In the ever-evolving world of technology, RemoteIoT SSH AWS Example plays a crucial role in enabling secure and efficient communication between Internet of Things (IoT) devices and cloud-based systems. The integration of IoT with AWS services opens up a world of possibilities, empowering businesses to optimize their operations, improve data management, and enhance security. Whether you're a developer, an IT professional, or simply someone interested in the intersection of IoT and cloud computing, this article will provide you with all the information you need to understand and implement this powerful solution.
As IoT continues to expand its reach across industries, ensuring secure and reliable communication between devices has become paramount. This is where RemoteIoT SSH AWS Example comes into play. By leveraging AWS's robust infrastructure, businesses can establish encrypted connections, manage large-scale IoT deployments, and monitor device performance in real time. This guide will delve into the technical aspects of setting up a remote IoT system using SSH and AWS, while also addressing potential challenges and best practices.
Whether you're looking to enhance your existing IoT infrastructure or build a new one from scratch, understanding the intricacies of RemoteIoT SSH AWS Example is essential. In this article, we will explore the step-by-step process of configuring SSH on AWS for IoT devices, discuss security considerations, and provide practical examples to help you implement this solution effectively. Let's dive in!
Read also:5movierulz 2025 The Ultimate Guide To Downloading Kannada Movies
Table of Contents
- What is RemoteIoT SSH AWS?
- Benefits of Using RemoteIoT SSH AWS
- Setting Up RemoteIoT SSH on AWS
- Securing Your RemoteIoT SSH AWS
- Common Issues and Troubleshooting
- Best Practices for RemoteIoT SSH AWS
- Real-World Examples of RemoteIoT SSH AWS
- Scaling RemoteIoT SSH AWS Deployments
- Future Trends in RemoteIoT SSH AWS
- Conclusion and Next Steps
What is RemoteIoT SSH AWS?
RemoteIoT SSH AWS refers to the practice of securely connecting IoT devices to Amazon Web Services (AWS) using the SSH (Secure Shell) protocol. This approach ensures that data transmitted between devices and cloud servers remains encrypted and protected from unauthorized access. By leveraging AWS's extensive suite of services, businesses can build scalable and reliable IoT infrastructures that meet their specific needs.
SSH is a cryptographic network protocol that facilitates secure communication over unsecured networks. When combined with AWS, it enables IoT devices to connect to cloud-based servers while maintaining high levels of security. This is particularly important in industries such as healthcare, finance, and manufacturing, where data integrity and confidentiality are critical.
In this section, we will explore the fundamental concepts of RemoteIoT SSH AWS, including its architecture, key components, and how it integrates with other AWS services like AWS IoT Core and Amazon EC2.
Benefits of Using RemoteIoT SSH AWS
Implementing RemoteIoT SSH AWS offers numerous advantages for businesses looking to enhance their IoT capabilities. Below are some of the key benefits:
- Enhanced Security: SSH ensures that all data transmitted between IoT devices and AWS servers is encrypted, reducing the risk of data breaches and cyberattacks.
- Scalability: AWS's cloud infrastructure allows businesses to easily scale their IoT deployments as their needs grow, without compromising performance.
- Cost Efficiency: By leveraging AWS's pay-as-you-go pricing model, businesses can optimize their costs and only pay for the resources they use.
- Reliability: AWS provides robust infrastructure and tools to ensure that IoT systems remain operational even in the face of unexpected disruptions.
- Global Reach: With AWS's extensive network of data centers, businesses can deploy IoT systems globally, ensuring low-latency communication and improved user experience.
These benefits make RemoteIoT SSH AWS an attractive solution for organizations seeking to harness the power of IoT while maintaining security and efficiency.
Setting Up RemoteIoT SSH on AWS
Step 1: AWS Account Setup
Before you can begin configuring RemoteIoT SSH on AWS, you need to set up an AWS account. Follow these steps to get started:
Read also:Hdhub4u Download All Bollywood Movies Your Ultimate Guide
- Visit the AWS website and sign up for a free account.
- Complete the registration process by providing your contact and payment information.
- Once your account is activated, log in to the AWS Management Console.
With your account set up, you can now proceed to the next step.
