As the Internet of Things (IoT) continues to grow exponentially, managing secure connections for IoT devices behind firewalls has become a critical challenge for businesses and developers alike. RemoteIoT behind firewall examples provide valuable insights into how organizations can establish secure, reliable, and efficient communication between devices while maintaining robust network security. In this article, we will explore the concept of RemoteIoT behind firewalls, its applications, and practical examples to help you implement secure IoT solutions in your network.
The integration of IoT devices into enterprise networks often raises concerns about security, privacy, and data integrity. Firewalls play a crucial role in protecting internal networks from external threats, but they can also act as barriers for IoT devices attempting to communicate with external servers or cloud platforms. Understanding RemoteIoT behind firewall examples can help you overcome these challenges and ensure seamless connectivity without compromising security.
This comprehensive guide will provide you with a detailed understanding of RemoteIoT behind firewall scenarios, including technical approaches, best practices, and real-world applications. Whether you're a developer, IT professional, or decision-maker, this article will equip you with the knowledge and tools needed to implement secure IoT solutions in your organization.
Read also:Lauren Graham Kids A Comprehensive Look Into The Lives Of Lauren Grahams Children
Table of Contents
- Introduction to RemoteIoT Behind Firewalls
- Understanding Firewalls and Their Role in IoT Networks
- What is RemoteIoT and Why is it Important?
- RemoteIoT Behind Firewall Examples
- Security Considerations for RemoteIoT Behind Firewalls
- Best Practices for Implementing RemoteIoT Solutions
- Tools and Technologies for RemoteIoT Deployment
- Common Challenges and Solutions
- Future Trends in RemoteIoT Behind Firewalls
- Conclusion and Next Steps
Introduction to RemoteIoT Behind Firewalls
The concept of RemoteIoT behind firewalls refers to the ability of IoT devices to communicate securely with external servers, cloud platforms, or other devices while residing within a protected internal network. Firewalls are essential for safeguarding enterprise networks from unauthorized access, but they can also create obstacles for IoT devices attempting to establish outbound connections.
Organizations must balance the need for security with the demand for seamless connectivity. By leveraging RemoteIoT behind firewall examples, businesses can design architectures that enable secure communication without exposing their networks to potential threats. This section will introduce the key concepts and challenges associated with RemoteIoT behind firewalls.
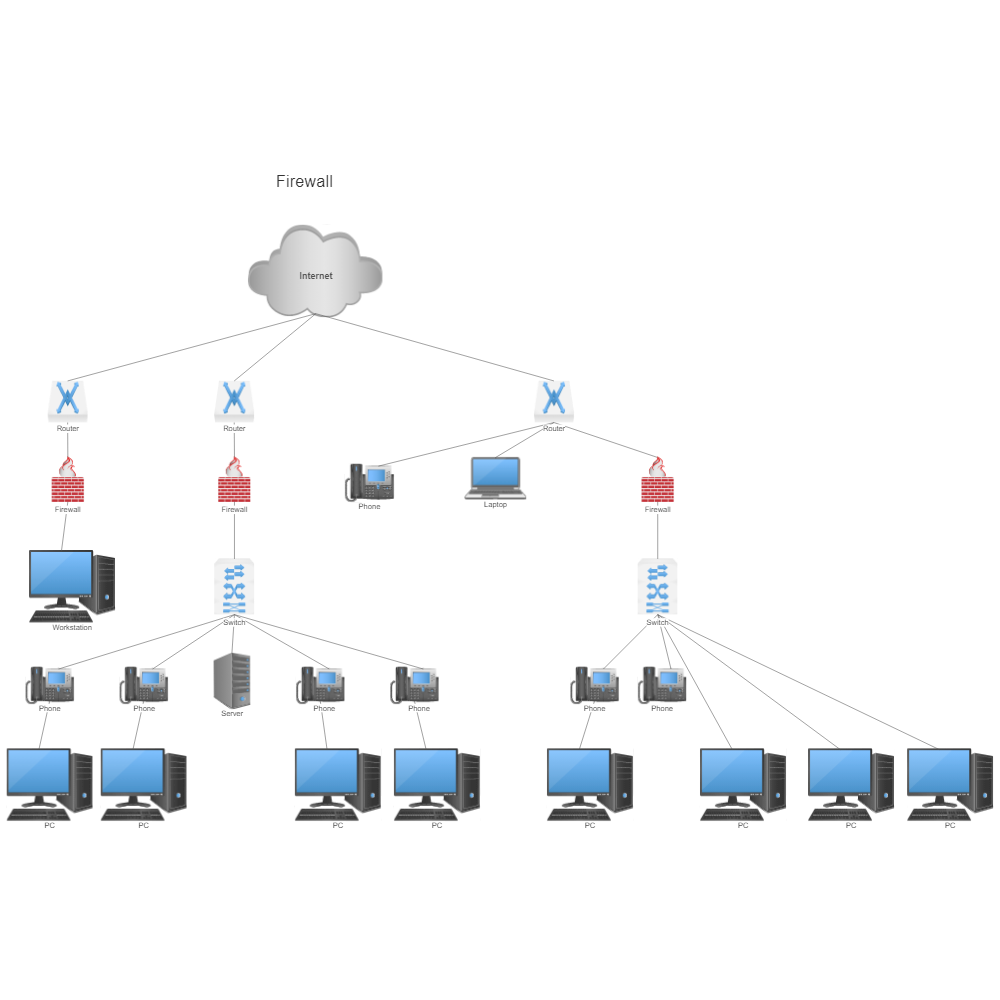
Understanding Firewalls and Their Role in IoT Networks
Firewalls are network security systems that monitor and control incoming and outgoing network traffic based on predetermined security rules. They act as a barrier between internal networks and external environments, ensuring that only authorized traffic is allowed to pass through.
