing IoT Devices
- Best Practices for RemoteIoT VPC SSH AWS
- Troubleshooting Common Issues
- Scalability Options
- Case Studies
- Conclusion
Introduction to VPC
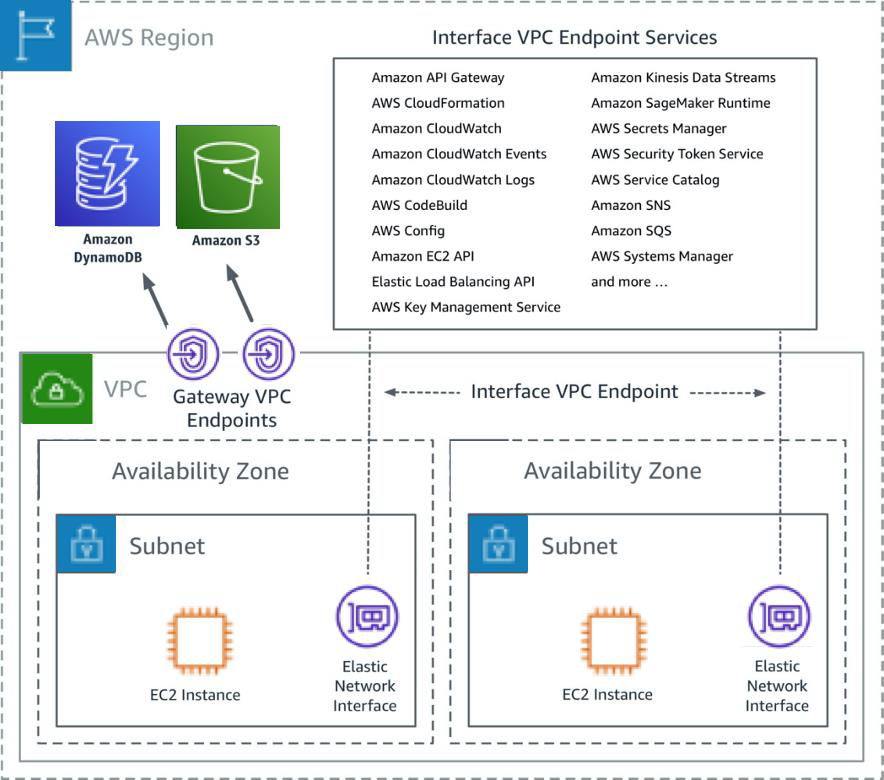
Amazon Virtual Private Cloud (VPC) is a fundamental component of AWS that allows users to create an isolated section of the AWS Cloud. This isolated section can be customized to meet specific network requirements, making it ideal for RemoteIoT VPC SSH AWS setups.
Key Features of VPC
VPC offers several features that make it indispensable for secure IoT deployments:
- Private Subnets: These subnets ensure that your IoT devices remain isolated from the public internet, enhancing security.
- Public Subnets: Public subnets allow devices to communicate with the internet when necessary, while still maintaining control over access.
- Security Groups: These act as virtual firewalls to control inbound and outbound traffic to your instances.
- Network Access Control Lists (NACLs): NACLs provide an additional layer of security by controlling traffic at the subnet level.
VPC is designed to support the stringent security requirements of RemoteIoT VPC SSH AWS environments, ensuring that your data remains secure while allowing for flexible connectivity options.
RemoteIoT Basics
Understanding the basics of RemoteIoT is crucial for anyone looking to implement a secure AWS environment. RemoteIoT involves managing IoT devices from a central location, often using cloud-based services like AWS.
Core Components of RemoteIoT
- IoT Devices: These can range from simple sensors to complex machinery, all connected to the internet.
- Cloud Platforms: Platforms like AWS provide the infrastructure needed to manage and process data from IoT devices.
- Communication Protocols: Protocols such as MQTT, HTTP, and SSH enable secure and efficient communication between devices and the cloud.
By integrating RemoteIoT with VPC and SSH, you can create a secure and scalable environment for managing IoT devices.
Read also:Remoteiot Ssh Aws Example A Comprehensive Guide For Secure Iot Connections
AWS SSH Overview
SSH, or Secure Shell, is a cryptographic network protocol that allows secure communication over unsecured networks. When combined with AWS, SSH becomes a powerful tool for managing RemoteIoT VPC SSH AWS environments.
Benefits of Using SSH with AWS
- Encrypted Communication: SSH ensures that all data transmitted between devices and the cloud is encrypted, protecting sensitive information.
- Authentication: SSH supports various authentication methods, including public key authentication, enhancing security.
- Remote Management: With SSH, you can remotely manage your IoT devices and AWS instances securely.
Implementing SSH in your AWS environment is a key step in securing your RemoteIoT deployments.
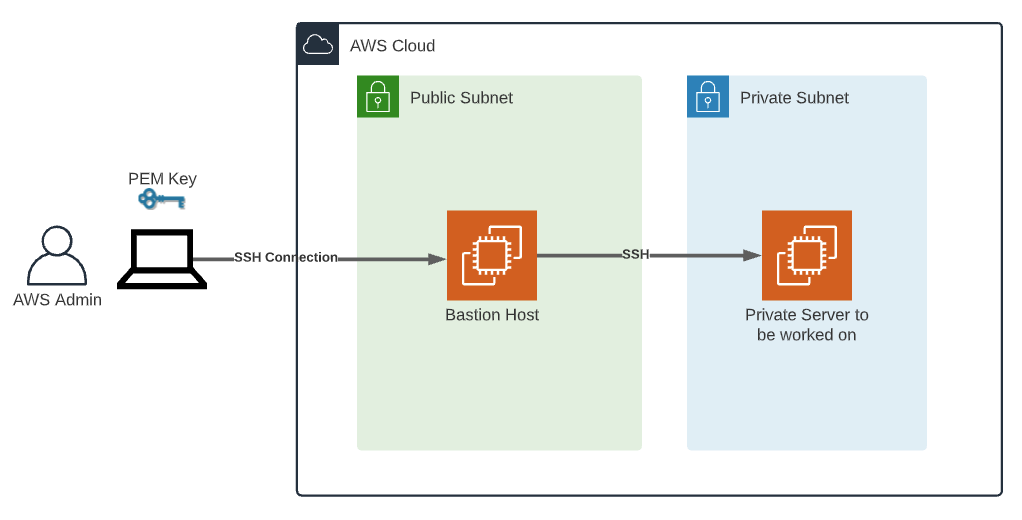
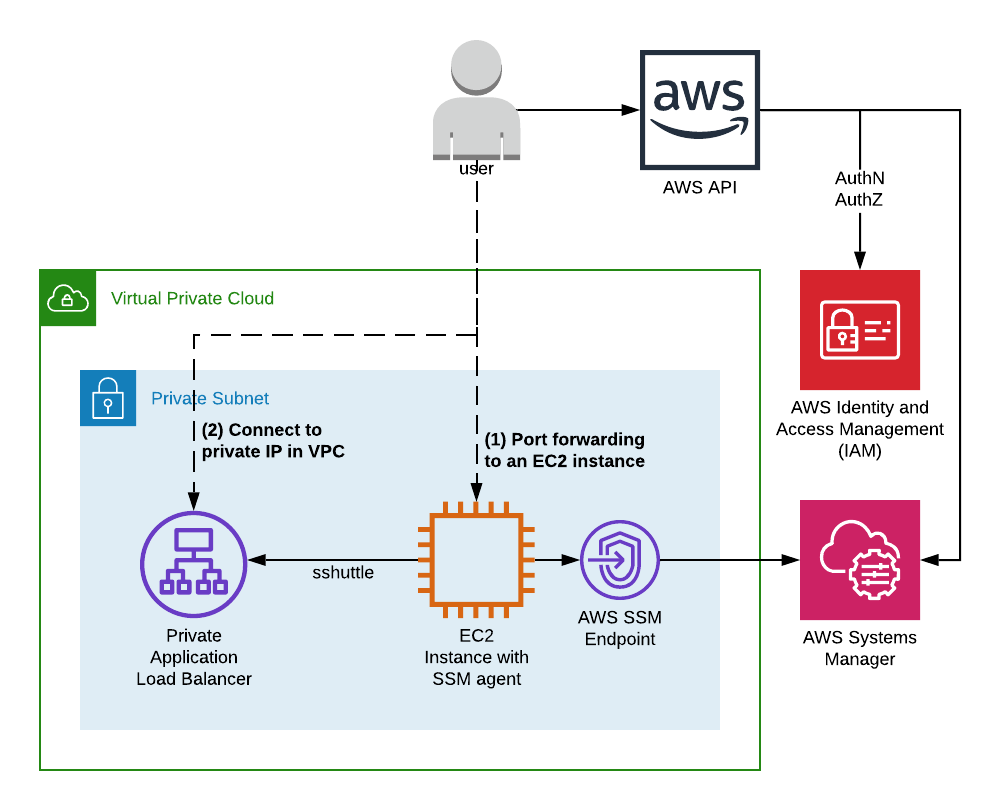
VPC and SSH Integration
Integrating VPC with SSH in AWS allows for a highly secure and efficient RemoteIoT setup. This integration involves configuring VPC settings to work seamlessly with SSH protocols.