Step 2: Configure SSH Keys
Configuring SSH keys is a critical step in ensuring secure communication between IoT devices and AWS servers. Follow these steps to generate and configure SSH keys:
- Open the AWS Management Console and navigate to the EC2 Dashboard.
- Click on "Key Pairs" under the "Network & Security" section.
- Create a new key pair by clicking "Create Key Pair" and downloading the private key file.
- Store the private key file in a secure location and ensure it is only accessible to authorized users.
By following these steps, you can establish a secure foundation for your RemoteIoT SSH AWS deployment.
Securing Your RemoteIoT SSH AWS
Security is a top priority when implementing RemoteIoT SSH AWS. Below are some best practices to ensure the security of your IoT infrastructure:
- Use Strong Passwords: Ensure that all user accounts associated with your AWS environment have strong, complex passwords.
- Enable Multi-Factor Authentication (MFA): Add an extra layer of security by enabling MFA for all AWS accounts.
- Regularly Update Software: Keep all IoT devices and AWS services up to date with the latest security patches and updates.
- Monitor Activity Logs: Use AWS CloudTrail to monitor and analyze activity logs for potential security threats.
- Restrict Access: Limit access to your AWS environment to only those who need it, using IAM roles and policies.
By adhering to these practices, you can significantly reduce the risk of security breaches and protect your IoT infrastructure.
Common Issues and Troubleshooting
Despite careful planning and implementation, issues may arise when setting up RemoteIoT SSH AWS. Below are some common problems and their solutions:
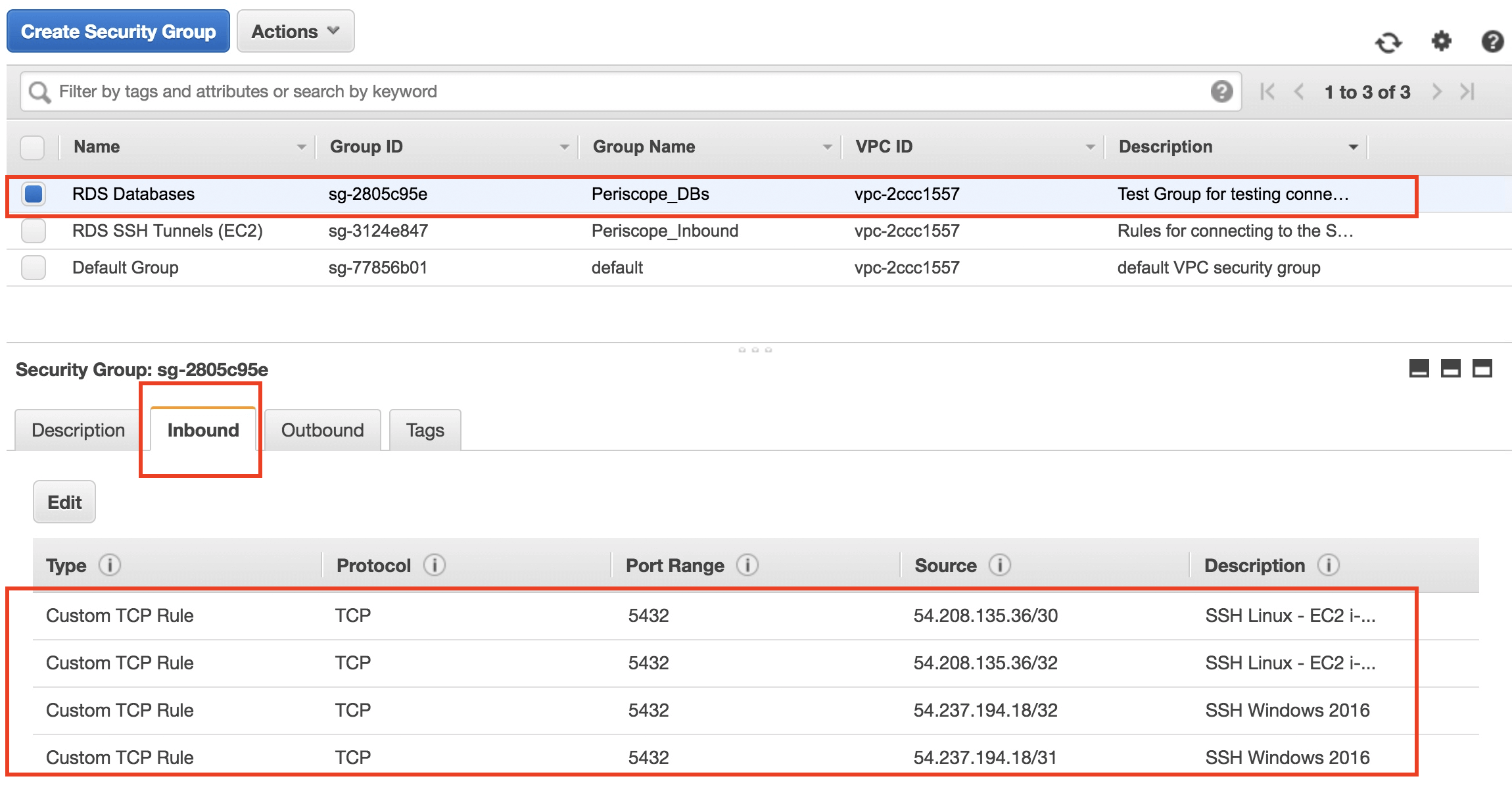
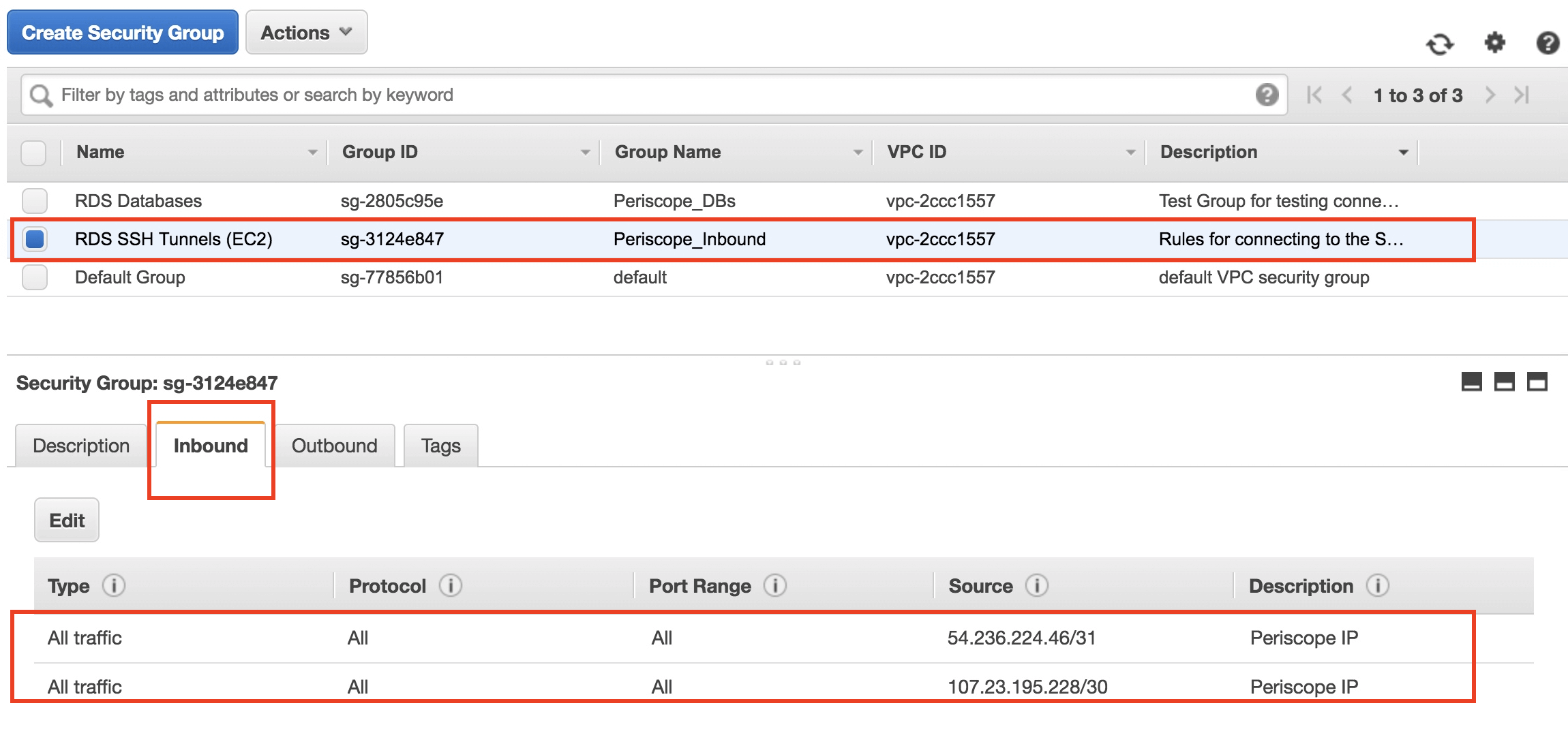
- Connection Errors: Ensure that your SSH keys are correctly configured and that the necessary ports are open in your AWS security group.