In the context of IoT, firewalls play a critical role in protecting sensitive devices and data from cyberattacks. However, they can also block legitimate IoT traffic if not configured properly. Understanding how firewalls work and their impact on IoT networks is essential for designing effective RemoteIoT solutions.
What is RemoteIoT and Why is it Important?
RemoteIoT refers to the ability of IoT devices to communicate with external systems or platforms while being physically located in remote or isolated environments. This capability is crucial for enabling real-time monitoring, data collection, and remote control of devices in various industries, including manufacturing, healthcare, and smart cities.
By implementing RemoteIoT solutions behind firewalls, organizations can ensure that their IoT devices remain secure while maintaining connectivity with external systems. This section will explore the importance of RemoteIoT and its applications in modern business environments.
Read also:Kaitlan Collins Husband A Comprehensive Guide To Her Personal Life
RemoteIoT Behind Firewall Examples
Example 1: Port Forwarding
Port forwarding is a common technique used to allow external access to devices located behind firewalls. By configuring the firewall to forward specific ports to internal devices, organizations can enable secure communication without exposing the entire network. However, this approach requires careful planning and implementation to avoid security risks.
Example 2: Reverse Proxy
A reverse proxy acts as an intermediary between internal devices and external clients, allowing secure communication without exposing the internal network. This method is particularly useful for IoT devices that need to communicate with multiple external systems simultaneously. By using a reverse proxy, organizations can enhance security and improve performance.
Example 3: Virtual Private Network (VPN)
VPNs provide a secure tunnel for communication between IoT devices and external systems, ensuring that all data transmissions are encrypted and protected from unauthorized access. Implementing a VPN for RemoteIoT behind firewalls is an effective way to maintain security while enabling seamless connectivity.
Example 4: MQTT Over WebSockets
MQTT (Message Queuing Telemetry Transport) is a lightweight messaging protocol commonly used in IoT applications. By combining MQTT with WebSockets, organizations can establish secure, real-time communication between devices behind firewalls and external systems. This approach is particularly useful for applications requiring low-latency data transmission.
Example 5: Cloud-Based IoT Platforms
Cloud-based IoT platforms offer a scalable and secure solution for managing IoT devices behind firewalls. These platforms provide built-in support for secure communication protocols, data encryption, and device authentication, making it easier for organizations to implement RemoteIoT solutions without compromising security.
Security Considerations for RemoteIoT Behind Firewalls
When implementing RemoteIoT solutions behind firewalls, security should always be a top priority. Organizations must address potential vulnerabilities and implement robust security measures to protect their networks and devices. This section will discuss key security considerations, including encryption, authentication, and access control.
Best Practices for Implementing RemoteIoT Solutions
To ensure successful deployment of RemoteIoT solutions behind firewalls, organizations should follow best practices that emphasize security, scalability, and efficiency. Some of these practices include:
- Using strong encryption protocols for data transmission
- Implementing multi-factor authentication for device access
- Regularly updating firmware and software to address security vulnerabilities
- Monitoring network activity for signs of unauthorized access
- Documenting and testing all configurations before deployment
Tools and Technologies for RemoteIoT Deployment
Several tools and technologies are available to facilitate the deployment of RemoteIoT solutions behind firewalls. These include:
- Firewall management software
- IoT device management platforms
- Cloud-based IoT services
- Encryption libraries and frameworks
- Network monitoring and analytics tools
By leveraging these tools, organizations can streamline the implementation process and ensure optimal performance of their RemoteIoT solutions.
Common Challenges and Solutions
Implementing RemoteIoT solutions behind firewalls can present several challenges, including:
- Configuring firewalls to allow IoT traffic without compromising security
- Ensuring consistent connectivity in dynamic network environments
- Managing large numbers of devices and data streams
- Addressing latency and bandwidth limitations
This section will provide practical solutions to these challenges, helping organizations overcome common obstacles in their RemoteIoT deployments.
Future Trends in RemoteIoT Behind Firewalls
As IoT technology continues to evolve, new trends and innovations are emerging in the field of RemoteIoT behind firewalls. These include advancements in edge computing, AI-driven security, and 5G connectivity. By staying informed about these trends, organizations can position themselves for success in the rapidly changing IoT landscape.
Conclusion and Next Steps
In conclusion, RemoteIoT behind firewall examples offer valuable insights into how organizations can implement secure and efficient IoT solutions in their networks. By understanding the key concepts, challenges, and best practices associated with RemoteIoT, businesses can design architectures that meet their unique needs and objectives.
We encourage you to explore the examples and resources provided in this article and consider how they can be applied to your own projects. Feel free to leave a comment or share this article with others who may find it useful. For more information on IoT and network security, be sure to check out our other articles and resources.