In today's interconnected world, securely connecting remote IoT devices using P2P SSH is more important than ever. With the growing number of smart devices, ensuring secure communication has become a top priority for users and businesses alike. This article will guide you through the process of setting up a secure P2P SSH connection for your remote IoT devices, with a focus on free tools and solutions available for Mac users.
As the Internet of Things (IoT) continues to expand, the need for secure communication between devices has never been more critical. Whether you're managing home automation systems or deploying industrial IoT solutions, establishing a secure connection is essential to protect sensitive data and maintain system integrity.
In this comprehensive guide, we will explore how to securely connect remote IoT devices using P2P SSH, provide step-by-step instructions, and recommend free tools that are compatible with Mac operating systems. By the end of this article, you'll have the knowledge and tools needed to safeguard your IoT ecosystem.
Read also:Controversial Topic The Truth Behind Buscar Kid And His Mom Cctv Video Leak
Table of Contents
- Overview of Secure IoT Connections
- Understanding SSH and Its Role in IoT Security
- What is P2P SSH and Why Use It?
- Compatibility with Mac Systems
- Free Tools for Secure IoT Connections
- Step-by-Step Setup Guide
- Enhancing Security Tips
- Common Issues and Troubleshooting
- Industry Statistics and Trends
- Conclusion and Call to Action
Overview of Secure IoT Connections
Connecting IoT devices securely is crucial to prevent unauthorized access and potential data breaches. IoT devices are often deployed in remote locations, making secure remote access a necessity. In this section, we will discuss the importance of secure connections and the challenges associated with IoT security.
Challenges in IoT Security
Securing IoT devices presents unique challenges, including:
- Limited processing power and memory on devices
- Vulnerabilities in communication protocols
- Difficulties in managing and updating firmware
Understanding SSH and Its Role in IoT Security
SSH (Secure Shell) is a cryptographic network protocol used to securely operate network services over an unsecured network. It plays a vital role in securing IoT devices by providing encrypted communication channels. This section will delve into the fundamentals of SSH and how it applies to IoT security.
How SSH Works
SSH establishes a secure connection by encrypting data between two devices. Key components of SSH include:
- Public-key cryptography for authentication
- Data encryption to protect transmitted information
- Integrity checks to ensure data has not been tampered with
What is P2P SSH and Why Use It?
P2P (Peer-to-Peer) SSH allows direct communication between devices without the need for a central server. This approach enhances security by reducing potential points of failure and minimizing exposure to external threats. In this section, we will explore the benefits of using P2P SSH for IoT devices.
Advantages of P2P SSH
Using P2P SSH for IoT devices offers several advantages:
Read also:Mastering Remoteiot Vpc Ssh A Comprehensive Guide To Raspberry Pi And Windows 10 Integration
- Reduced latency in communication
- Improved security through direct connections
- Lower infrastructure costs
Compatibility with Mac Systems
Mac users can leverage built-in tools and third-party applications to establish secure P2P SSH connections for IoT devices. This section will highlight the compatibility of various tools with macOS and provide recommendations for optimal performance.
