In today's interconnected world, securely connecting remote IoT devices to AWS VPC is a critical task for businesses and developers. As more devices become connected, the need for secure communication channels grows exponentially. In this article, we will explore the best practices, tools, and techniques to ensure your IoT devices are securely integrated into your AWS Virtual Private Cloud (VPC).
IoT technology has revolutionized industries, enabling real-time data collection, automation, and enhanced operational efficiency. However, as these devices operate across various networks and environments, securing their connections becomes a top priority. This guide will walk you through the essential steps to protect your IoT ecosystem within AWS VPC.
By the end of this article, you will have a solid understanding of the tools and strategies required to ensure the security of your IoT devices while leveraging the robust infrastructure of AWS VPC. Let's dive in!
Read also:Brandi Passante Naked Pictures A Comprehensive Analysis And Understanding
Table of Contents
- Introduction to IoT and AWS VPC
- Why Secure IoT Connections Are Essential
- AWS VPC Basics
- Secure Connection Methods for IoT Devices
- Best Practices for Securing IoT Devices
- Using AWS Security Features
- Common Security Challenges
- Step-by-Step Guide to Secure IoT Connections
- Case Studies
- The Future of IoT Security
Introduction to IoT and AWS VPC
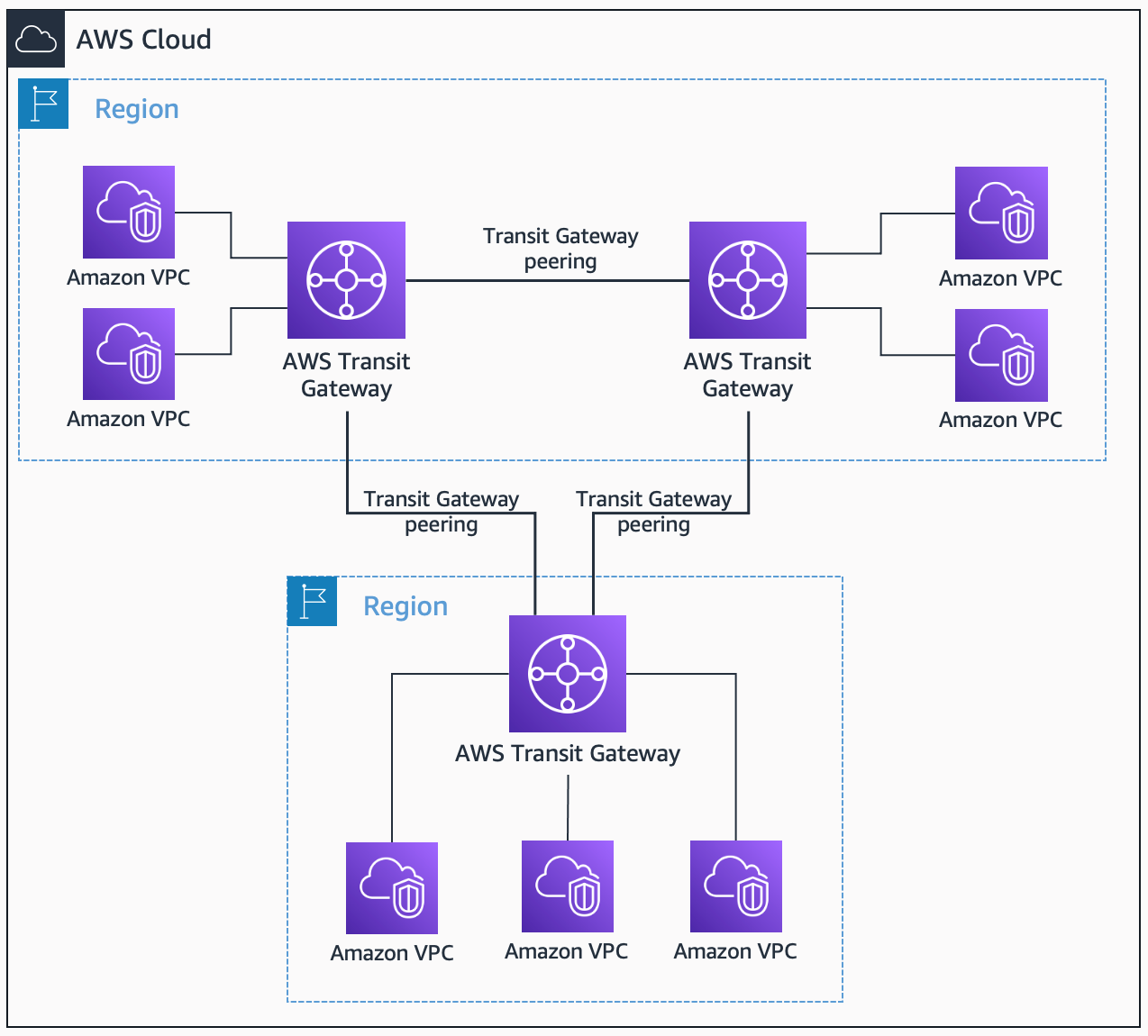
The Internet of Things (IoT) has transformed the way businesses operate, enabling seamless communication between devices and systems. AWS Virtual Private Cloud (VPC) provides a secure and scalable environment for hosting IoT applications. By integrating IoT devices into AWS VPC, organizations can ensure robust security, high availability, and efficient data management.
