As the world becomes increasingly connected, the need for secure remote access to IoT devices is more critical than ever. With the rise of smart homes, industrial automation, and remote monitoring systems, the best remote IoT device SSH solutions have become indispensable. Secure Shell (SSH) technology provides encrypted communication between devices, ensuring data remains safe from cyber threats. In this article, we will explore the top remote IoT device SSH solutions, their benefits, and how they can transform the way you manage your connected devices.
The Internet of Things (IoT) has revolutionized the way we interact with technology. From smart thermostats to industrial sensors, IoT devices are designed to improve efficiency and convenience. However, managing these devices remotely requires a secure and reliable solution. This is where SSH comes into play, offering robust encryption and authentication mechanisms to protect your data and systems.
Whether you're a tech enthusiast, a business owner, or an IT professional, understanding the best remote IoT device SSH options is essential for ensuring the security and functionality of your connected ecosystem. In this comprehensive guide, we'll delve into the features, benefits, and considerations for selecting the right SSH solution for your IoT devices.
Read also:Kim Howard Unveiling The Life Achievements And Legacy Of A Remarkable Individual
What is Remote IoT Device SSH?
Remote IoT device SSH refers to the use of Secure Shell (SSH) protocols to establish secure communication with Internet of Things (IoT) devices from a remote location. SSH is a cryptographic network protocol that provides secure data communication, strong authentication, and integrity protection. It is widely used in IT environments for managing servers, routers, and other network devices, but its application in IoT has become increasingly significant.
IoT devices often operate in unsecured environments, making them vulnerable to cyberattacks. By implementing SSH, users can remotely access and manage these devices without compromising their security. SSH encrypts all data transmitted between the client and server, ensuring that sensitive information remains confidential and protected from unauthorized access.
Why SSH is Crucial for IoT Devices
SSH plays a vital role in securing IoT devices for several reasons:
- Encryption: SSH encrypts all data packets exchanged between the client and server, preventing eavesdropping and data interception.
- Authentication: SSH uses public-key cryptography to verify the identity of both the client and server, ensuring that only authorized users can access the system.
- Integrity Protection: SSH ensures that data transmitted between devices has not been tampered with during transit.
- Scalability: SSH can be used to manage multiple IoT devices simultaneously, making it suitable for large-scale deployments.
Top 10 Best Remote IoT Device SSH Solutions
1. OpenSSH
OpenSSH is one of the most widely used SSH solutions for managing IoT devices. It is open-source, highly customizable, and compatible with a wide range of operating systems. OpenSSH provides robust encryption and authentication mechanisms, making it an ideal choice for securing IoT devices.
Key features of OpenSSH include:
- Support for AES, RSA, and ECC encryption algorithms
- Two-factor authentication
- Port forwarding for secure tunneling
2. PuTTY
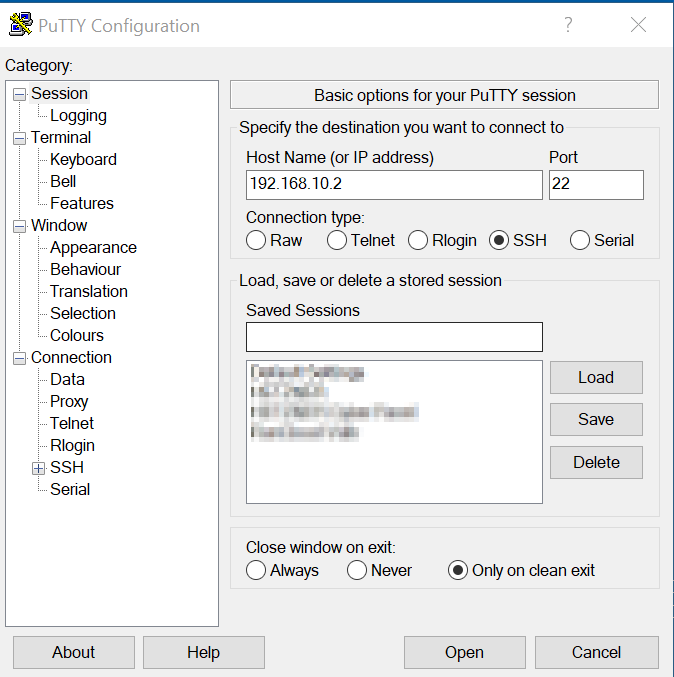
PuTTY is a popular SSH client for Windows users. It is lightweight, easy to use, and offers a range of configuration options for managing remote IoT devices. PuTTY supports various encryption protocols and can be used to establish secure connections to IoT devices over the internet.
Read also:Hdhub4u App Download Your Ultimate Guide To Accessing Highquality Movies
Advantages of PuTTY:
- Free and open-source
- Supports SSH, Telnet, and serial connections
- Customizable interface
3. MobaXterm
MobaXterm is an advanced SSH client that combines the features of a terminal emulator, network scanner, and remote desktop client. It is particularly useful for managing IoT devices in enterprise environments, offering a user-friendly interface and powerful tools for network monitoring.
Key benefits of MobaXterm:
- Support for multiple protocols, including SSH, FTP, and RDP
- Built-in network tools for troubleshooting
- Session management for easy access to multiple devices
4. Bitvise SSH Client
Bitvise SSH Client is a feature-rich solution for managing IoT devices securely. It offers advanced encryption algorithms, support for public-key authentication, and seamless integration with Windows environments. Bitvise is particularly popular among IT professionals for its ease of use and reliability.
