In today's interconnected world, securely connect remote IoT P2P SSH Windows 10 has become a crucial requirement for both personal and business users. Whether you're managing smart home devices or monitoring industrial IoT systems, ensuring secure communication is paramount. This guide will provide a comprehensive overview of how to establish and maintain secure connections for IoT devices using SSH on Windows 10.
As the Internet of Things (IoT) continues to expand, the need for secure communication protocols becomes increasingly important. Remote connections, especially those involving peer-to-peer (P2P) setups, require robust security measures to protect sensitive data. Windows 10 provides a variety of tools and configurations to facilitate secure IoT connections using SSH.
This article will explore the technical aspects of setting up and maintaining secure IoT connections. From understanding the basics of SSH to advanced configurations, we'll cover everything you need to know to protect your IoT ecosystem effectively.
Read also:Is Charli Damelio Pregnant Unraveling The Truth Behind The Rumors
Table of Contents
- Introduction to SSH
- Why Secure Connections Are Critical
- Understanding Remote IoT Connections
- Setting Up SSH on Windows 10
- Configuring P2P SSH Connections
- Securing Your SSH Connection
- Troubleshooting Common Issues
- Best Practices for Secure IoT SSH
- Case Studies and Examples
- Conclusion and Next Steps
Introduction to SSH
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It is widely used for remote command-line operations and secure data transfer. SSH ensures confidentiality, integrity, and authentication of data exchanged between devices.
Key Features of SSH
- Encryption of data in transit
- Authentication mechanisms such as public key and password-based authentication
- Support for secure file transfer through SFTP (SSH File Transfer Protocol)
For those looking to securely connect remote IoT P2P SSH Windows 10, understanding these features is essential to leveraging the full potential of SSH.
Why Secure Connections Are Critical
In the realm of IoT, security cannot be overlooked. Devices connected to the internet are vulnerable to cyber threats such as unauthorized access, data breaches, and malware attacks. Securely connecting IoT devices ensures the protection of sensitive information and the integrity of the network.
Risks of Insecure Connections
- Data theft
- Device hijacking
- Network disruption
By implementing secure protocols like SSH, you can mitigate these risks and ensure the reliability of your IoT ecosystem.
Understanding Remote IoT Connections
How Remote IoT Connections Work
Remote IoT connections allow devices to communicate with each other regardless of their physical location. These connections are typically established using protocols such as SSH, which provide secure channels for data exchange.
Peer-to-Peer (P2P) Connections
P2P connections enable direct communication between devices without the need for a central server. This setup is particularly useful in scenarios where devices need to exchange data quickly and efficiently.
Read also:Camilla Arauacutejo Nudes Unveiling The Truth And Debunking Myths
When securely connect remote IoT P2P SSH Windows 10, the focus is on creating a direct, encrypted link between devices, ensuring that data remains private and secure.
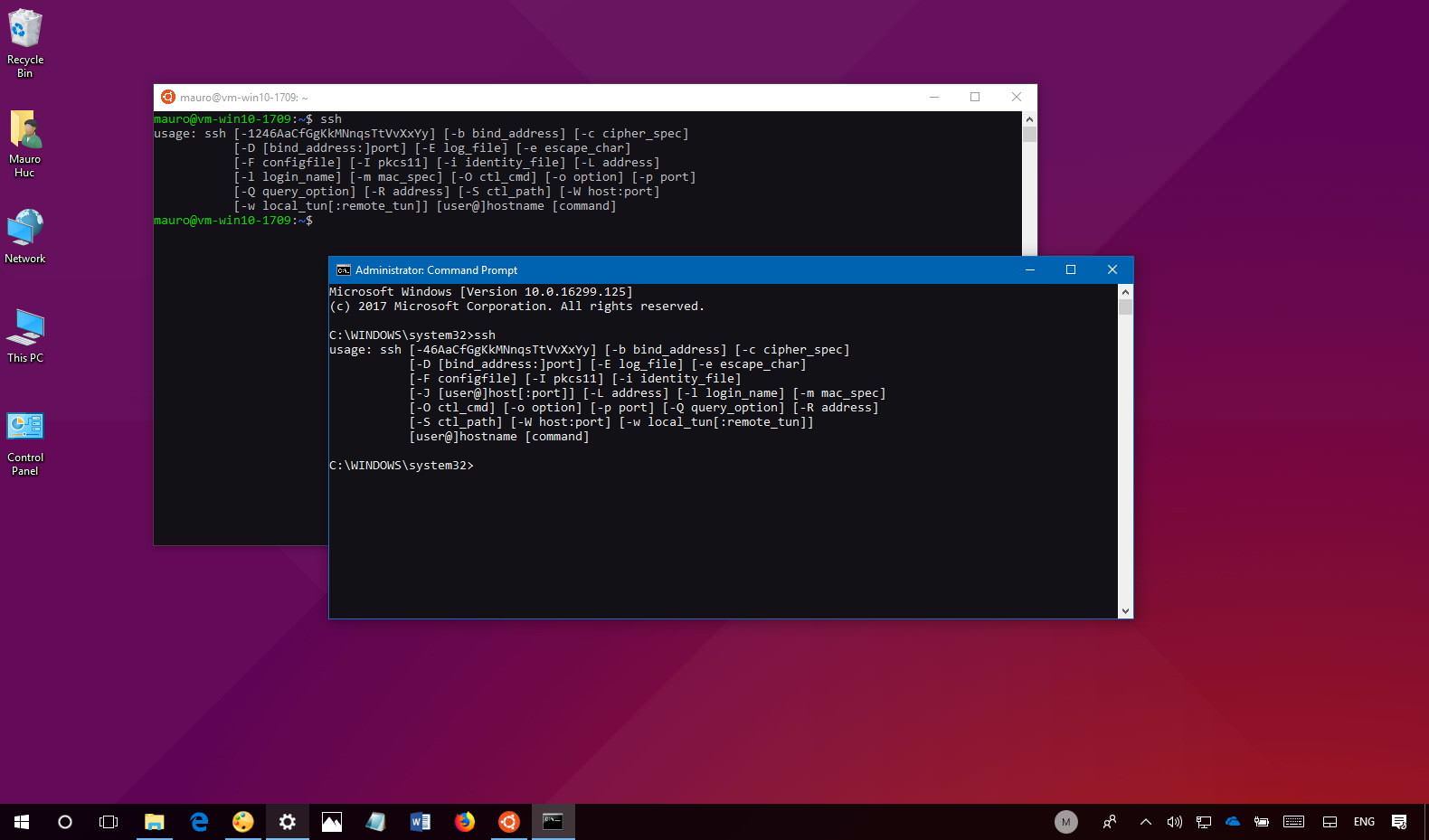
Setting Up SSH on Windows 10
Installing SSH Client and Server
Windows 10 includes built-in support for SSH through the OpenSSH client and server. To enable these features, follow these steps:
- Open the "Settings" app.
- Go to "Apps" and click on "Optional Features."