Mac-Specific Tools
Some popular tools for Mac users include:
- Terminal: A built-in application for SSH connections
- PuTTY: A versatile SSH client compatible with Mac
- Tunnelblick: An open-source application for creating secure tunnels
Free Tools for Secure IoT Connections
There are several free tools available for Mac users to securely connect IoT devices via P2P SSH. This section will introduce you to some of the best options and explain their features.
Recommended Tools
Consider the following tools for your secure IoT connections:
- OpenSSH: A widely-used open-source SSH client
- Bitvise SSH Client: A feature-rich SSH client with a free version
- WinSCP: A free SFTP and SCP client that supports SSH
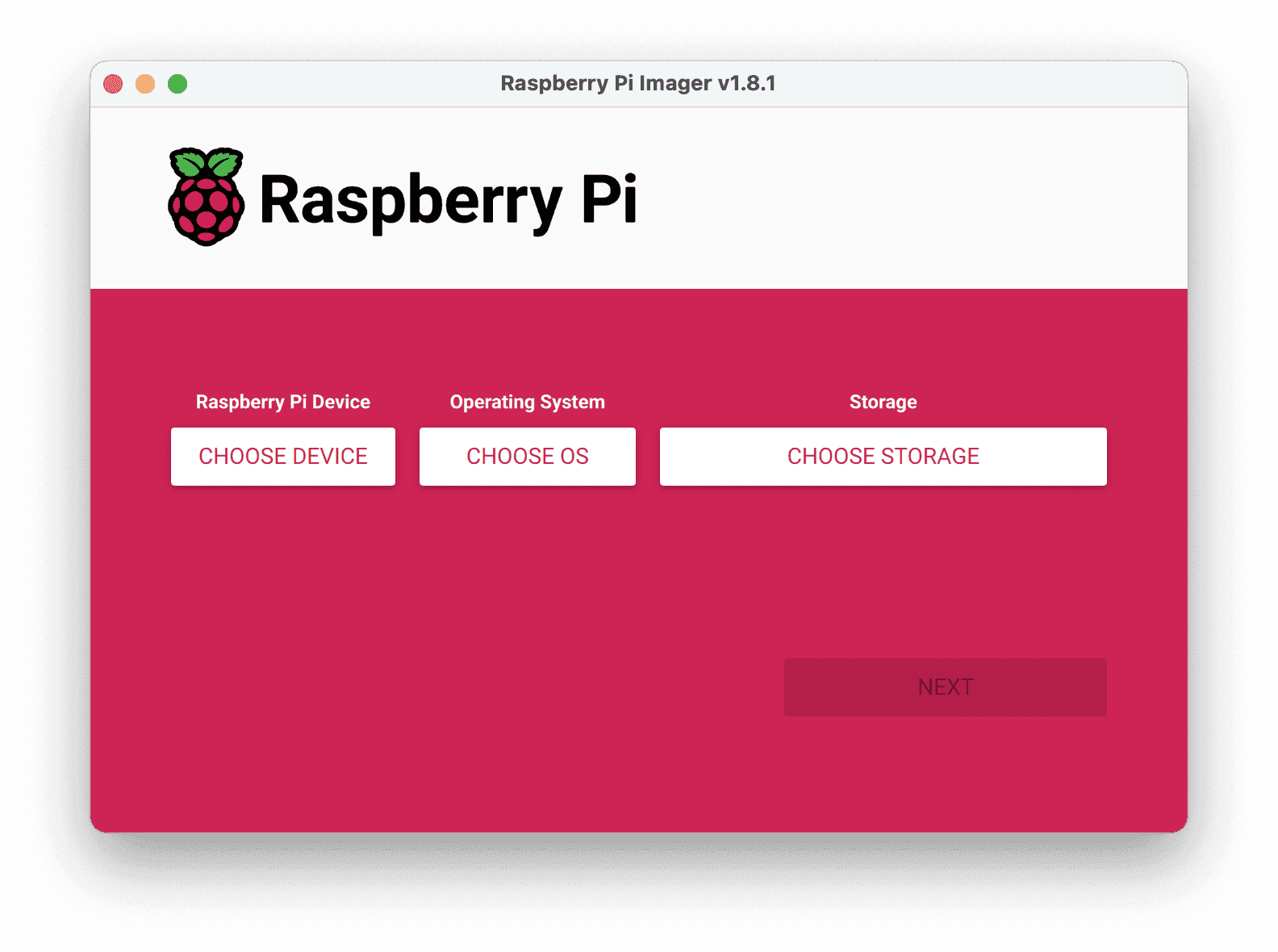
Step-by-Step Setup Guide
This section provides a detailed guide on setting up a secure P2P SSH connection for your IoT devices on a Mac. Follow these steps to ensure a secure and reliable connection.
Step 1: Install Required Software
Begin by installing the necessary software on your Mac. Most Mac systems come with OpenSSH pre-installed, but you may need to install additional tools depending on your requirements.
Step 2: Configure SSH Keys
Generate SSH keys to authenticate your devices. This ensures that only authorized devices can establish a connection.
Step 3: Establish the Connection
Use the appropriate commands in Terminal or your chosen SSH client to establish the connection between your IoT devices.
Enhancing Security Tips
While setting up a secure connection is essential, there are additional steps you can take to enhance the security of your IoT ecosystem. This section will provide practical tips to further protect your devices.
Best Practices for IoT Security
Implement the following best practices:
- Regularly update firmware and software
- Use strong, unique passwords for all devices
- Monitor network activity for suspicious behavior
Common Issues and Troubleshooting
Even with proper setup, issues may arise when establishing secure connections. This section will address common problems and provide solutions to help you troubleshoot effectively.
Troubleshooting Tips
If you encounter issues, consider the following:
- Check network settings and firewall rules
- Verify SSH key configurations
- Consult documentation for your chosen tools
Industry Statistics and Trends
The IoT market is growing rapidly, with projections indicating billions of connected devices by the end of the decade. Understanding industry trends and statistics can help you make informed decisions about securing your IoT ecosystem. This section will present relevant data and insights.
Key Statistics
According to recent reports:
- The global IoT market is expected to reach $1.5 trillion by 2030
- Cybersecurity spending on IoT is projected to increase significantly
- Over 75% of organizations have experienced an IoT-related security incident
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using P2P SSH is essential for protecting sensitive data and maintaining system integrity. By following the guidelines and recommendations outlined in this article, you can establish a secure connection for your IoT devices on a Mac system.
We encourage you to take action by implementing the steps discussed and exploring the recommended tools. Share your experience with us in the comments section below and consider exploring other articles on our site for more valuable insights.
Remember, securing your IoT ecosystem is not a one-time task but an ongoing process. Stay informed, stay vigilant, and keep your devices protected.