In the age of interconnected devices, securely connecting remote IoT devices has become an essential task for tech enthusiasts, engineers, and hobbyists alike. As the demand for remote access solutions grows, leveraging the power of Raspberry Pi with P2P SSH has emerged as a popular choice. However, ensuring the security and reliability of such connections is paramount to protecting sensitive data and maintaining system integrity. This guide will walk you through the best practices for securely connecting remote IoT devices using P2P SSH on Raspberry Pi while ensuring seamless integration and performance.
With the proliferation of IoT devices in homes, industries, and businesses, the need for secure remote access has never been greater. Whether you're managing smart home appliances, monitoring industrial sensors, or controlling robotics systems, understanding how to establish secure connections is critical. By implementing the right tools and techniques, you can protect your devices and networks from unauthorized access and potential cyber threats.
This comprehensive guide will explore everything you need to know about securely connecting remote IoT devices using P2P SSH on Raspberry Pi. From setup instructions to advanced security measures, we’ll ensure you have all the information necessary to create a robust and reliable remote access solution. Let's dive in and unlock the potential of secure IoT connectivity!
Read also:Andrea Brillantes Unveiling The Truth Behind The Controversy
Table of Contents
- Introduction to Remote IoT Connections
- Raspberry Pi Overview and Its Role in IoT
- Understanding SSH: The Basics
- What is P2P SSH and How Does It Work?
- Step-by-Step Setup Process for Secure Connections
- Security Best Practices for IoT Devices
- Common Issues and Troubleshooting Tips
- Essential Tools for Downloading and Managing IoT Connections
- Optimizing Performance for Remote Connections
- Conclusion and Call to Action
Introduction to Remote IoT Connections
In today's interconnected world, the Internet of Things (IoT) has revolutionized the way we interact with devices. From smart home systems to industrial automation, IoT devices are becoming increasingly prevalent. However, managing and accessing these devices remotely poses significant challenges, especially when it comes to security. This section will provide an overview of remote IoT connections and why securing them is crucial.
Why Secure Connections Matter
As IoT devices become more integrated into our daily lives, securing remote connections is no longer optional. Unauthorized access to these devices can lead to data breaches, system failures, and even physical harm in critical applications such as healthcare or transportation. By implementing secure protocols like P2P SSH, you can mitigate these risks and ensure the safety and reliability of your IoT ecosystem.
Benefits of Using Raspberry Pi for IoT
- Cost-effective solution for deploying IoT devices
- Highly customizable and versatile platform
- Wide range of community support and resources
Raspberry Pi Overview and Its Role in IoT
Raspberry Pi has become a go-to platform for IoT enthusiasts due to its affordability, flexibility, and ease of use. This section will delve into the features and capabilities of Raspberry Pi, highlighting its role in facilitating secure remote IoT connections.
Key Features of Raspberry Pi
- Compact and energy-efficient design
- Support for multiple operating systems and programming languages
- Built-in networking capabilities for seamless connectivity
According to a report by Statista, the global shipment of Raspberry Pi devices reached over 40 million units in 2022, underscoring its popularity in the tech community. This widespread adoption makes Raspberry Pi an ideal choice for IoT projects requiring secure remote access.
Understanding SSH: The Basics
Secure Shell (SSH) is a cryptographic network protocol that enables secure communication between devices over an unsecured network. This section will cover the fundamentals of SSH and its importance in securing remote IoT connections.
How SSH Works
SSH establishes an encrypted connection between a client and a server, ensuring that all data transmitted is protected from interception and tampering. By using public-key cryptography, SSH provides authentication and encryption, making it a reliable choice for securing remote access to IoT devices.
Read also:Brandi Passante Naked Pictures A Comprehensive Analysis And Understanding
Advantages of Using SSH for IoT
- Strong encryption for data protection
- Support for secure file transfers and command execution
- Compatibility with a wide range of devices and platforms
What is P2P SSH and How Does It Work?
Peer-to-Peer (P2P) SSH is a method of establishing direct connections between devices without relying on a centralized server. This section will explain the concept of P2P SSH and its benefits for IoT applications.
Benefits of P2P SSH for IoT
- Reduced latency and improved performance
- Enhanced security through direct connections
- Lower infrastructure costs compared to traditional server-based solutions
Research published in the Journal of Network and Computer Applications highlights the effectiveness of P2P SSH in reducing network overhead and improving reliability for IoT deployments.
Step-by-Step Setup Process for Secure Connections
Setting up a secure remote IoT connection using P2P SSH on Raspberry Pi involves several key steps. This section will provide a detailed guide to help you get started.