- Select "Add a feature" and search for "OpenSSH Client" and "OpenSSH Server."
- Install both features to enable SSH functionality on your system.
Configuring SSH Settings
After installation, you can configure SSH settings through the Windows Services Manager. This allows you to customize parameters such as port numbers and authentication methods.
Configuring P2P SSH Connections
Establishing a Direct Connection
To securely connect remote IoT P2P SSH Windows 10, you need to establish a direct connection between devices. This involves configuring SSH keys and setting up port forwarding if necessary.
Using SSH Keys for Authentication
SSH keys provide a secure and passwordless authentication method. To generate SSH keys on Windows 10:
- Open the Command Prompt or PowerShell.
- Run the command
ssh-keygento generate a key pair. - Copy the public key to the remote device using the
ssh-copy-idcommand.
Securing Your SSH Connection
Best Security Practices
To ensure the security of your SSH connections, consider the following practices:
- Use strong, unique passwords or SSH keys for authentication.
- Disable password-based authentication if possible.
- Limit access to specific IP addresses using firewall rules.
Regularly Updating Software
Keeping your SSH client and server software up to date is crucial for maintaining security. Regular updates ensure that vulnerabilities are patched promptly.
Troubleshooting Common Issues
Connection Problems
If you encounter issues while trying to securely connect remote IoT P2P SSH Windows 10, consider the following troubleshooting steps:
- Verify that the SSH service is running on the server.
- Check firewall settings to ensure that the SSH port is open.
- Test the connection using the
sshcommand with the correct credentials.
Error Messages
Common error messages such as "connection refused" or "authentication failed" can often be resolved by reviewing configuration files and ensuring proper key setup.
Best Practices for Secure IoT SSH
Regular Audits
Performing regular audits of your SSH configurations and access logs can help identify potential security threats. This proactive approach ensures that your IoT ecosystem remains secure.
Limiting Access
Restrict access to your SSH server by implementing strict access controls. Only authorized devices and users should be granted access to the network.
Case Studies and Examples
Real-World Applications
Companies across various industries are leveraging SSH to securely connect remote IoT P2P SSH Windows 10. For example, in the healthcare sector, hospitals use SSH to ensure the secure transmission of patient data between IoT devices.
Success Stories
Many organizations have reported significant improvements in network security after implementing SSH-based solutions. These success stories highlight the importance of adopting secure communication protocols in IoT environments.
Conclusion and Next Steps
In conclusion, securely connect remote IoT P2P SSH Windows 10 is essential for protecting your IoT ecosystem from potential threats. By following the guidelines and best practices outlined in this article, you can establish robust and secure connections for your devices.
We encourage you to take the following steps:
- Review your current SSH configurations and implement necessary updates.
- Explore additional resources and documentation to deepen your understanding of SSH and IoT security.
- Share your thoughts and experiences in the comments section below, and consider reading other articles on our site for further insights.
Thank you for reading, and we hope this guide has provided valuable information to enhance the security of your IoT connections.