In today's interconnected world, managing IoT devices remotely is crucial for both personal and business purposes. If you're looking to control your IoT devices behind a router using MAC addresses without relying on Windows, you're in the right place. This article will walk you through the process step-by-step, ensuring a seamless experience.
As the Internet of Things (IoT) continues to expand, remote access to these devices becomes increasingly important. Whether it’s for home automation, smart security systems, or industrial applications, having the ability to manage IoT devices from anywhere is a game-changer. However, doing so securely and efficiently can be challenging, especially when you're not using a Windows-based system.
This guide aims to demystify the process of remotely accessing IoT devices behind a router using MAC addresses. By the end of this article, you'll have the knowledge and tools necessary to implement this setup effectively. Let’s dive in!
Read also:Hdhub4u In Movie Hindi Your Ultimate Guide To Streaming Bollywood Movies
Table of Contents
- Introduction to Remote IoT Access
- Why Use MAC Address for IoT Devices
- Router Configuration for Remote IoT
- Non-Windows Options for Remote Access
- Tools and Software You'll Need
- Step-by-Step Guide to Remote IoT Access
- Security Best Practices for Remote IoT
- Common Issues and Troubleshooting
- Future Trends in IoT Remote Access
- Conclusion and Next Steps
Introduction to Remote IoT Access
What is IoT Remote Access?
Remote IoT access refers to the ability to control and monitor Internet of Things devices from a distance, regardless of location. This is achieved through various technologies and protocols that allow secure communication between devices and users.
For those unfamiliar, IoT devices range from smart home appliances to industrial sensors. Remote access ensures that these devices remain functional and secure, even when physical access is not possible.
Using a router's MAC address filtering is one method to enhance security while managing these devices. This approach minimizes unauthorized access and ensures only trusted devices connect to your network.
Why Use MAC Address for IoT Devices
Understanding MAC Addresses
A MAC (Media Access Control) address is a unique identifier assigned to network interfaces for communications at the data link layer of a network segment. By utilizing MAC addresses, you can:
- Identify specific devices on your network
- Restrict access to only authorized devices
- Monitor device activity more effectively
Using MAC addresses is particularly beneficial for IoT devices because it provides an additional layer of security, ensuring only trusted devices can connect to your network.
Router Configuration for Remote IoT
Setting Up Your Router for IoT Devices
Configuring your router is the first step in enabling remote access to IoT devices. Here's how you can do it:
Read also:Telugu Movierulz 2025 The Ultimate Guide To Telugu Movies And Beyond
1. Access your router's admin interface by typing its IP address into a web browser.
2. Log in using your credentials.
3. Navigate to the settings related to device management and MAC address filtering.
4. Add the MAC addresses of your IoT devices to the whitelist.
This setup ensures that only devices with approved MAC addresses can connect to your network, enhancing security and control.
Non-Windows Options for Remote Access
Alternatives to Windows for Remote IoT Access
While Windows is a popular choice for remote access software, there are several alternatives that work just as effectively:
- Linux: Offers robust command-line tools and a wide range of open-source software for remote access.
