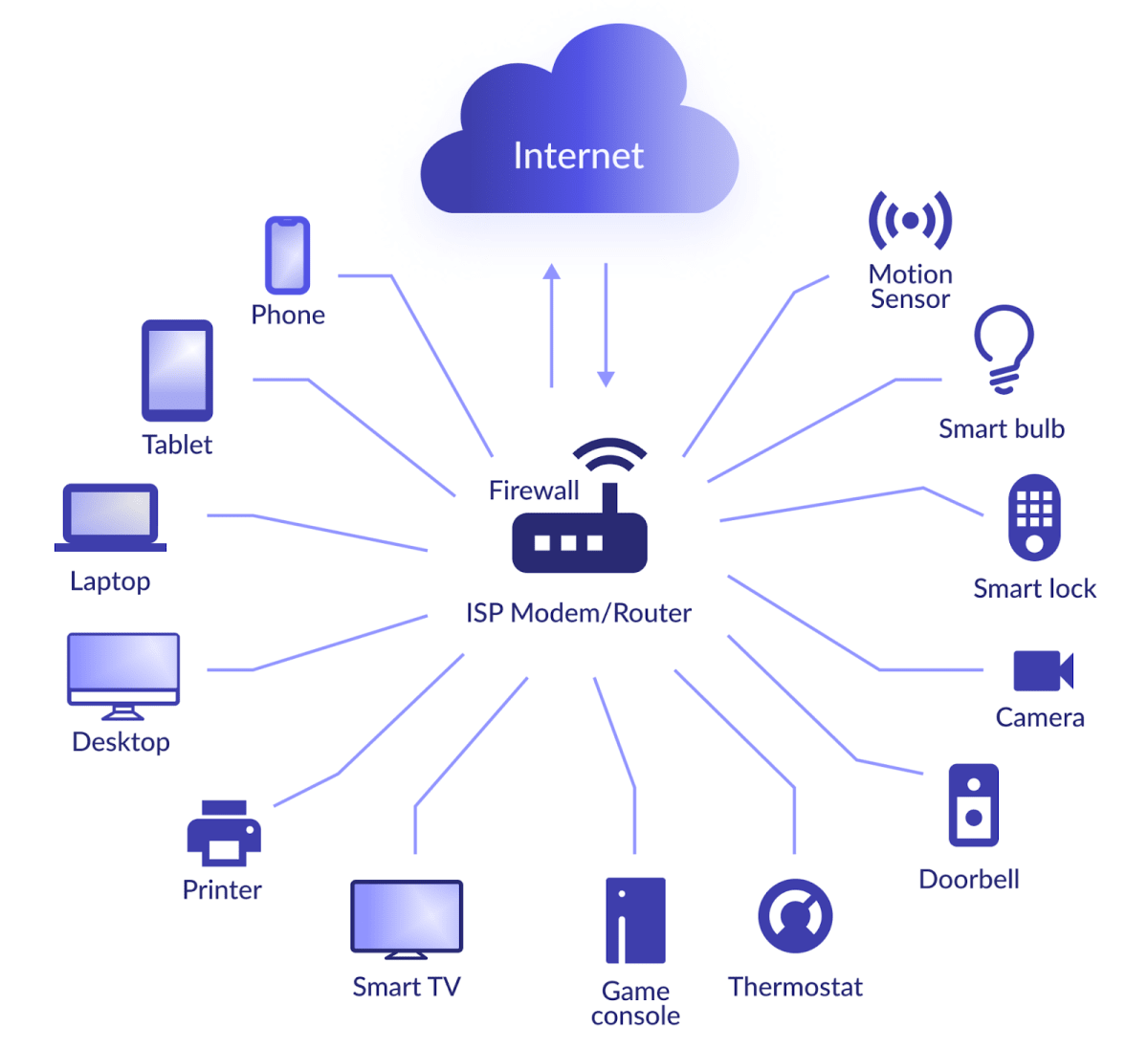
As the Internet of Things (IoT) continues to revolutionize the way we live and work, remote access IoT firewall example has become a critical component in ensuring the security of connected devices. With the growing number of smart devices, securing your network from potential cyber threats is no longer optional but essential. This guide will explore the concept of remote access IoT firewalls, their importance, and provide practical examples to help you safeguard your IoT ecosystem.
With billions of IoT devices now connected to the internet, the potential attack surface for cybercriminals has expanded exponentially. In this article, we will delve into the importance of remote access IoT firewalls, how they work, and provide real-world examples to ensure your network remains secure. Whether you're a business owner or an individual user, understanding the role of firewalls in IoT security is crucial.
This article aims to provide a comprehensive overview of remote access IoT firewalls and how they can be implemented effectively. By the end of this guide, you will have a better understanding of the best practices and strategies to protect your IoT infrastructure from unauthorized access and potential breaches.
Read also:5movierulz 2025 The Ultimate Guide To Downloading Kannada Movies
What is Remote Access IoT Firewall?
A remote access IoT firewall refers to a security mechanism designed to protect IoT devices and networks from unauthorized access and cyber threats when accessed remotely. Unlike traditional firewalls, which primarily focus on securing local networks, remote access IoT firewalls are specifically tailored to address the unique challenges posed by IoT ecosystems. These firewalls monitor and filter incoming and outgoing traffic, ensuring only legitimate connections are allowed while blocking malicious attempts.
Key Features of Remote Access IoT Firewalls
- Advanced traffic filtering capabilities to distinguish between legitimate and malicious connections.
- Real-time threat detection and response to minimize the risk of data breaches.
- Customizable rules and policies to cater to specific network requirements.
- Integration with other security solutions for a comprehensive defense strategy.
