RemoteIoT platform SSH key has become an essential tool for professionals in the Internet of Things (IoT) industry. With the rise of remote management and secure data exchange, understanding and implementing SSH keys correctly is more important than ever. This article will guide you through everything you need to know about RemoteIoT platform SSH keys, from their basics to advanced implementation strategies.
In the era of interconnected devices, ensuring secure communication between systems is critical. RemoteIoT platform SSH key plays a pivotal role in securing these connections by providing cryptographic authentication. This technology not only protects sensitive data but also ensures the integrity of your IoT network, which is crucial for businesses and individuals alike.
Whether you're a seasoned IT professional or just starting to explore the world of IoT, this comprehensive guide will equip you with the knowledge and tools necessary to leverage RemoteIoT platform SSH key effectively. Let’s dive into the details and discover how you can enhance the security of your IoT infrastructure.
Read also:How Tall Is Dorit Kemsley Discover The Real Facts About This Reality Star
Table of Contents
- What is RemoteIoT Platform SSH Key?
- How RemoteIoT Platform SSH Key Works
- Importance of SSH Key in IoT Security
- Generating SSH Keys for RemoteIoT Platform
- Configuring SSH Keys on RemoteIoT Platform
- Best Practices for Using SSH Keys
- Common Issues and Troubleshooting
- Security Considerations for RemoteIoT Platform SSH Key
- Integration with Other Systems
- The Future of RemoteIoT Platform SSH Key
What is RemoteIoT Platform SSH Key?
The RemoteIoT platform SSH key refers to the cryptographic keys used to authenticate devices and users within the RemoteIoT ecosystem. These keys are an integral part of the SSH (Secure Shell) protocol, which ensures secure communication between IoT devices and remote servers. By leveraging SSH keys, users can establish encrypted connections without relying on traditional password authentication.
SSH keys consist of two parts: a private key and a public key. The private key must be securely stored on the client device, while the public key is shared with the server. This key pair ensures that only authorized devices can access the network, enhancing overall security.
Why Use SSH Keys in IoT?
Using SSH keys in IoT offers several advantages:
- Eliminates the need for passwords, reducing the risk of brute-force attacks.
- Provides strong encryption for data transmitted between devices.
- Facilitates seamless and secure remote management of IoT devices.
How RemoteIoT Platform SSH Key Works
The operation of RemoteIoT platform SSH key revolves around the principles of public-key cryptography. When a client attempts to connect to a server, the server verifies the client's public key against its authorized keys list. If the key matches, the server grants access, establishing a secure session.
This process involves several steps:
- Key generation: Creating a private-public key pair.
- Key exchange: Sharing the public key with the server.
- Authentication: Verifying the client's identity using the private key.
- Session establishment: Initiating a secure communication channel.
Advantages of SSH Key Authentication
SSH key authentication offers several benefits over traditional password-based systems:
Read also:Does Vivid Seats Have Service Fees A Comprehensive Guide
- Enhanced security through cryptographic methods.
- Convenience of not requiring users to remember complex passwords.
- Scalability for managing multiple devices and users.
Importance of SSH Key in IoT Security
As IoT devices continue to proliferate, the importance of SSH keys in securing these networks cannot be overstated. With billions of connected devices, the potential for cyberattacks increases exponentially. SSH keys provide a robust defense mechanism against unauthorized access and data breaches.
According to a report by Gartner, the number of IoT devices is expected to reach 25 billion by 2030. This growth underscores the need for secure authentication methods like SSH keys. By implementing SSH keys, organizations can protect sensitive data and maintain the integrity of their IoT infrastructure.
Generating SSH Keys for RemoteIoT Platform
Generating SSH keys for the RemoteIoT platform is a straightforward process that involves a few simple steps:
Step-by-Step Guide
- Open your terminal or command prompt.
- Run the command:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com". - Follow the prompts to specify the file location and passphrase (optional).
- Once completed, your SSH key pair will be generated.
It’s important to store your private key securely and never share it with anyone. The public key can be shared with the RemoteIoT platform or any server you wish to connect to.
Configuring SSH Keys on RemoteIoT Platform
After generating your SSH keys, the next step is to configure them on the RemoteIoT platform. This involves uploading your public key to the platform and ensuring that it is recognized by the server.
Steps to Configure SSH Keys
- Log in to your RemoteIoT platform account.
- Navigate to the settings or security section.
- Locate the SSH key configuration option.
- Paste your public key into the designated field.
- Save the changes and test the connection.
By following these steps, you can ensure that your RemoteIoT platform is securely configured to use SSH keys for authentication.
Best Practices for Using SSH Keys
To maximize the security benefits of SSH keys, it’s important to adhere to best practices:
- Use strong, unique passphrases for your private keys.
- Regularly update and rotate your SSH keys.
- Limit access to your private keys and store them securely.
- Monitor and audit SSH key usage regularly.
Implementing these practices will help protect your RemoteIoT platform from potential security threats.
Common Issues and Troubleshooting
While SSH keys are a powerful tool, users may encounter issues during implementation. Some common problems include:
Key Not Recognized
If the server does not recognize your SSH key, ensure that:
- Your public key is correctly uploaded to the platform.
- The private key matches the public key.
- The file permissions for your private key are set correctly.
Connection Issues
If you experience connection issues, check the following:
- Verify the server’s SSH configuration settings.
- Ensure that firewalls or network settings are not blocking the connection.
- Test the connection using alternative methods to isolate the problem.
Security Considerations for RemoteIoT Platform SSH Key
When implementing SSH keys on the RemoteIoT platform, it’s crucial to consider various security aspects:
- Use the latest SSH protocol versions to benefit from enhanced security features.