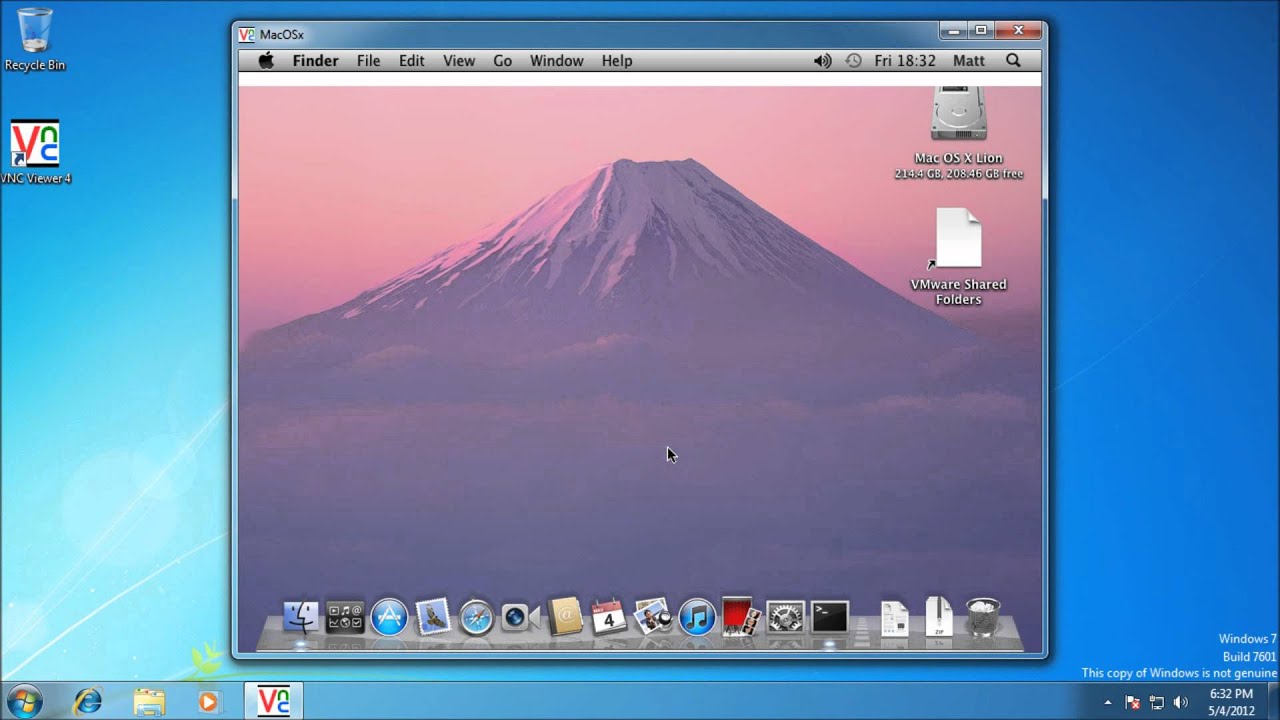
- macOS: Provides built-in tools like Screen Sharing and Terminal for managing remote devices.
- Android/iOS: Various apps are available for mobile remote access, making it convenient to manage IoT devices on the go.
These platforms provide flexibility and security, allowing you to manage IoT devices without the need for Windows.
Tools and Software You'll Need
Essential Tools for Remote IoT Access
To successfully manage IoT devices remotely, you'll need the following tools and software:
- SSH (Secure Shell): For secure command-line access to devices.
- Port Forwarding Tools: To enable communication between your local network and the internet.
- Network Monitoring Software: To keep track of device activity and ensure security.
These tools are essential for maintaining a secure and efficient remote IoT setup.
Step-by-Step Guide to Remote IoT Access
Implementing Remote Access
Follow these steps to set up remote access for your IoT devices:
1. Identify the MAC addresses of your IoT devices.
2. Configure your router to allow only these MAC addresses.
3. Set up port forwarding to enable external access.
4. Use SSH or a similar protocol to establish a secure connection.
5. Test the connection to ensure everything is working correctly.
By following these steps, you'll have a secure and functional remote IoT setup in no time.
Security Best Practices for Remote IoT
Ensuring Security in Remote IoT Access
Security is paramount when dealing with remote IoT access. Here are some best practices to follow:
- Use strong, unique passwords for all devices and accounts.
- Enable two-factor authentication wherever possible.
- Regularly update firmware and software to protect against vulnerabilities.
- Monitor network activity for any suspicious behavior.
Implementing these practices will help safeguard your IoT devices and network from potential threats.
Common Issues and Troubleshooting
Addressing Challenges in Remote IoT Access
Despite careful setup, issues can arise. Here are some common problems and their solutions:
- Connection Issues: Check router settings and ensure all ports are correctly forwarded.
- Security Alerts: Verify that all devices are authorized and update security protocols.
- Performance Problems: Optimize network settings and reduce unnecessary traffic.
By troubleshooting these issues effectively, you can maintain a stable and secure remote IoT environment.
Future Trends in IoT Remote Access
Innovations in Remote IoT Management
The future of IoT remote access looks promising, with advancements in technology driving innovation. Some trends to watch include:
- Enhanced security protocols to protect against evolving threats.
- Integration with AI and machine learning for smarter device management.
- Increased adoption of cloud-based solutions for easier scalability.
Staying informed about these trends will help you leverage the latest technologies for your remote IoT setup.
Conclusion and Next Steps
Summarizing the Key Points
In conclusion, managing IoT devices remotely using MAC addresses without Windows is both feasible and secure. By following the steps outlined in this guide, you can create a robust setup that meets your needs. Remember to prioritize security and stay updated with the latest trends in IoT technology.
We encourage you to take action by implementing the strategies discussed here. Don't hesitate to leave a comment or share this article with others who might find it useful. For further reading, explore our other articles on IoT and remote access solutions.
Thank you for reading, and happy IoT managing!