Remote IoT technology has revolutionized the way we interact with devices from afar. Whether you're managing home automation systems or monitoring industrial equipment, understanding how to use remote IoT behind a router without MAC restrictions is essential for maximizing functionality and security. This comprehensive guide will walk you through every step, ensuring you can confidently set up and manage your IoT devices.
In today's interconnected world, IoT devices are everywhere, from smart thermostats to industrial sensors. However, accessing these devices remotely often presents challenges, especially when working behind routers with MAC filtering or firewalls. This article will demystify the process and provide actionable solutions to help you overcome these hurdles.
Whether you're a beginner or an experienced user, this guide is tailored to ensure you have all the information you need. From configuring your router settings to downloading necessary software, we'll cover everything step by step, ensuring you can achieve seamless remote IoT access.
Read also:Desiremovies Bollywood Your Ultimate Guide To The Best Of Indian Cinema
Understanding Remote IoT and Its Importance
What Is Remote IoT?
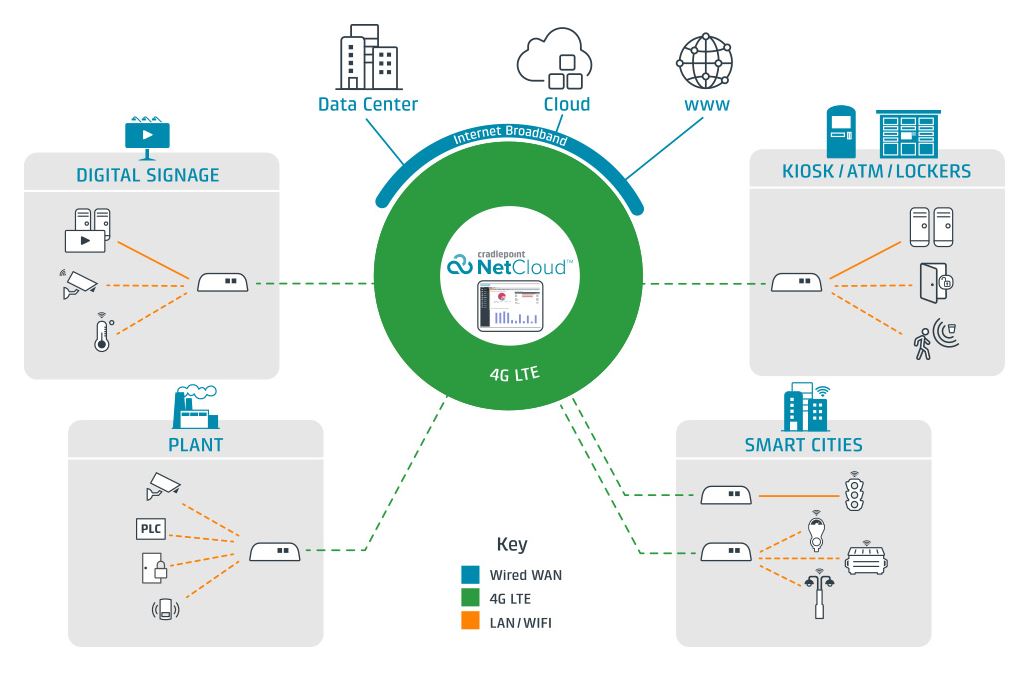
Remote IoT refers to the ability to control, monitor, and interact with Internet of Things devices from a distant location. These devices can range from simple home appliances to complex industrial machinery. The significance of remote IoT lies in its ability to enhance convenience, efficiency, and security in various applications.
- Remote IoT allows users to manage devices without physical presence.
- It improves operational efficiency by enabling real-time monitoring and adjustments.
- Security measures can be implemented to protect sensitive data and systems.
Why Is Remote IoT Behind a Router Important?
When IoT devices are connected to a network behind a router, they may face restrictions such as firewalls or MAC address filtering. Understanding how to configure your router settings is crucial for ensuring uninterrupted remote access. This section will delve into the importance of navigating these challenges and provide practical solutions.