Why is Remote Access IoT Firewall Important?
In today's interconnected world, securing IoT devices is paramount. Remote access IoT firewalls play a crucial role in protecting sensitive data and ensuring the integrity of your network. Without proper security measures, IoT devices can become easy targets for cybercriminals, leading to potential data breaches, financial losses, and reputational damage.
Statistics on IoT Security Threats
According to a report by Gartner, the number of IoT devices is expected to surpass 25 billion by 2025. With this rapid growth, the number of security incidents targeting IoT devices has also increased significantly. In 2022 alone, there was a 30% rise in IoT-related cyberattacks compared to the previous year. These statistics highlight the urgent need for robust security solutions like remote access IoT firewalls.
How Does Remote Access IoT Firewall Work?
Remote access IoT firewalls function by analyzing and filtering network traffic based on predefined rules and policies. They monitor all incoming and outgoing data packets, ensuring only authorized connections are allowed. Additionally, these firewalls can be configured to detect and respond to suspicious activities in real-time, providing an additional layer of protection for your IoT ecosystem.
Steps Involved in Remote Access IoT Firewall Operation
- Packet inspection: Examining each data packet to determine its origin and destination.
- Rule evaluation: Applying predefined rules to decide whether to allow or block the connection.
- Threat detection: Identifying potential threats and taking appropriate action to mitigate them.
- Logging and reporting: Maintaining a record of all network activities for future analysis and auditing.
Examples of Remote Access IoT Firewalls
Several remote access IoT firewall solutions are available in the market, each with its own set of features and capabilities. Below are some examples of popular remote access IoT firewalls:
1. pfSense
pfSense is an open-source firewall and router software that supports remote access for IoT devices. It offers advanced features such as stateful packet inspection, intrusion prevention, and virtual private networking (VPN) capabilities. pfSense is highly customizable and can be tailored to meet the specific needs of your IoT network.
Read also:Lauren Graham Kids A Comprehensive Look Into The Lives Of Lauren Grahams Children
2. SonicWall
SonicWall provides a range of firewall solutions designed specifically for IoT environments. Their remote access firewalls offer features such as deep packet inspection, application control, and multi-factor authentication. SonicWall's firewalls are known for their ease of use and robust security features.
3. Fortinet FortiGate
Fortinet's FortiGate series of firewalls offers comprehensive protection for IoT networks. These firewalls support remote access and include features such as threat intelligence, sandboxing, and web filtering. FortiGate firewalls are widely used by enterprises due to their scalability and performance.
Implementing Remote Access IoT Firewalls
Implementing a remote access IoT firewall involves several steps, including assessing your network requirements, selecting the appropriate solution, and configuring the firewall settings. Below is a step-by-step guide to help you implement a remote access IoT firewall effectively:
Step 1: Assess Your Network Requirements
Before selecting a firewall solution, it's essential to evaluate your network's specific needs. Consider factors such as the number of IoT devices, the type of data being transmitted, and the level of security required.
Step 2: Choose the Right Firewall Solution
Based on your assessment, select a remote access IoT firewall that aligns with your network requirements. Ensure the chosen solution offers the necessary features and capabilities to protect your IoT ecosystem.
Step 3: Configure Firewall Settings
Once the firewall is installed, configure its settings to optimize performance and security. This includes setting up access rules, enabling threat detection features, and configuring logging and reporting options.
Best Practices for Securing IoT Networks
In addition to implementing a remote access IoT firewall, there are several best practices you can follow to enhance the security of your IoT network:
1. Regularly Update Firmware
Ensure all IoT devices and firewalls are running the latest firmware versions to protect against known vulnerabilities.
2. Use Strong Authentication Mechanisms
Implement multi-factor authentication (MFA) to add an extra layer of security when accessing IoT devices remotely.
3. Segment Your Network
Divide your network into separate segments to isolate IoT devices from critical systems, reducing the risk of unauthorized access.
Challenges in IoT Security
While remote access IoT firewalls provide an effective solution for securing IoT networks, there are several challenges that need to be addressed:
1. Device Diversity
IoT devices come in various shapes and sizes, each with its own set of security requirements. Ensuring consistent security across all devices can be challenging.
2. Limited Resources
Many IoT devices have limited processing power and memory, making it difficult to implement complex security solutions.
3. Rapid Evolution
The IoT landscape is constantly evolving, with new devices and technologies emerging regularly. Keeping up with the latest security trends and threats can be a daunting task.
Future of Remote Access IoT Firewalls
As IoT continues to grow, the role of remote access IoT firewalls will become increasingly important. Advancements in artificial intelligence (AI) and machine learning (ML) are expected to enhance the capabilities of these firewalls, enabling them to detect and respond to threats more effectively. Additionally, the development of new protocols and standards will further improve the security of IoT networks.
Conclusion
Remote access IoT firewalls are essential for securing your IoT ecosystem and protecting it from potential cyber threats. By understanding how these firewalls work and implementing best practices, you can significantly reduce the risk of unauthorized access and data breaches. We encourage you to explore the examples and solutions discussed in this article and take the necessary steps to safeguard your IoT network.
Feel free to leave a comment below if you have any questions or would like to share your experiences with remote access IoT firewalls. Don't forget to share this article with others who may benefit from the information provided. For more insights on IoT security, explore our other articles on the topic.
Table of Contents
- What is Remote Access IoT Firewall?
- Why is Remote Access IoT Firewall Important?
- How Does Remote Access IoT Firewall Work?
- Examples of Remote Access IoT Firewalls
- Implementing Remote Access IoT Firewalls
- Best Practices for Securing IoT Networks
- Challenges in IoT Security
- Future of Remote Access IoT Firewalls
- Conclusion