As the Internet of Things (IoT) continues to expand, securely connecting remote IoT devices through peer-to-peer (P2P) SSH has become a critical concern for businesses and individuals alike. The rise in IoT adoption brings with it an increased risk of cyberattacks, particularly from hackers targeting vulnerabilities in network connections. In this article, we will explore how to establish secure remote connections for IoT devices using P2P SSH protocols while safeguarding against potential threats.
This topic is especially relevant as more organizations rely on IoT devices for operational efficiency. Ensuring the security of these connections is not just about protecting data; it's about maintaining trust and reliability in an increasingly interconnected world. By understanding the best practices for secure connections, you can mitigate risks and enhance your cybersecurity posture.
Throughout this article, we will delve into the technical aspects of securely connecting IoT devices, explore common vulnerabilities, and provide actionable strategies to protect your network from malicious actors. Whether you're a network administrator or an IT professional, this guide will equip you with the knowledge needed to fortify your IoT infrastructure.
Read also:5movierulz Telugu 2025 Your Ultimate Guide To Telugu Movies And Beyond
Table of Contents
- Introduction to Secure Remote IoT Connections
- Overview of IoT and Its Security Challenges
- Understanding P2P SSH for IoT
- Common Vulnerabilities in IoT Networks
- How to Securely Connect Remote IoT Devices
- Best Practices for IoT Security
- Understanding Hacker Threats in IoT
- Tools and Technologies for Enhanced Security
- Real-World Examples of IoT Security Breaches
- Conclusion and Call to Action
Introduction to Secure Remote IoT Connections
Connecting remote IoT devices securely is essential in today's digital landscape. With the proliferation of IoT devices, ensuring that data transmitted between devices is protected from unauthorized access is paramount. Peer-to-peer (P2P) SSH offers a robust solution for establishing secure connections, allowing devices to communicate directly without relying on centralized servers.
The importance of securely connecting remote IoT devices cannot be overstated. By implementing P2P SSH, organizations can significantly reduce the risk of data breaches and cyberattacks. This section will outline the fundamental principles of secure IoT connections and highlight why they are crucial for modern networks.
Overview of IoT and Its Security Challenges
What is IoT?
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. From smart home appliances to industrial machinery, IoT devices are transforming industries by providing real-time insights and automating processes.
However, the rapid growth of IoT has introduced new security challenges. Many IoT devices lack robust security features, making them vulnerable to attacks. As these devices often handle sensitive data, ensuring their security is vital for protecting both individuals and organizations.
Security Challenges in IoT
- Limited processing power and memory in IoT devices restrict the implementation of advanced security measures.
- Default passwords and inadequate firmware updates expose devices to unauthorized access.
- The decentralized nature of IoT networks complicates security management and monitoring.
Addressing these challenges requires a comprehensive approach that combines technology, policy, and best practices.
Read also:Hdhub4u Tv Your Ultimate Destination For Hindi Movie Downloads
Understanding P2P SSH for IoT
What is P2P SSH?
Peer-to-peer (P2P) SSH is a secure communication protocol that allows IoT devices to establish direct connections without the need for intermediaries. SSH, or Secure Shell, provides encryption and authentication mechanisms to protect data during transmission. By leveraging P2P SSH, organizations can enhance the security of their IoT networks.
P2P SSH offers several advantages over traditional client-server architectures, including reduced latency and improved resilience. These benefits make it an ideal choice for securing remote IoT connections.
How Does P2P SSH Work?
P2P SSH operates by creating a secure tunnel between two devices, ensuring that all data exchanged is encrypted and authenticated. The protocol uses public-key cryptography to verify the identity of devices and protect against man-in-the-middle attacks. By eliminating the need for centralized servers, P2P SSH reduces the attack surface and minimizes the risk of data breaches.
Common Vulnerabilities in IoT Networks
Weak Authentication
One of the most common vulnerabilities in IoT networks is weak authentication. Many devices come with default passwords that are rarely changed, making them easy targets for hackers. Strengthening authentication mechanisms is crucial for securing IoT devices.
Implementing multi-factor authentication (MFA) can significantly enhance security by requiring users to provide additional verification beyond just a password.
Inadequate Firmware Updates
Another prevalent issue is the lack of timely firmware updates. Manufacturers often fail to release security patches promptly, leaving devices exposed to known vulnerabilities. Regularly updating firmware ensures that devices are protected against the latest threats.
Organizations should establish a proactive approach to firmware management, prioritizing updates for critical devices.
How to Securely Connect Remote IoT Devices
Step-by-Step Guide
Securing remote IoT connections involves several key steps:
- Identify all devices on the network and assess their security posture.