Key Challenges in Remote IoT Access
MAC Address Filtering
MAC address filtering is a common security feature in routers that restricts network access to specific devices. While this enhances security, it can also hinder remote IoT functionality. By learning how to bypass or configure MAC filtering, you can maintain both security and accessibility.
Firewall Restrictions
Firewalls are another layer of security that can block unauthorized access to your network. However, they may also prevent legitimate remote IoT connections. This section will explore methods to configure firewall settings to allow safe remote access without compromising security.
Setting Up Remote IoT Behind a Router
Configuring Router Settings
Configuring your router is the first step in enabling remote IoT access. This involves adjusting settings such as port forwarding, DMZ, and dynamic DNS. Below are detailed steps to guide you through the process:
- Access your router's admin panel using its IP address.
- Locate the port forwarding section and set up the necessary ports for your IoT devices.
- Enable dynamic DNS to ensure consistent access to your network.
Port Forwarding Explained
Port forwarding directs incoming traffic from the internet to specific devices on your local network. This is essential for remote IoT access, as it ensures that requests reach the intended devices. We'll discuss how to identify the correct ports and set up forwarding rules effectively.
Read also:Kim Kardashian Siblings The Complete Guide To Their Lives Careers And Influence
Software Solutions for Remote IoT Access
Choosing the Right Software
Selecting the appropriate software is crucial for successful remote IoT implementation. Popular options include platforms like MQTT, Node-RED, and IoT Cloud Services. Each solution has its advantages, and this section will help you determine which one suits your needs best.
Free Download Options
Several free software solutions are available for remote IoT access. These tools offer robust features without the need for paid subscriptions. We'll provide a list of recommended downloads and guide you through the installation process.
Security Best Practices for Remote IoT
Implementing Strong Authentication
Security should always be a top priority when setting up remote IoT access. Implementing strong authentication methods, such as two-factor authentication (2FA), can significantly enhance protection against unauthorized access.
Regular Updates and Monitoring
Keeping your IoT devices and software up to date is vital for maintaining security. Regular monitoring can help detect and address potential vulnerabilities before they become serious issues.
Troubleshooting Common Issues
Connection Problems
Connection issues are a common challenge in remote IoT setups. This section will address common problems and provide troubleshooting tips to help you resolve them quickly and efficiently.
Network Configuration Errors
Errors in network configuration can prevent successful remote access. We'll walk you through identifying and correcting these mistakes to ensure smooth operation.
Case Studies and Real-World Applications
Successful Remote IoT Implementations
Learning from real-world examples can provide valuable insights into effective remote IoT strategies. This section will highlight successful implementations and the lessons learned from them.
Lessons Learned from Failures
Examining failures can be just as informative as studying successes. By understanding common pitfalls, you can avoid making the same mistakes and improve your remote IoT setup.
Future Trends in Remote IoT
Innovations in Remote IoT Technology
As technology continues to evolve, new innovations in remote IoT are emerging. From advanced AI-driven solutions to enhanced security protocols, staying informed about these developments is essential for staying ahead.
Preparing for the Future
To prepare for future advancements, it's important to adopt flexible and scalable solutions. This section will discuss strategies for ensuring your remote IoT setup remains relevant and effective in the years to come.
Conclusion
In conclusion, mastering how to use remote IoT behind a router without MAC restrictions involves understanding key concepts, configuring your network settings, and implementing robust security measures. By following the steps outlined in this guide, you can achieve seamless remote access to your IoT devices.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more valuable insights into IoT technology and its applications.
Table of Contents
- Understanding Remote IoT and Its Importance
- Key Challenges in Remote IoT Access
- Setting Up Remote IoT Behind a Router
- Software Solutions for Remote IoT Access
- Security Best Practices for Remote IoT
- Troubleshooting Common Issues
- Case Studies and Real-World Applications
- Future Trends in Remote IoT
- Conclusion