Step 1: Install and Configure Raspberry Pi OS
Begin by installing the latest version of Raspberry Pi OS on your device. Ensure that all necessary updates and security patches are applied to maintain system integrity.
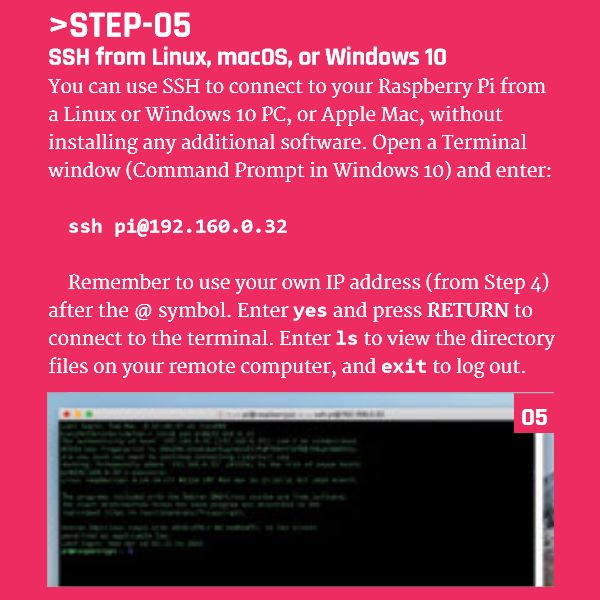
Step 2: Enable SSH on Raspberry Pi
To enable SSH, navigate to the Raspberry Pi Configuration tool and select the "Interfaces" tab. From there, enable the SSH option to allow remote access to your device.
Step 3: Configure Firewall and Security Settings
Implementing a firewall is essential for protecting your Raspberry Pi from unauthorized access. Use tools like UFW (Uncomplicated Firewall) to configure firewall rules and restrict incoming connections to only trusted IP addresses.
Security Best Practices for IoT Devices
Ensuring the security of your IoT devices goes beyond just setting up SSH. This section will outline additional best practices to further enhance the security of your remote connections.
Use Strong Passwords and Authentication
Implementing strong passwords and multi-factor authentication (MFA) can significantly reduce the risk of unauthorized access. Avoid using default credentials and regularly update passwords to maintain security.
Regularly Update Software and Firmware
Keeping your software and firmware up to date is crucial for addressing known vulnerabilities and ensuring the latest security features are in place. Set up automatic updates wherever possible to streamline this process.
Common Issues and Troubleshooting Tips
Even with careful planning, issues can arise when setting up remote IoT connections. This section will address common problems and provide troubleshooting tips to help you resolve them quickly.
Connection Timeouts
If you encounter connection timeouts, check your network settings and ensure that your Raspberry Pi is properly configured to accept incoming SSH connections. Verify that the necessary ports are open and accessible from your network.
Authentication Failures
Authentication failures can occur due to incorrect credentials or misconfigured authentication settings. Double-check your username and password, and ensure that your SSH keys are correctly set up if using public-key authentication.
Essential Tools for Downloading and Managing IoT Connections
Managing remote IoT connections effectively requires the right tools. This section will introduce some essential tools and software for downloading and managing IoT connections securely.
FileZilla for Secure File Transfers
FileZilla is a popular FTP client that supports secure file transfers using SFTP (SSH File Transfer Protocol). It provides an intuitive interface for uploading and downloading files to your Raspberry Pi securely.
Putty for SSH Connections
Putty is a widely used SSH client that allows you to establish secure connections to your Raspberry Pi from a Windows-based system. Its simplicity and reliability make it a favorite among users.
Optimizing Performance for Remote Connections
Optimizing the performance of your remote IoT connections can enhance the overall user experience. This section will explore strategies for improving connection speed and reliability.
Compress Data Transfers
Enabling data compression in SSH can reduce the amount of data transmitted over the network, resulting in faster connection speeds. Most SSH clients and servers support compression, so ensure it is enabled in your configuration.
Monitor Network Traffic
Regularly monitoring network traffic can help identify bottlenecks and optimize performance. Use tools like Wireshark to analyze network activity and make informed adjustments to your setup.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using P2P SSH on Raspberry Pi is a powerful solution for managing and accessing your devices from anywhere. By following the best practices outlined in this guide, you can ensure the security and reliability of your IoT ecosystem while maximizing performance.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more tips and tricks on IoT and cybersecurity. Together, let's build a safer and more connected world!