AWS VPC allows you to create an isolated network environment where you can launch AWS resources, including IoT devices. This isolation ensures that your devices are protected from unauthorized access and potential threats.
Understanding the basics of AWS VPC is crucial for setting up a secure IoT infrastructure. This section will explore the key components of AWS VPC and how they contribute to securing IoT connections.
Why Secure IoT Connections Are Essential
IoT devices are often deployed in remote locations, making them vulnerable to cyberattacks. Ensuring secure connections is vital to protect sensitive data and maintain the integrity of your IoT ecosystem. Below are some reasons why securing IoT connections is essential:
- Data Protection: IoT devices often transmit sensitive information, such as user data or operational metrics. Secure connections prevent unauthorized access to this data.
- Device Integrity: Protecting IoT devices from malware and unauthorized access ensures they function as intended.
- Compliance: Many industries have strict regulations regarding data security. Securing IoT connections helps organizations meet these compliance requirements.
AWS VPC Basics
AWS VPC is a fundamental component of AWS infrastructure, providing a secure and customizable networking environment. Below are the key features of AWS VPC:
Key Components of AWS VPC
- Subnets: Subnets divide your VPC into smaller segments, allowing you to control traffic flow and isolate resources.
- Security Groups: Security groups act as virtual firewalls, controlling inbound and outbound traffic to your instances.
- Network Access Control Lists (NACLs): NACLs provide an additional layer of security by filtering traffic at the subnet level.
By leveraging these components, you can create a secure and efficient environment for your IoT devices.
Read also:Desiremovies Movies Bollywood Your Ultimate Guide To Bollywood Cinema
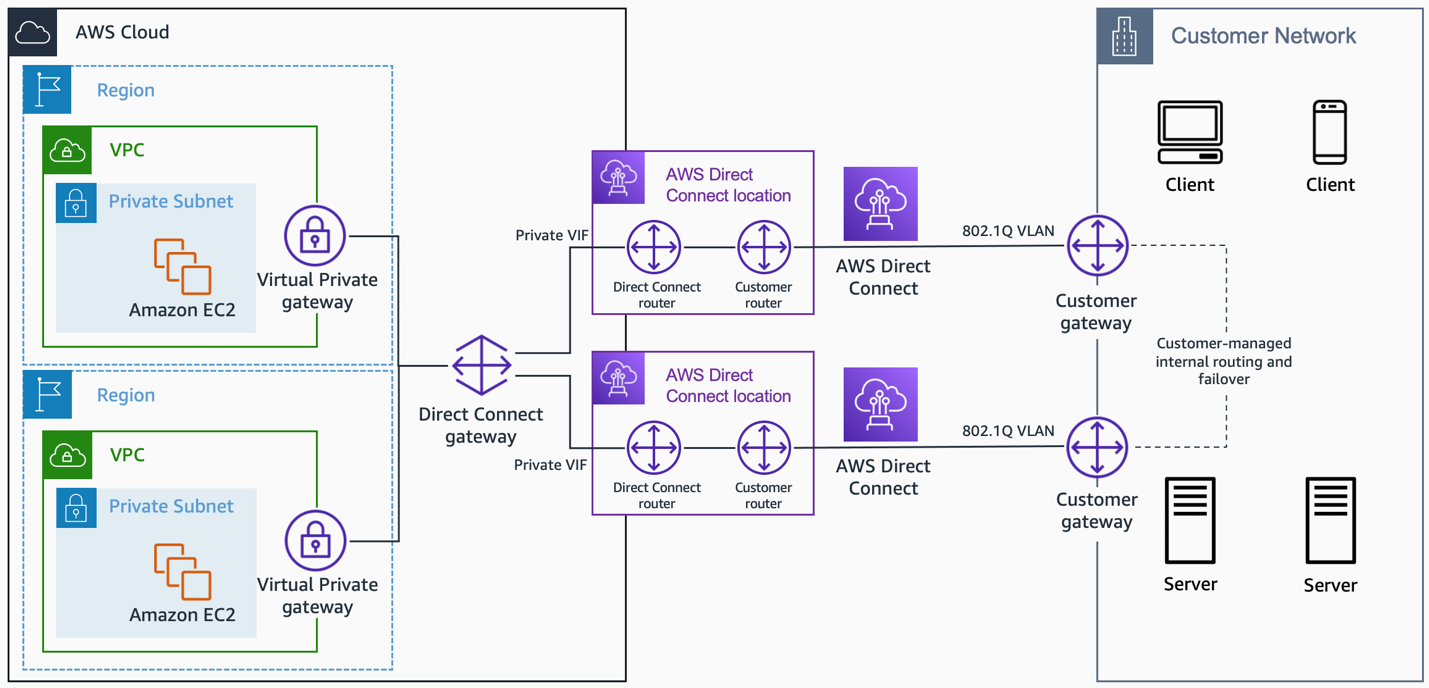
Secure Connection Methods for IoT Devices
Securing IoT connections involves implementing robust authentication, encryption, and monitoring mechanisms. Below are some of the most effective methods for securing IoT devices in AWS VPC:
TLS Encryption
Transport Layer Security (TLS) is a widely used protocol for securing data transmission. By enabling TLS encryption, you can ensure that all communication between IoT devices and AWS VPC is protected.
Device Authentication
Implementing strong authentication mechanisms, such as X.509 certificates or AWS IoT Core authentication, ensures that only authorized devices can access your VPC.
Best Practices for Securing IoT Devices
Adopting best practices is essential for maintaining the security of your IoT ecosystem. Below are some key practices to follow:
- Regular Updates: Keep your IoT devices and firmware up to date to address known vulnerabilities.
- Least Privilege Principle: Grant devices only the permissions they need to perform their functions.