Notable features of Bitvise:
- Support for SFTP and SCP file transfer
- Two-factor authentication
- Customizable security settings
5. Tera Term
Tera Term is a versatile SSH client that supports a wide range of communication protocols. It is lightweight, easy to install, and offers a range of plugins for extending its functionality. Tera Term is an excellent choice for managing IoT devices in both personal and professional settings.
Advantages of Tera Term:
- Support for SSH, Telnet, and serial connections
- Scripting capabilities for automation
- Extensible through plugins
6. SecureCRT
SecureCRT is a powerful SSH client designed for managing large-scale IoT deployments. It offers advanced features such as session management, scripting, and automation, making it an ideal choice for enterprise environments. SecureCRT supports multiple protocols and provides robust encryption for secure communication.
Key benefits of SecureCRT:
- Support for SSH, Telnet, and serial connections
- Session scripting for automation
- Customizable user interface
7. Cygwin
Cygwin is a Unix-like environment for Windows that includes an SSH client for managing IoT devices. It provides a command-line interface for executing remote commands and transferring files securely. Cygwin is particularly useful for users familiar with Unix-based systems and offers a wide range of tools for network management.
Features of Cygwin:
- Support for SSH and SFTP
- Command-line interface
- Extensive library of Unix utilities
8. SSH.NET
SSH.NET is a .NET library for implementing SSH functionality in IoT applications. It allows developers to integrate SSH capabilities into their custom solutions, enabling secure remote access to IoT devices. SSH.NET is particularly useful for building custom management tools and automation scripts.
Advantages of SSH.NET:
- Support for AES, RSA, and ECC encryption
- Easy integration with .NET applications
- Open-source and customizable
9. SSH Tectia
SSH Tectia is a commercial SSH solution designed for enterprise environments. It offers advanced security features, including strong encryption, public-key authentication, and centralized management. SSH Tectia is particularly useful for managing large-scale IoT deployments in industries such as healthcare, finance, and manufacturing.
Key features of SSH Tectia:
- Support for FIPS 140-2 compliant encryption
- Centralized key management
- Advanced logging and auditing capabilities
10. Dropbear SSH
Dropbear SSH is a lightweight SSH server and client designed for resource-constrained IoT devices. It is open-source, easy to configure, and offers robust encryption for secure communication. Dropbear SSH is particularly useful for embedded systems and small-scale IoT deployments.
Advantages of Dropbear SSH:
- Small memory footprint
- Support for SSH and SCP
- Easy to configure and deploy
Factors to Consider When Choosing a Remote IoT Device SSH Solution
Selecting the right SSH solution for your IoT devices depends on several factors. Here are some key considerations:
- Security: Ensure that the solution offers robust encryption and authentication mechanisms to protect your data.
- Compatibility: Choose a solution that is compatible with your IoT devices and operating systems.
- Scalability: Consider whether the solution can handle the number of devices you plan to manage.
- Ease of Use: Opt for a solution that is user-friendly and requires minimal configuration.
- Cost: Evaluate the cost of the solution and determine whether it fits within your budget.
Best Practices for Securing IoT Devices with SSH
While SSH provides robust security for IoT devices, it is essential to follow best practices to ensure maximum protection. Here are some tips:
- Use Strong Passwords: Avoid using weak or default passwords for SSH access.
- Enable Public-Key Authentication: Use public-key authentication instead of password-based authentication for added security.
- Disable Root Login: Prevent direct root access to reduce the risk of unauthorized access.
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activity.
- Keep Software Updated: Ensure that your SSH client and server software are up to date with the latest security patches.
Common Challenges in Remote IoT Device SSH Management
Managing IoT devices with SSH can present several challenges. Here are some common issues and solutions:
- Network Connectivity: Ensure that your IoT devices have stable internet connectivity to maintain SSH sessions.
- Firewall Restrictions: Configure firewalls to allow SSH traffic on the appropriate ports.
- Key Management: Implement a centralized key management system to simplify public-key authentication.
- Performance Issues: Optimize SSH configurations to reduce latency and improve performance.
Future Trends in Remote IoT Device SSH
The field of remote IoT device SSH is rapidly evolving, driven by advancements in technology and increasing demand for secure connectivity. Some emerging trends include:
- Quantum-Resistant Encryption: As quantum computing becomes more prevalent, SSH solutions will need to adopt quantum-resistant encryption algorithms.
- Artificial Intelligence: AI-powered SSH tools will enhance threat detection and response capabilities, improving overall security.
- Edge Computing: The integration of SSH with edge computing will enable faster and more secure communication between IoT devices.
Conclusion
In conclusion, the best remote IoT device SSH solutions offer robust security, scalability, and ease of use for managing connected devices. Whether you choose OpenSSH, PuTTY, or another solution, ensuring the security of your IoT ecosystem is critical in today's interconnected world. By following best practices and staying informed about emerging trends, you can protect your devices and data from cyber threats.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, please consider sharing it with your network. For more insights on IoT security and technology, explore our other articles on the website.
Table of Contents
- What is Remote IoT Device SSH?
- Top 10 Best Remote IoT Device SSH Solutions
- Factors to Consider When Choosing a Remote IoT Device SSH Solution
- Best Practices for Securing IoT Devices with SSH
- Common Challenges in Remote IoT Device SSH Management