- Enable two-factor authentication (2FA) for additional protection.
- Regularly update your SSH client and server software to patch vulnerabilities.
By addressing these security considerations, you can ensure that your RemoteIoT platform remains secure and resilient against attacks.
Integration with Other Systems
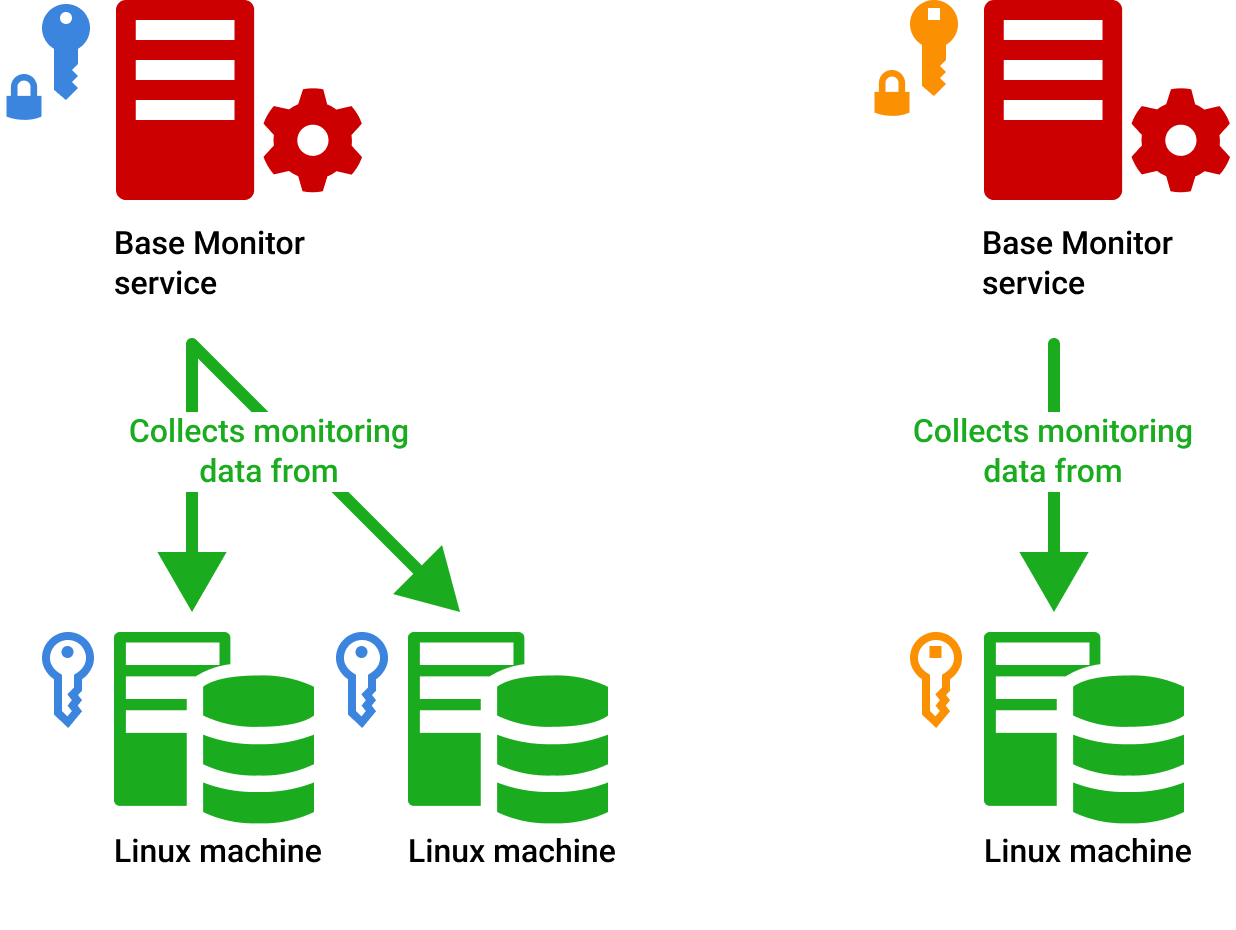
SSH keys can also be integrated with other systems and platforms to enhance their security. For example, you can use SSH keys to secure connections between:
- RemoteIoT platform and cloud services.
- IoT devices and backend servers.
- Development environments and deployment pipelines.
This integration ensures a consistent and secure authentication mechanism across your entire infrastructure.
The Future of RemoteIoT Platform SSH Key
As technology continues to evolve, the role of SSH keys in securing IoT platforms like RemoteIoT will only grow. Advancements in cryptography and quantum computing may introduce new challenges and opportunities for SSH key management.
Organizations must stay informed about these developments and adapt their security strategies accordingly. By embracing emerging technologies and best practices, you can ensure that your RemoteIoT platform remains secure and future-proof.
Emerging Trends
Some emerging trends in SSH key management include:
- Adoption of post-quantum cryptography for enhanced security.
- Increased use of automated key management systems.
- Integration with AI-driven security solutions for proactive threat detection.
Kesimpulan
In conclusion, mastering RemoteIoT platform SSH key is essential for anyone involved in IoT security. By understanding how SSH keys work, implementing them correctly, and following best practices, you can significantly enhance the security of your IoT infrastructure.
We encourage you to take action by generating and configuring your SSH keys today. Don’t forget to share this article with your network and explore other resources on our site to deepen your knowledge of IoT security.
Feel free to leave a comment or question below, and we’ll be happy to assist you further. Thank you for reading, and stay secure in the ever-evolving world of IoT!