Managing IoT devices remotely while maintaining security is a growing challenge for businesses and tech enthusiasts alike. In this article, we will explore how to use remote IoT behind a firewall using a Mac server. Whether you're managing smart home devices or industrial sensors, understanding this setup will give you the tools to stay ahead in the connected world.
With the rapid expansion of the Internet of Things (IoT), the need for secure remote access has never been greater. Devices behind firewalls often require special configurations to ensure they can be accessed safely from outside the local network. This article dives deep into the process of configuring a Mac server to facilitate secure remote IoT communication.
By the end of this guide, you'll have a clear understanding of the technical steps involved, the security measures to implement, and best practices to follow. Let’s get started!
Read also:Andrea Brillantes Unveiling The Truth Behind The Controversy
Table of Contents:
- Introduction to Remote IoT Access
- Challenges of IoT Devices Behind Firewalls
- Overview of Mac Server for IoT
- Preparing Your Mac Server
- Configuring Firewall for Remote IoT Access
- Securing IoT Connections
- Implementing VPN Solutions
- Advanced Techniques for Remote IoT
- Troubleshooting Tips
- Best Practices for Secure IoT Access
Introduction to Remote IoT Access
The Internet of Things (IoT) has revolutionized the way we interact with technology. From smart homes to industrial automation, IoT devices are everywhere. However, accessing these devices remotely while ensuring security can be a challenge, especially when they are located behind firewalls.
Why Use a Mac Server for IoT?
A Mac server offers a robust platform for managing IoT devices. With macOS's built-in security features and ease of use, it is an excellent choice for setting up remote access solutions. Whether you're a small business owner or an individual tech enthusiast, leveraging a Mac server can streamline your IoT operations.
Key advantages include:
- Seamless integration with Apple ecosystem
- Advanced security features
- Reliable performance for IoT management
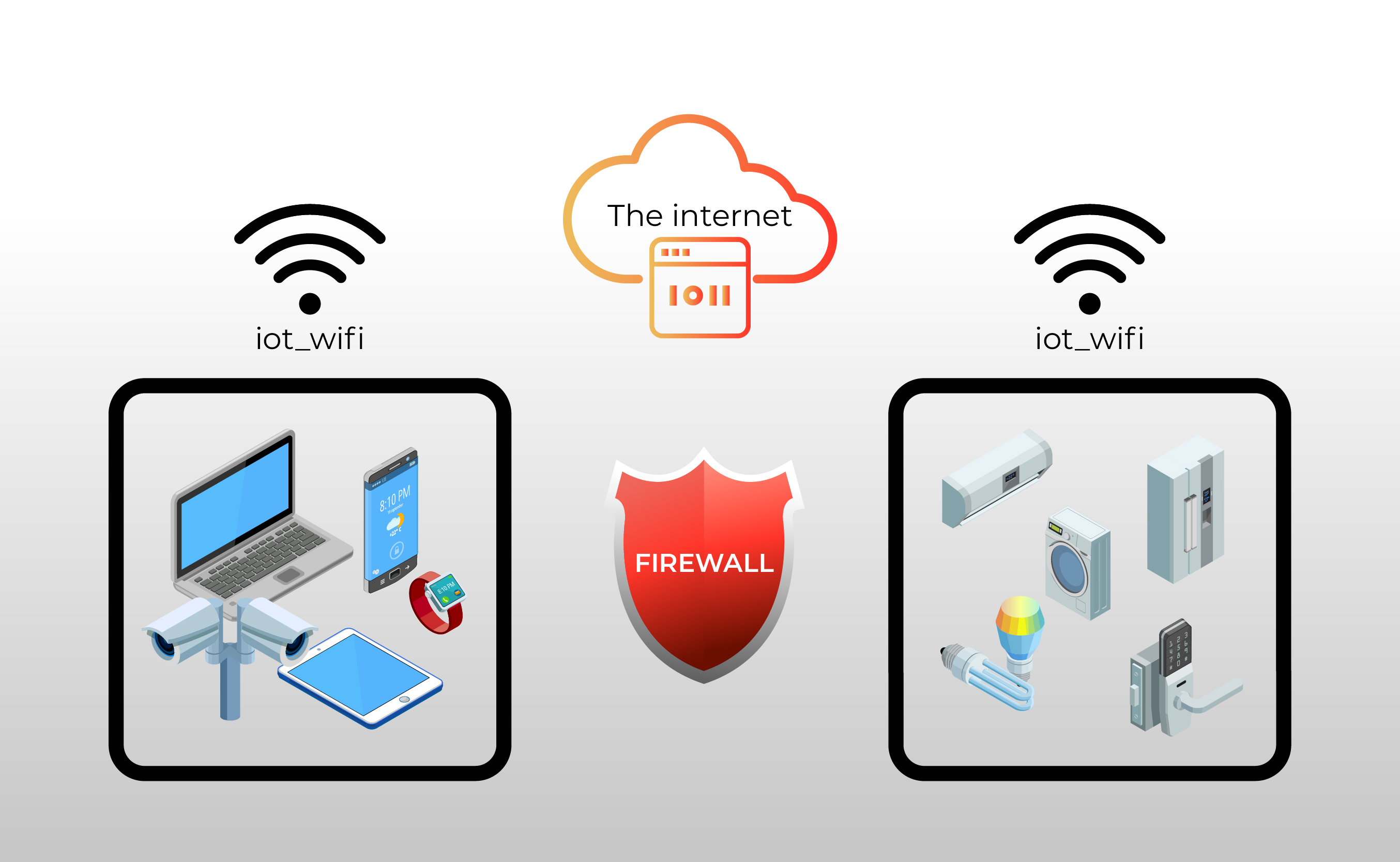
Challenges of IoT Devices Behind Firewalls
When IoT devices are located behind a firewall, they face several challenges that can hinder remote access:
Limited Access
Firewalls are designed to restrict unauthorized access, which can make it difficult to connect to IoT devices from outside the network. This limitation is essential for security but complicates remote management.
Read also:Hdhub 4u Your Ultimate Source For Highquality Movies And Entertainment
Security Risks
Opening ports in a firewall to allow remote access can expose the network to potential threats. It's crucial to implement strong security measures to mitigate these risks.
Key challenges include:
- Port forwarding vulnerabilities
- Unauthorized access attempts
- Data interception risks
Overview of Mac Server for IoT
A Mac server provides a powerful solution for managing IoT devices. With macOS Server, you can set up services such as file sharing, remote access, and automation, all tailored to your IoT needs.
Key Features of macOS Server
macOS Server offers several features that make it ideal for IoT management:
- Remote Access: Securely access your devices from anywhere.
- Automation: Schedule tasks and automate device management.
- Security: Built-in firewalls and encryption protocols.
By leveraging these features, you can create a secure and efficient environment for managing your IoT devices.
Preparing Your Mac Server
Before setting up remote access for IoT devices, you need to prepare your Mac server. This involves installing macOS Server, configuring basic settings, and ensuring your server is secure.
Step-by-Step Guide
Follow these steps to prepare your Mac server:
- Install macOS Server: Download and install macOS Server from the App Store.
- Configure Network Settings: Set up your server's network configuration to ensure stable connectivity.
- Enable Remote Management: Turn on remote management in System Preferences.
Once your server is set up, you can proceed to configure the firewall settings.