- Monitoring and Logging: Implement continuous monitoring and logging to detect and respond to potential security threats.
Using AWS Security Features
AWS provides a range of security features to help protect your IoT devices. Below are some of the most useful features:
AWS IoT Core
AWS IoT Core enables secure and reliable communication between IoT devices and AWS services. It supports device authentication, encryption, and message routing.
AWS Shield
AWS Shield protects your applications from Distributed Denial of Service (DDoS) attacks, ensuring uninterrupted service delivery.
Common Security Challenges
Securing IoT devices in AWS VPC comes with its own set of challenges. Below are some common challenges and how to address them:
- Device Scalability: As the number of IoT devices grows, managing security becomes more complex. Use automated tools and policies to streamline security management.
- Data Privacy: Ensure compliance with data privacy regulations by implementing encryption and access controls.
Step-by-Step Guide to Secure IoT Connections
Below is a step-by-step guide to securely connect IoT devices to AWS VPC:
- Create a VPC and configure subnets, security groups, and NACLs.
- Register IoT devices in AWS IoT Core and configure authentication.
- Enable TLS encryption for all device communications.
- Set up monitoring and logging to detect and respond to security incidents.
Case Studies
Real-world examples can provide valuable insights into securing IoT devices in AWS VPC. Below are two case studies:
Case Study 1: Smart Agriculture
Agricultural company X implemented IoT sensors to monitor soil moisture levels. By securely connecting these sensors to AWS VPC, they ensured real-time data collection and analysis, improving crop yield and reducing water usage.
Case Study 2: Industrial Automation
Manufacturing company Y integrated IoT devices into their production lines. Using AWS IoT Core and VPC security features, they achieved seamless and secure communication between devices, enhancing operational efficiency.
The Future of IoT Security
As IoT technology continues to evolve, so do the security challenges. Emerging trends such as edge computing and artificial intelligence will play a significant role in enhancing IoT security. Organizations must stay informed and adapt to these changes to maintain the security of their IoT ecosystems.
Kesimpulan
Securing IoT devices in AWS VPC is a multifaceted task that requires a combination of best practices, tools, and strategies. By implementing the methods and techniques outlined in this article, you can ensure the security and reliability of your IoT ecosystem.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site to deepen your understanding of IoT and cloud security. Together, we can build a safer and more connected world.
For further reading, refer to the following resources: