In today's rapidly evolving digital landscape, remote IoT (Internet of Things) management through Virtual Private Cloud (VPC) and Secure Shell (SSH) has become a critical component for businesses and tech enthusiasts alike. RemoteIoT VPC SSH allows users to securely access and manage IoT devices from anywhere in the world, providing unparalleled flexibility and control. Whether you're a developer, network administrator, or a tech-savvy individual, understanding how to leverage this technology can significantly enhance your operational efficiency.
With the rise of IoT devices, ensuring secure and reliable communication has become more important than ever. RemoteIoT VPC SSH not only addresses these concerns but also offers a robust framework for managing complex networks. This article aims to provide an in-depth exploration of the topic, covering everything from the basics to advanced techniques, ensuring that you have all the tools needed to succeed in this domain.
Whether you're looking to implement VPC SSH for your IoT devices or simply want to expand your knowledge, this guide is tailored to meet your needs. By the end of this article, you'll have a comprehensive understanding of RemoteIoT VPC SSH and how it can be applied to enhance your network security and efficiency.
Read also:Mastering Remoteiot Platform Ssh Raspberry Pi Download Free A Comprehensive Guide
Table of Contents
Introduction to RemoteIoT VPC SSH
Why VPC is Essential for Remote IoT
Understanding SSH in IoT Environments
How to Set Up VPC for Remote IoT Devices
Securing Your RemoteIoT VPC with SSH
Best Practices for RemoteIoT VPC SSH
Read also:Kim Kardashian Siblings The Complete Guide To Their Lives Careers And Influence
Common Challenges and Solutions
Integrating RemoteIoT VPC SSH with Cloud Services
Case Studies of RemoteIoT VPC SSH
Future Trends in RemoteIoT VPC SSH
Introduction to RemoteIoT VPC SSH
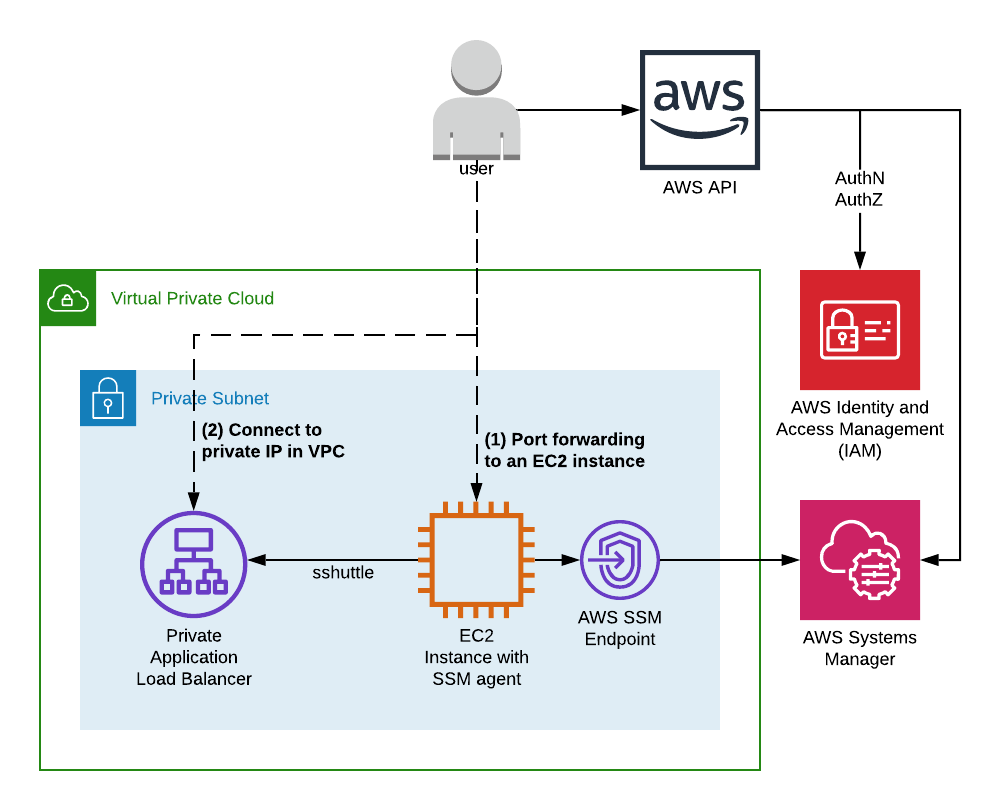
The concept of RemoteIoT VPC SSH revolves around creating a secure and isolated network environment for managing IoT devices. A Virtual Private Cloud (VPC) acts as a private space within a cloud provider's infrastructure, enabling users to deploy and manage resources securely. SSH, on the other hand, provides an encrypted channel for communication between devices, ensuring data integrity and confidentiality.
By combining VPC and SSH, organizations can establish a robust framework for remote IoT management. This setup not only enhances security but also simplifies the administration of IoT devices. Whether you're dealing with smart home devices, industrial sensors, or wearable technology, RemoteIoT VPC SSH offers a scalable solution that caters to diverse needs.
What is VPC?
A Virtual Private Cloud (VPC) is a logically isolated section of a cloud provider's infrastructure. It allows users to define their own network topology, including subnets, IP address ranges, and routing tables. By implementing a VPC, organizations can create a secure environment for their IoT devices, protecting them from unauthorized access and potential threats.
Why Use SSH for IoT Devices?
Secure Shell (SSH) is a cryptographic network protocol that ensures secure communication between devices. When applied to IoT environments, SSH provides a reliable means of accessing and managing devices remotely. Its encryption capabilities protect sensitive data from interception and tampering, making it an ideal choice for securing IoT networks.
Why VPC is Essential for Remote IoT
In the realm of IoT, security is a top priority. With billions of connected devices exchanging data, the risk of cyberattacks increases exponentially. A Virtual Private Cloud (VPC) plays a crucial role in mitigating these risks by providing a secure and isolated environment for IoT devices.
By deploying IoT devices within a VPC, organizations can control access to their networks, ensuring that only authorized users can interact with the devices. Additionally, VPCs enable the implementation of advanced security features, such as firewalls and intrusion detection systems, further enhancing the protection of IoT networks.
Key Benefits of Using VPC for IoT
- Enhanced security through isolation and access control
- Scalability to accommodate growing numbers of IoT devices
- Flexibility in configuring network settings and resources
- Improved performance through optimized routing and resource allocation
Understanding SSH in IoT Environments
Secure Shell (SSH) is a fundamental tool for managing IoT devices remotely. It establishes an encrypted connection between devices, ensuring that sensitive data is transmitted securely. In IoT environments, where devices are often deployed in diverse locations, SSH provides a reliable means of accessing and managing these devices without compromising security.
SSH operates on a client-server model, where a client initiates a connection to a server. This connection is encrypted using advanced cryptographic algorithms, making it nearly impossible for attackers to intercept or decipher the data being transmitted. By leveraging SSH, organizations can confidently manage their IoT devices, knowing that their communications are protected.
How SSH Works in IoT Networks
When an SSH connection is established, several steps occur to ensure secure communication:
- Authentication: The client and server verify each other's identities using public key cryptography.
- Encryption: Data is encrypted using a symmetric key algorithm, ensuring confidentiality during transmission.
- Integrity: A message authentication code (MAC) is used to verify the integrity of the transmitted data.
How to Set Up VPC for Remote IoT Devices
Setting up a Virtual Private Cloud (VPC) for remote IoT devices involves several key steps. First, you need to define your network topology, including subnets, IP address ranges, and routing tables. This ensures that your IoT devices are properly organized and can communicate effectively within the VPC.
Next, you should configure security groups and network access control lists (ACLs) to control inbound and outbound traffic. These settings help protect your IoT devices from unauthorized access and potential threats. Finally, you can deploy your IoT devices within the VPC, ensuring that they are securely integrated into your network.
Step-by-Step Guide to Setting Up VPC
- Define your network topology and IP address ranges.
- Create subnets and configure routing tables.
- Set up security groups and network ACLs.
- Deploy IoT devices within the VPC.
Securing Your RemoteIoT VPC with SSH
Once your VPC is set up, securing it with SSH is the next critical step. SSH provides an additional layer of protection by encrypting all communications between devices. To implement SSH in your RemoteIoT VPC, you need to configure SSH servers on your IoT devices and ensure that they are accessible only through secure channels.
It's also important to manage SSH keys effectively, ensuring that they are stored securely and rotated regularly. By following best practices for SSH configuration and key management, you can significantly enhance the security of your RemoteIoT VPC.
Best Practices for SSH Configuration
- Use strong, unique passwords for SSH authentication.
- Disable password-based authentication and rely solely on public key authentication.
- Limit SSH access to trusted IP addresses and networks.
- Regularly update SSH software and apply security patches.
Best Practices for RemoteIoT VPC SSH
Implementing RemoteIoT VPC SSH requires adherence to best practices to ensure optimal performance and security. These practices include regular monitoring of network activity, maintaining up-to-date software, and conducting regular security audits. By following these guidelines, organizations can minimize risks and maximize the benefits of their RemoteIoT VPC SSH setup.
Additionally, it's important to educate team members about the importance of security and the proper use of SSH. Training sessions and workshops can help ensure that everyone involved in managing IoT devices understands the significance of adhering to security protocols.
Key Best Practices for RemoteIoT VPC SSH
- Regularly monitor network activity for suspicious behavior.
- Keep all software and firmware up to date with the latest security patches.
- Conduct regular security audits to identify and address potential vulnerabilities.
- Provide ongoing training and education for team members.
Common Challenges and Solutions
Despite the many advantages of RemoteIoT VPC SSH, there are challenges that organizations may encounter. These challenges can range from technical issues, such as configuration errors, to broader concerns, such as maintaining compliance with industry standards. Understanding these challenges and their solutions is essential for successful implementation.
One common challenge is managing SSH keys effectively. Organizations must ensure that keys are stored securely and rotated regularly to prevent unauthorized access. Another challenge is ensuring that all devices within the VPC are properly configured and maintained. Regular updates and security audits can help address these issues.
Solutions to Common Challenges
- Implement centralized key management systems for secure storage and rotation of SSH keys.
- Automate updates and security audits to reduce manual workload and improve consistency.
- Establish clear policies and procedures for managing IoT devices and networks.
Integrating RemoteIoT VPC SSH with Cloud Services
Integrating RemoteIoT VPC SSH with cloud services can further enhance the capabilities of your IoT network. Cloud platforms, such as AWS, Google Cloud, and Microsoft Azure, offer a wide range of tools and services that can be leveraged to optimize your VPC and SSH setup. By combining these services with your RemoteIoT VPC SSH, you can achieve greater scalability, flexibility, and security.
Some popular cloud services for IoT include AWS IoT Core, Google Cloud IoT Core, and Azure IoT Hub. These services provide features such as device management, data analytics, and integration with other cloud services, making them invaluable for managing large-scale IoT networks.
Benefits of Integrating with Cloud Services
- Increased scalability and flexibility for managing IoT devices.
- Access to advanced analytics and machine learning capabilities.
- Integration with other cloud services for enhanced functionality.
Case Studies of RemoteIoT VPC SSH
Several organizations have successfully implemented RemoteIoT VPC SSH to manage their IoT networks. These case studies highlight the benefits and challenges of adopting this technology and provide valuable insights for others considering similar implementations.
One notable example is a manufacturing company that used RemoteIoT VPC SSH to secure its industrial IoT network. By implementing VPC and SSH, the company was able to enhance the security of its operations, reduce downtime, and improve overall efficiency. Another example is a smart city initiative that leveraged RemoteIoT VPC SSH to manage its network of sensors and devices, ensuring reliable and secure communication across the city.
Key Takeaways from Case Studies
- RemoteIoT VPC SSH can significantly enhance the security and efficiency of IoT networks.
- Successful implementations require careful planning, configuration, and ongoing management.
- Integration with cloud services can further enhance the capabilities of RemoteIoT VPC SSH setups.
Future Trends in RemoteIoT VPC SSH
As technology continues to evolve, the future of RemoteIoT VPC SSH looks promising. Emerging trends, such as edge computing, artificial intelligence, and quantum cryptography, are expected to shape the landscape of IoT security and management. Organizations that stay ahead of these trends will be better positioned to leverage the full potential of RemoteIoT VPC SSH.
Edge computing, for example, offers the potential to process data closer to the source, reducing latency and improving performance. Artificial intelligence can enhance security by detecting and responding to threats in real-time. Quantum cryptography promises to revolutionize encryption, providing unparalleled security for IoT communications.
Preparing for the Future
- Stay informed about emerging technologies and their potential impact on IoT security.
- Invest