Connecting remote IoT devices through secure P2P SSH on Android has become an essential skill for tech enthusiasts, IT professionals, and developers alike. As the Internet of Things (IoT) continues to grow exponentially, ensuring secure communication between devices is paramount. This guide will walk you through everything you need to know about securely connecting remote IoT devices using P2P SSH on Android, including step-by-step instructions, essential tools, and best practices.
With billions of IoT devices connected globally, the importance of securing these devices cannot be overstated. Whether you're managing smart home devices, industrial sensors, or wearable tech, secure connectivity is key to protecting sensitive data. This article will provide actionable insights into setting up P2P SSH tunnels, downloading necessary apps, and ensuring your Android device remains secure.
As the demand for remote access grows, so does the need for secure protocols. Understanding how to securely connect remote IoT devices using P2P SSH on Android is not just a technical skill—it’s a necessity. Let’s dive into the details and equip you with the knowledge to safeguard your IoT ecosystem.
Read also:Kaylee Hartung Eye Injury A Comprehensive Analysis And Updates
Table of Contents
- Introduction to IoT and Its Importance
- Understanding SSH and Its Role in IoT Security
- P2P SSH Explained: What It Is and Why It Matters
- Top Android SSH Clients for Secure Connections
- Downloading and Installing SSH Apps on Android
- Configuring P2P SSH on Android: Step-by-Step Guide
- Securing Remote Connections: Best Practices
- Troubleshooting Common SSH Issues
- Real-World Applications of P2P SSH in IoT
- Conclusion and Next Steps
Introduction to IoT and Its Importance
The Internet of Things (IoT) refers to the network of interconnected devices that communicate and exchange data over the internet. From smart thermostats to industrial automation systems, IoT devices are transforming industries and enhancing our daily lives. However, with this convenience comes the challenge of securing these devices from cyber threats.
IoT security is a critical concern due to the vast amount of sensitive data being transmitted. A breach in one device can compromise an entire network, making secure connectivity a top priority. Understanding how to securely connect remote IoT devices is vital for protecting both personal and enterprise-level data.
As IoT adoption continues to rise, the demand for secure communication protocols like P2P SSH is increasing. This article will explore how to implement these protocols effectively on Android devices, ensuring your IoT ecosystem remains protected.
Understanding SSH and Its Role in IoT Security
Secure Shell (SSH) is a cryptographic network protocol used for secure communication over unsecured networks. It provides a secure channel for data transfer, remote command execution, and file management. In the context of IoT, SSH plays a crucial role in securing device-to-device communication.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between devices, ensuring confidentiality.
- Authentication: It verifies the identity of devices and users, preventing unauthorized access.
- Integrity: SSH ensures that data remains unaltered during transmission, maintaining its integrity.
By leveraging SSH, IoT devices can communicate securely, reducing the risk of data breaches and cyberattacks. This section will delve deeper into how SSH works and its importance in securing IoT networks.
Read also:Rei Kamiki Rising Star In The World Of Entertainment
P2P SSH Explained: What It Is and Why It Matters
Peer-to-Peer (P2P) SSH is a method of establishing direct, secure connections between devices without relying on a central server. This approach offers several advantages, including reduced latency, improved security, and enhanced scalability. In the realm of IoT, P2P SSH is particularly beneficial for remote device management and data exchange.
Benefits of P2P SSH
- Direct Connectivity: Devices can communicate directly, bypassing intermediaries.
- Enhanced Security: P2P SSH minimizes the risk of man-in-the-middle attacks.
- Cost-Effective: It eliminates the need for costly infrastructure, making it ideal for large-scale IoT deployments.
Understanding P2P SSH is essential for anyone looking to secure IoT devices. This section will provide a comprehensive overview of P2P SSH and its applications in IoT environments.
Top Android SSH Clients for Secure Connections
When it comes to securely connecting IoT devices on Android, having the right SSH client is crucial. Several reliable SSH clients are available on the Google Play Store, each offering unique features and functionalities. Below are some of the top SSH clients for Android:
Popular Android SSH Clients
- Termius: A powerful SSH client with a user-friendly interface and robust security features.
- ConnectBot: An open-source SSH client that supports multiple connections and custom keybindings.
- ServerAuditor: Offers advanced features like session recording and file transfer capabilities.
Choosing the right SSH client depends on your specific needs and preferences. This section will evaluate these clients and help you make an informed decision.
Downloading and Installing SSH Apps on Android
Downloading and installing SSH apps on Android is a straightforward process. Follow these steps to get started:
- Open the Google Play Store on your Android device.
- Search for your preferred SSH client (e.g., Termius, ConnectBot).
- Select the app and click "Install" to begin the download process.
- Once installed, launch the app and configure it according to your requirements.
It’s important to download apps from reputable sources to ensure security. This section will guide you through the process of downloading and installing SSH apps safely and efficiently.
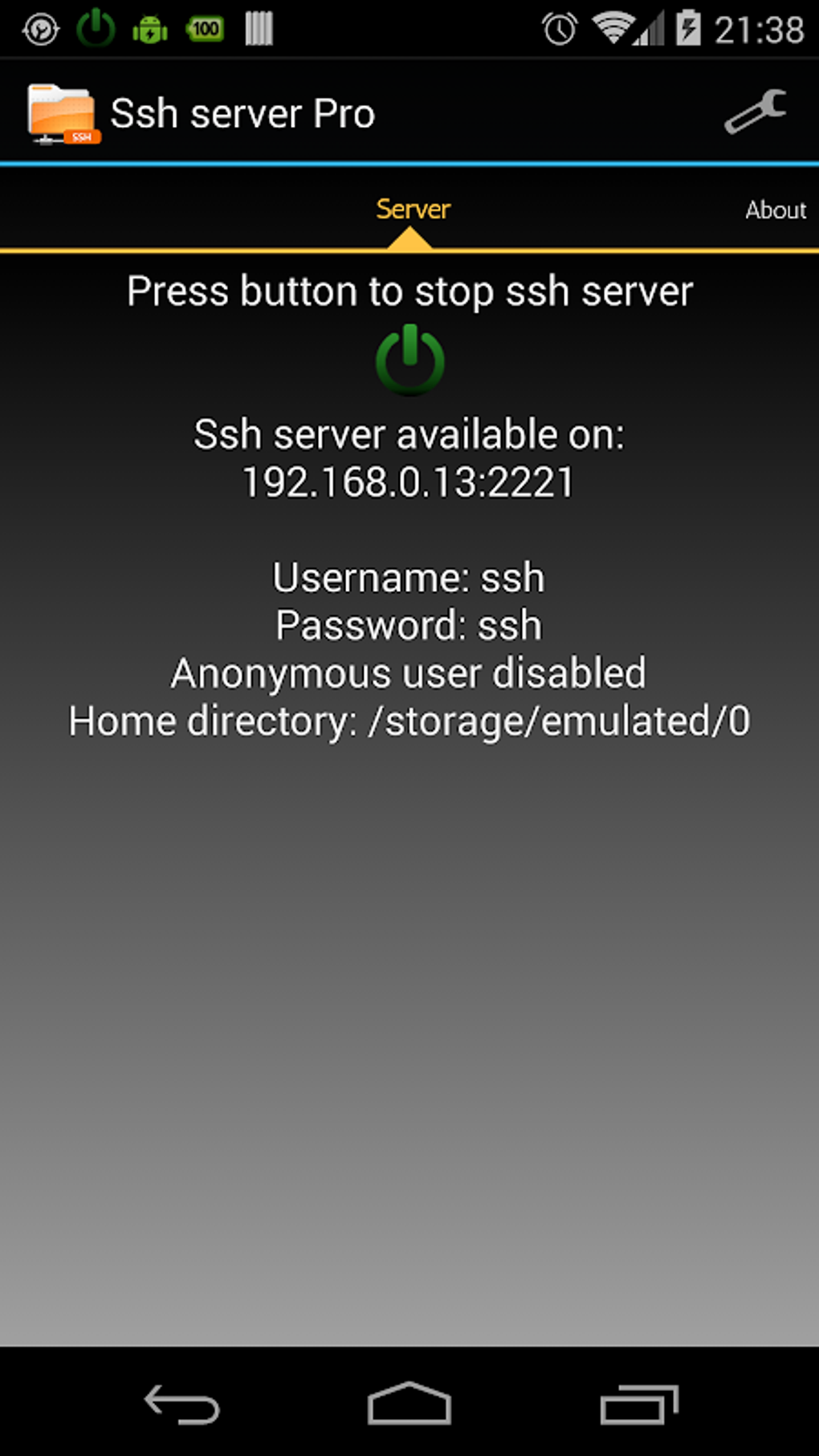
Configuring P2P SSH on Android: Step-by-Step Guide
Configuring P2P SSH on Android involves several steps, including setting up SSH keys, establishing connections, and testing the setup. Below is a step-by-step guide to help you configure P2P SSH:
Step 1: Generate SSH Keys
SSH keys are essential for secure authentication. Use your SSH client to generate a pair of public and private keys.
Step 2: Set Up Connections
Configure your SSH client to connect to remote IoT devices using the generated keys. Ensure that the devices are properly configured to accept SSH connections.
Step 3: Test the Connection
Once the setup is complete, test the connection to ensure secure communication between devices. This section will provide detailed instructions for each step, ensuring a smooth configuration process.
Securing Remote Connections: Best Practices
Securing remote connections is vital for protecting IoT devices from unauthorized access and cyber threats. Below are some best practices to enhance security:
- Use Strong Passwords: Avoid using default passwords and opt for complex, unique credentials.
- Enable Two-Factor Authentication (2FA): Add an extra layer of security by enabling 2FA for SSH connections.
- Regularly Update Software: Keep your SSH clients and IoT devices up to date with the latest security patches.
Implementing these practices will significantly enhance the security of your IoT ecosystem. This section will explore additional strategies for securing remote connections.
Troubleshooting Common SSH Issues
Despite best efforts, SSH connections may encounter issues. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH service is running on the remote device and that the correct port is being used.
- Authentication Failed: Verify that the SSH keys are correctly configured and that the credentials are accurate.
- Network Issues: Check your internet connection and ensure that there are no firewalls blocking the connection.
This section will provide troubleshooting tips and solutions to help you resolve common SSH issues effectively.
Real-World Applications of P2P SSH in IoT
P2P SSH has numerous real-world applications in IoT, ranging from smart homes to industrial automation. Below are some examples:
- Remote Device Management: IT professionals can securely manage IoT devices from anywhere using P2P SSH.
- Data Exchange: P2P SSH enables secure data transfer between IoT devices, ensuring confidentiality and integrity.
- Network Monitoring: Organizations can monitor IoT networks in real-time using P2P SSH for enhanced security.
Exploring these applications will provide valuable insights into the practical uses of P2P SSH in IoT environments.
Conclusion and Next Steps
Securing remote IoT devices using P2P SSH on Android is a critical aspect of IoT security. By following the steps outlined in this guide, you can ensure that your IoT ecosystem remains protected from cyber threats. Remember to implement best practices, regularly update your software, and stay informed about the latest security trends.
We encourage you to take action by downloading and installing an SSH client on your Android device, configuring P2P SSH, and testing the setup. Share your experience in the comments below and explore other articles on our site for more valuable insights into IoT security.
References:
- OpenSSH Documentation: https://www.openssh.com/
- Google Play Store: https://play.google.com/
- IoT Security Foundation: https://iotsecurityfoundation.org/