As the world becomes increasingly interconnected, securely connecting remote IoT devices through P2P SSH on Android has become a critical skill for tech-savvy users. Whether you're managing smart home devices, industrial sensors, or personal gadgets, ensuring secure communication is paramount. This comprehensive guide will walk you through everything you need to know about setting up, securing, and optimizing remote IoT connections on your Android device.
In today's digital age, the Internet of Things (IoT) has revolutionized the way we interact with technology. From smart thermostats to autonomous vehicles, IoT devices are transforming industries and enhancing our daily lives. However, with this convenience comes the responsibility of maintaining robust security measures to protect sensitive data and prevent unauthorized access.
This article is designed to provide you with actionable insights, practical tips, and expert advice to help you securely connect remote IoT devices using P2P SSH on Android. Whether you're a beginner or an experienced user, this guide will equip you with the knowledge and tools you need to safeguard your IoT ecosystem.
Read also:Movierulz 2023 Telugu Your Ultimate Guide To Telugu Movies
Table of Contents
- Introduction to Secure IoT Connections
- Understanding SSH and Its Role in IoT Security
- What Is P2P SSH and How Does It Work?
- Connecting Remote IoT Devices Securely
- Setting Up P2P SSH on Android
- Security Tips for Remote IoT Connections
- Recommended Tools and Apps for Android
- Troubleshooting Common Issues
- Future Trends in IoT Security
- Conclusion and Call to Action
Introduction to Secure IoT Connections
The proliferation of IoT devices has created new opportunities for innovation and convenience. However, it has also introduced unique security challenges. Securely connecting remote IoT devices is essential to protect sensitive data and maintain system integrity. In this section, we'll explore the basics of IoT security and why it matters.
Why Security Matters in IoT
IoT devices often handle critical data, from personal health information to industrial control systems. A single breach can have far-reaching consequences, compromising privacy, safety, and even financial stability. By implementing robust security measures, such as P2P SSH, you can significantly reduce the risk of unauthorized access and data breaches.
Understanding SSH and Its Role in IoT Security
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It plays a vital role in IoT security by encrypting data transmissions and authenticating devices. Understanding how SSH works is the first step toward securing your IoT ecosystem.
Key Features of SSH
- Encryption: Protects data in transit from being intercepted or tampered with.
- Authentication: Ensures that only authorized devices can access the network.
- Integrity: Verifies that data has not been altered during transmission.
What Is P2P SSH and How Does It Work?
P2P SSH, or Peer-to-Peer Secure Shell, enables direct and secure communication between IoT devices without relying on a central server. This decentralized approach offers several advantages, including improved security, reduced latency, and enhanced scalability. Let's delve into how P2P SSH works and its benefits for IoT applications.
Advantages of P2P SSH
- Enhanced Security: By eliminating the need for a central server, P2P SSH reduces the risk of single-point failures and attacks.
- Improved Performance: Direct device-to-device communication minimizes latency and bandwidth usage.
- Cost-Effective: P2P SSH eliminates the need for costly infrastructure investments.
Connecting Remote IoT Devices Securely
Connecting remote IoT devices securely is a multi-step process that involves configuring SSH settings, establishing secure connections, and implementing best practices for data protection. In this section, we'll walk you through the steps to ensure your IoT devices are protected.
Steps to Securely Connect Remote IoT Devices
- Install an SSH client on your Android device.
- Generate and configure SSH keys for authentication.
- Set up port forwarding to allow remote access.
- Test the connection to ensure secure communication.