Steps to Integrate VPC and SSH
- Create a VPC: Start by setting up a VPC in your AWS account, defining subnets and IP ranges.
- Configure Security Groups: Set up security groups to allow SSH access from specific IP addresses.
- Set Up SSH Keys: Generate and configure SSH keys for secure access to your instances.
By following these steps, you can create a secure environment for managing IoT devices using RemoteIoT VPC SSH AWS.
Securing IoT Devices
Securing IoT devices is paramount in any RemoteIoT VPC SSH AWS setup. This involves implementing various security measures to protect devices and the data they transmit.
Security Measures for IoT Devices
- Data Encryption: Encrypt data both in transit and at rest to prevent unauthorized access.
- Regular Updates: Keep firmware and software up to date to protect against vulnerabilities.
- Access Control: Implement strict access control policies to ensure only authorized users can interact with devices.
These measures, combined with VPC and SSH, create a robust security framework for IoT deployments.
Best Practices for RemoteIoT VPC SSH AWS
To ensure the success of your RemoteIoT VPC SSH AWS setup, it's essential to follow best practices in cloud computing and IoT security.
Top Best Practices
- Regular Audits: Conduct regular security audits to identify and address potential vulnerabilities.
- Monitoring and Logging: Implement monitoring and logging to track activity and detect anomalies.
- Compliance: Ensure your setup complies with relevant regulations and standards, such as GDPR or HIPAA.
By adhering to these best practices, you can maintain a secure and compliant RemoteIoT environment.
Troubleshooting Common Issues
Even with the best planning, issues can arise in RemoteIoT VPC SSH AWS setups. Understanding common problems and how to resolve them is crucial for maintaining a stable environment.
Common Issues and Solutions
- SSH Connection Failures: Ensure that security groups and NACLs allow SSH traffic and that SSH keys are correctly configured.
- Network Connectivity Issues: Check VPC settings and ensure that subnets are properly configured.
- Device Malfunctions: Regularly monitor device health and update firmware to prevent malfunctions.
Addressing these issues promptly can prevent downtime and ensure the smooth operation of your IoT infrastructure.
Scalability Options
As your IoT deployment grows, it's important to consider scalability options that allow your RemoteIoT VPC SSH AWS environment to expand without compromising security or performance.
Scalability Strategies
- Auto Scaling: Implement auto-scaling policies to automatically adjust resources based on demand.
- Load Balancing: Use load balancers to distribute traffic evenly across instances, improving performance.
- Multi-Region Deployments: Deploy resources across multiple AWS regions to enhance redundancy and availability.
These strategies ensure that your RemoteIoT setup can grow alongside your business needs.
Case Studies
Examining real-world case studies can provide valuable insights into how organizations successfully implement RemoteIoT VPC SSH AWS solutions.
Case Study: Smart City IoT Deployment
A major city implemented a smart city IoT deployment using RemoteIoT VPC SSH AWS. By leveraging VPC for isolation and SSH for secure communication, the city was able to manage thousands of IoT devices efficiently, improving public services and reducing costs.
Such case studies highlight the practical applications and benefits of RemoteIoT VPC SSH AWS setups.
Conclusion
In conclusion, mastering RemoteIoT VPC SSH AWS requires a thorough understanding of cloud computing principles and IoT security best practices. By following the guidelines outlined in this article, you can create a secure, scalable, and efficient environment for managing IoT devices.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, consider exploring other articles on our site for more insights into cloud computing and IoT technologies. Together, let's build a more connected and secure future.