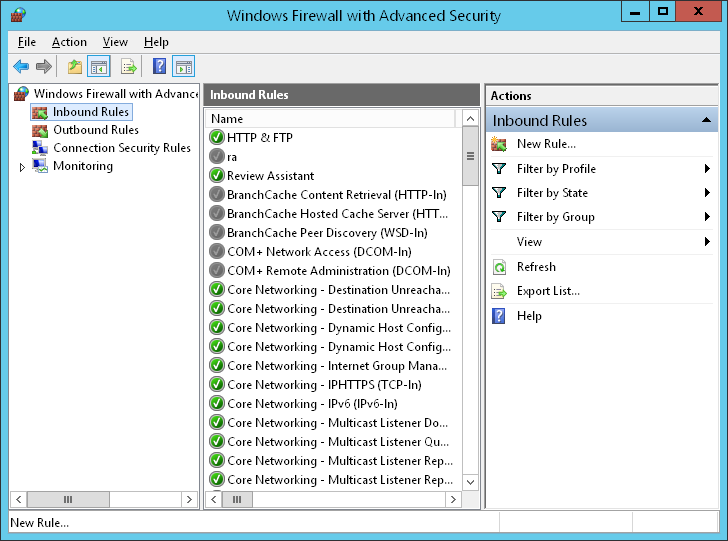
Configuring Firewall for Remote IoT Access
Configuring the firewall is a critical step in setting up remote IoT access. A well-configured firewall ensures that only authorized connections are allowed, minimizing security risks.
Best Practices for Firewall Configuration
Here are some best practices to follow:
- Use Specific Rules: Create rules that only allow traffic from trusted IP addresses.
- Limit Port Access: Open only the necessary ports for IoT communication.
- Regularly Update Rules: Keep your firewall rules up to date to address new threats.
By following these practices, you can ensure that your firewall is both secure and effective.
Securing IoT Connections
Securing IoT connections is essential for protecting your devices and data. There are several methods you can use to enhance security, including encryption and authentication.
Encryption Methods
Implementing encryption is a key step in securing IoT connections:
- SSL/TLS: Use SSL/TLS protocols to encrypt data transmitted between devices.
- SSH Tunneling: Set up SSH tunnels for secure communication.
Authentication protocols such as OAuth and API keys can also be used to verify the identity of devices and users.
Implementing VPN Solutions
Using a Virtual Private Network (VPN) is one of the most effective ways to secure remote IoT access. A VPN creates a secure tunnel between your devices and the server, ensuring that all communication is encrypted.
Choosing the Right VPN
When selecting a VPN solution, consider the following factors:
- Performance: Choose a VPN that offers high-speed connections.
- Security Features: Look for advanced encryption and security protocols.
- Compatibility: Ensure the VPN is compatible with your devices and operating systems.
By implementing a reliable VPN, you can significantly enhance the security of your IoT setup.
Advanced Techniques for Remote IoT
For those looking to take their IoT management to the next level, there are several advanced techniques you can explore. These include using cloud services, implementing IoT platforms, and automating device management.
Cloud Integration
Integrating your IoT setup with cloud services can provide several benefits:
- Scalability: Easily scale your operations as needed.
- Data Storage: Store and analyze large amounts of data in the cloud.
- Remote Access: Access your devices from anywhere with an internet connection.
Platforms like AWS IoT and Google Cloud IoT offer robust solutions for managing IoT devices in the cloud.
Troubleshooting Tips
Even with a well-configured setup, issues can arise. Here are some troubleshooting tips to help you resolve common problems:
Common Issues and Solutions
- Connection Problems: Check firewall rules and ensure the correct ports are open.
- Device Failures: Verify device settings and firmware updates.
- Security Alerts: Investigate any unusual activity and update security measures as needed.
By addressing these issues promptly, you can maintain a stable and secure IoT environment.
Best Practices for Secure IoT Access
To ensure the long-term success of your IoT setup, follow these best practices:
Maintain Security
- Regular Updates: Keep your server and devices up to date with the latest security patches.
- Monitor Activity: Regularly review logs and monitor for suspicious activity.
- Backup Data: Regularly back up important data to prevent loss in case of failure.
By adhering to these practices, you can create a secure and reliable IoT setup that meets your needs.
Kesimpulan
In conclusion, setting up remote IoT access behind a firewall using a Mac server involves several key steps. From preparing your server to configuring the firewall and implementing security measures, each step is crucial for ensuring a secure and efficient setup.
We encourage you to take action by:
- Implementing the techniques discussed in this article.
- Sharing your experience and insights in the comments below.
- Exploring additional resources and articles on our site for more information.
Thank you for reading, and we hope this guide helps you achieve your IoT management goals!