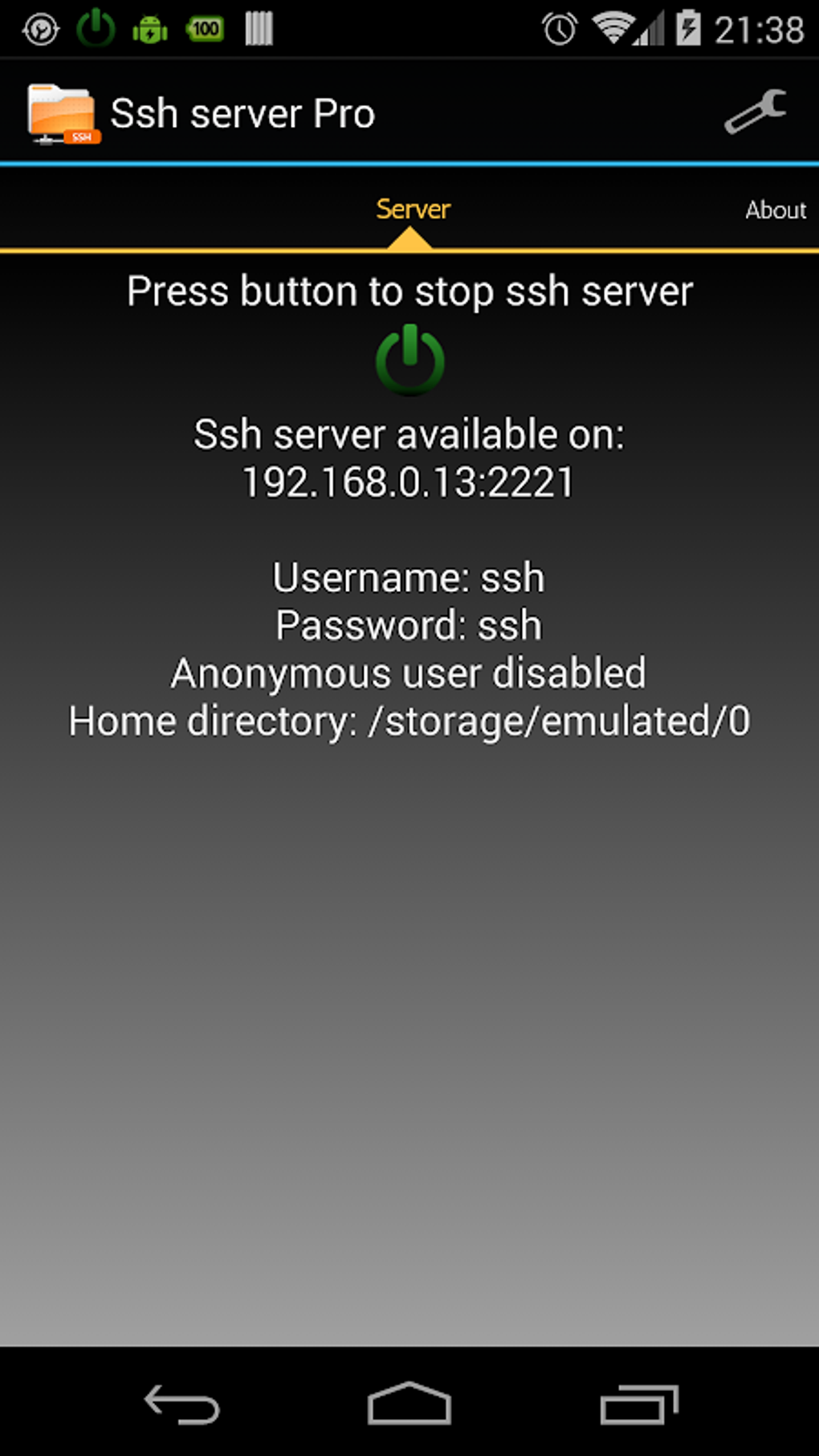
Setting Up P2P SSH on Android
Setting up P2P SSH on Android requires the right tools and configuration. With the increasing popularity of mobile devices in IoT management, having a secure and reliable setup is crucial. Follow these steps to get started:
Read also:Hdhub4u In Bollywood Your Ultimate Guide To Movie Downloads And Entertainment
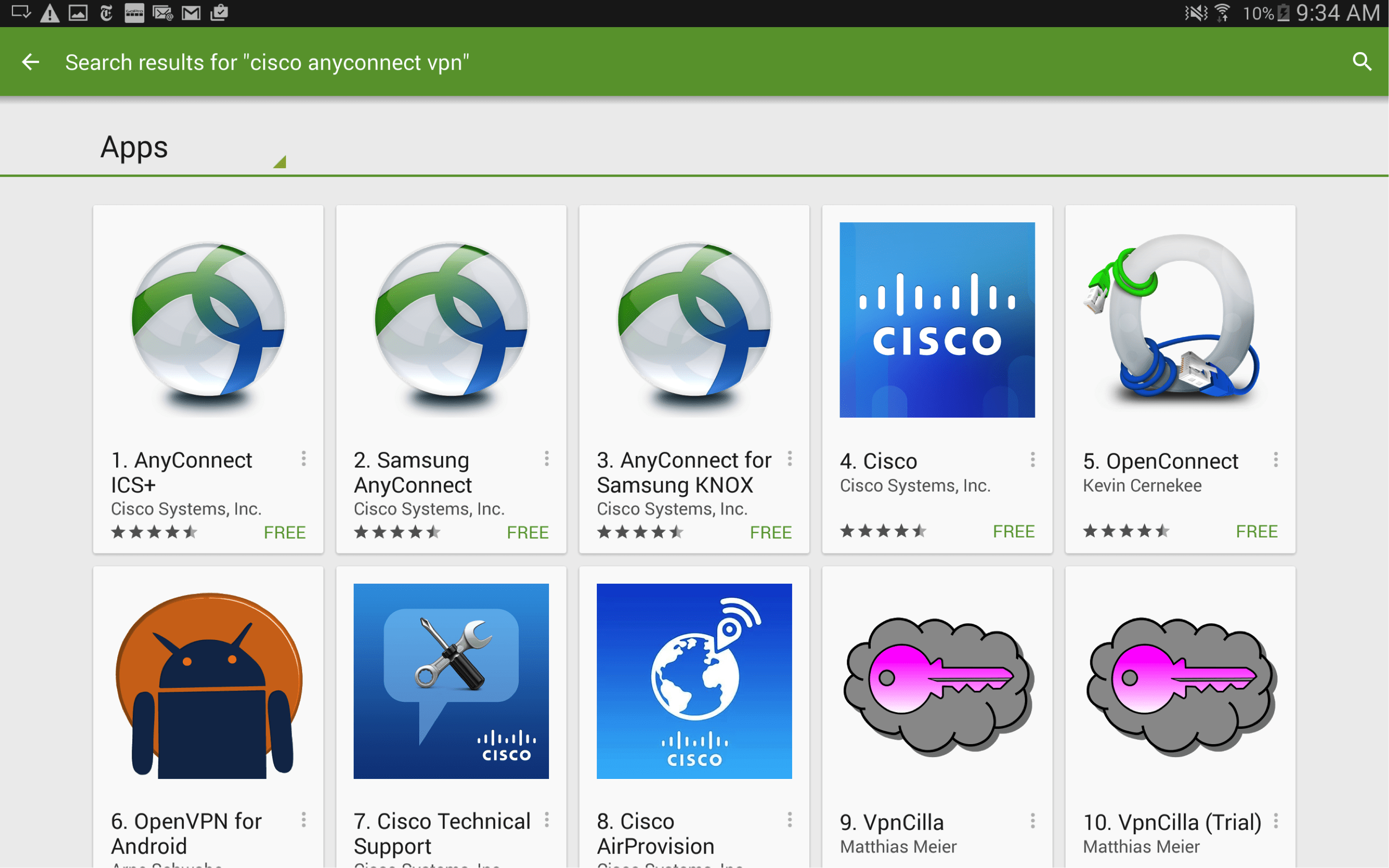
Recommended Android SSH Clients
- Termux: A powerful terminal emulator and Linux environment app.
- ConnectBot: A free and open-source SSH client for Android.
- SSH Client by Ice Cold Apps: A user-friendly SSH client with advanced features.
Security Tips for Remote IoT Connections
To ensure the highest level of security for your remote IoT connections, follow these best practices:
Best Practices for IoT Security
- Use strong, unique passwords for all devices and accounts.
- Enable two-factor authentication whenever possible.
- Regularly update firmware and software to patch vulnerabilities.
- Monitor network activity for suspicious behavior.
Recommended Tools and Apps for Android
Several tools and apps can help streamline the process of setting up and managing P2P SSH connections on Android. Here are some of the most popular options:
Top Tools for IoT Security
- Wireshark: A network protocol analyzer for troubleshooting and monitoring.
- OpenSSH: A widely-used SSH implementation for secure communication.
- SSHFS: A file system client that allows you to mount remote file systems over SSH.
Troubleshooting Common Issues
Even with the best preparations, issues can arise when setting up P2P SSH connections. Here are some common problems and their solutions:
Common Issues and Solutions