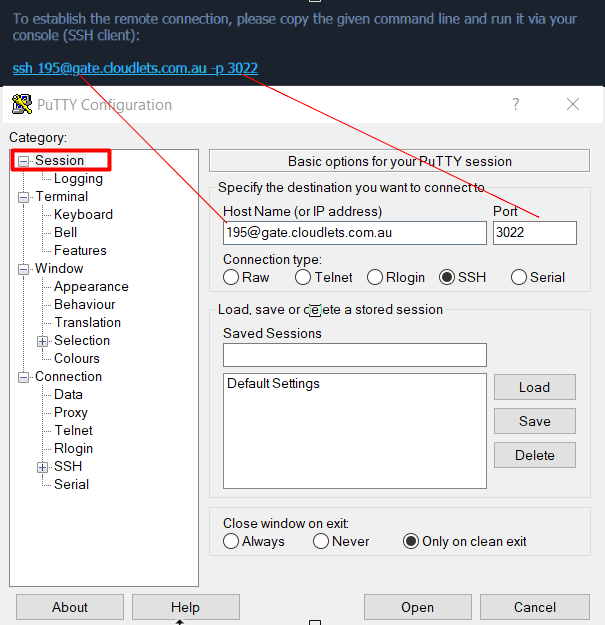
- Implement strong authentication mechanisms, such as P2P SSH or MFA.
- Encrypt data transmissions using robust encryption protocols.
- Regularly update firmware and software to address known vulnerabilities.
- Monitor network activity for suspicious behavior and respond promptly to potential threats.
By following these steps, organizations can establish secure connections for their IoT devices and reduce the risk of cyberattacks.
Best Practices for IoT Security
Network Segmentation
Segmenting IoT networks can help isolate sensitive devices and limit the potential impact of a security breach. By dividing the network into smaller, manageable segments, organizations can better control access and monitor activity.
Implementing network segmentation requires careful planning and configuration, but the benefits in terms of security and manageability are significant.
Regular Security Audits
Conducting regular security audits is essential for identifying vulnerabilities and ensuring compliance with best practices. These audits should include assessments of device configurations, network architecture, and security policies.
Engaging third-party experts to perform security audits can provide valuable insights and help organizations address blind spots in their security strategies.
Understanding Hacker Threats in IoT
Types of Hacker Attacks
Hackers employ various tactics to exploit vulnerabilities in IoT networks. Some common attack types include:
- Brute-force attacks: Attempting to guess passwords through automated trials.
- Man-in-the-middle attacks: Intercepting and altering communications between devices.
- Denial-of-service (DoS) attacks: Overloading devices with traffic to disrupt operations.
Understanding these threats is the first step in developing effective countermeasures.
Protecting Against Hackers
Protecting IoT networks from hackers requires a multi-layered approach that combines technology, policy, and education. Organizations should invest in advanced security solutions, establish clear policies for device management, and provide training for employees to recognize and respond to potential threats.
Tools and Technologies for Enhanced Security
Encryption Technologies
Encryption plays a vital role in securing IoT communications. Tools like P2P SSH and TLS (Transport Layer Security) provide robust encryption mechanisms that protect data during transmission. Implementing these technologies ensures that sensitive information remains confidential and inaccessible to unauthorized parties.
Organizations should evaluate their encryption needs and select tools that align with their security requirements.
Monitoring and Analytics
Monitoring tools and analytics platforms can help organizations detect and respond to security incidents in real time. By analyzing network activity and device behavior, these tools can identify anomalies that may indicate a potential breach.
Investing in advanced monitoring and analytics capabilities is essential for maintaining the security of IoT networks.
Real-World Examples of IoT Security Breaches
Case Study: Mirai Botnet
The Mirai botnet attack in 2016 highlighted the vulnerabilities of IoT devices. Hackers exploited weak passwords and unpatched firmware to compromise thousands of devices, creating a massive botnet that launched a distributed denial-of-service (DDoS) attack on major websites.
This incident underscored the importance of securing IoT devices and implementing robust security measures to prevent similar attacks in the future.
Conclusion and Call to Action
Securing remote IoT connections through P2P SSH is a critical component of modern cybersecurity strategies. By understanding the challenges and implementing best practices, organizations can protect their networks from hackers and ensure the integrity of their data.
We encourage readers to take action by assessing their IoT security posture, implementing P2P SSH for secure connections, and staying informed about the latest threats and technologies. Share your thoughts and experiences in the comments below, and explore other articles on our site for more insights into cybersecurity and IoT.