- Performance Issues: Monitor your IoT devices and AWS resources for bottlenecks and optimize your infrastructure accordingly.
- Authentication Failures: Verify that your SSH keys and user credentials are correct and that MFA is properly configured.
For more detailed troubleshooting, refer to the AWS Documentation or consult with AWS support.
Best Practices for RemoteIoT SSH AWS
To maximize the effectiveness of your RemoteIoT SSH AWS deployment, consider the following best practices:
- Plan Your Architecture: Design your IoT infrastructure with scalability and security in mind, ensuring that it can grow with your business needs.
- Automate Processes: Use AWS services like AWS Lambda and AWS IoT Core to automate routine tasks and reduce manual intervention.
- Monitor Performance: Regularly monitor your IoT devices and AWS resources to identify and address any issues promptly.
- Document Procedures: Maintain comprehensive documentation of your setup and configuration processes for future reference.
By following these best practices, you can ensure the success of your RemoteIoT SSH AWS implementation.
Real-World Examples of RemoteIoT SSH AWS
Several organizations have successfully implemented RemoteIoT SSH AWS to enhance their IoT capabilities. Below are some real-world examples:
- Smart Agriculture: Farmers use IoT sensors connected to AWS via SSH to monitor soil moisture levels and optimize irrigation systems.
- Remote Healthcare: Medical devices in remote locations securely transmit patient data to cloud servers using SSH, enabling real-time monitoring and analysis.
- Industrial Automation: Manufacturers leverage IoT and AWS to monitor and control production processes, improving efficiency and reducing downtime.
These examples demonstrate the versatility and power of RemoteIoT SSH AWS in various industries.
Scaling RemoteIoT SSH AWS Deployments
As your IoT infrastructure grows, it's essential to scale your RemoteIoT SSH AWS deployment to meet increasing demands. Below are some strategies for scaling effectively:
- Use Auto Scaling: Implement AWS Auto Scaling to automatically adjust the number of EC2 instances based on demand.
- Optimize Resource Usage: Regularly review and optimize your resource usage to ensure cost efficiency.
- Implement Load Balancing: Use AWS Elastic Load Balancer to distribute traffic evenly across your IoT devices and servers.
By following these strategies, you can ensure that your RemoteIoT SSH AWS deployment remains scalable and efficient.
Future Trends in RemoteIoT SSH AWS
The future of RemoteIoT SSH AWS looks promising, with several trends expected to shape its evolution:
- Edge Computing: The integration of edge computing with IoT and AWS will enable faster data processing and reduced latency.
- Artificial Intelligence: AI-powered analytics will enhance the capabilities of IoT systems, providing deeper insights and predictive capabilities.
- Quantum Computing: Advances in quantum computing may lead to breakthroughs in encryption and security for IoT devices.
These trends will continue to drive innovation in the field of IoT and cloud computing, offering exciting possibilities for the future.
Conclusion and Next Steps
In conclusion, RemoteIoT SSH AWS provides a powerful and secure solution for connecting IoT devices to cloud-based systems. By following the guidelines and best practices outlined in this article, you can successfully implement and scale your IoT infrastructure while ensuring optimal security and performance.
We encourage you to take the next steps by experimenting with AWS services and exploring the possibilities of RemoteIoT SSH AWS. Feel free to leave a comment below if you have any questions or would like to share your experiences. Additionally, don't forget to check out our other articles for more insights into IoT and cloud computing.