- Connection Refused: Ensure that the SSH server is running and that port forwarding is correctly configured.
- Authentication Failed: Double-check your SSH keys and passwords for accuracy.
- Slow Performance: Optimize your network settings and reduce bandwidth usage.
Future Trends in IoT Security
As IoT technology continues to evolve, so do the methods for securing these devices. Emerging trends such as blockchain, quantum cryptography, and AI-driven security solutions are poised to revolutionize the field. Stay informed about these developments to ensure your IoT ecosystem remains secure in the years to come.
Emerging Technologies in IoT Security
- Blockchain: Provides decentralized and tamper-proof data storage solutions.
- Quantum Cryptography: Offers unparalleled security through quantum mechanics principles.
- AI and Machine Learning: Enables predictive analytics and real-time threat detection.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices through P2P SSH on Android is a crucial skill for anyone managing an IoT ecosystem. By following the steps outlined in this guide and implementing best practices for security, you can protect your devices and data from potential threats.
We invite you to share your thoughts and experiences in the comments section below. Have you encountered any challenges while setting up P2P SSH on Android? What tools and strategies have worked best for you? Don't forget to explore our other articles for more insights into IoT security and technology trends.
For further reading and research, consider consulting the following sources:
- SSH.com - The Secure Shell Protocol
- IoT World Today - Latest IoT News and Trends
- NIST Cybersecurity Framework