In the era of interconnected devices, the ability to securely connect remote IoT (Internet of Things) using peer-to-peer (P2P) technology has become a critical need for both hobbyists and professionals. Whether you're working on a home automation project or building an industrial IoT solution, understanding how to establish a secure connection without costly infrastructure is essential. This article will guide you through setting up a secure remote IoT P2P connection using a Raspberry Pi, ensuring your data remains protected and your devices remain accessible.
As more devices become part of the IoT ecosystem, the challenges of managing secure connections increase. Traditional methods often require complex setups or subscription-based services. However, leveraging the power of Raspberry Pi and open-source tools can provide a cost-effective and secure solution. This guide aims to demystify the process and empower you with actionable steps to achieve your goals.
From understanding the basics of IoT P2P connections to downloading the necessary software for your Raspberry Pi, this article will serve as your comprehensive resource. Whether you're a beginner or an advanced user, you'll find valuable insights to enhance your projects. Let's dive in!
Read also:Andrea Brillantes Unveiling The Truth Behind The Controversy
Table of Contents
- Introduction to IoT and Remote Connections
- Raspberry Pi: An Overview
- Benefits of Securely Connecting Remote IoT Devices
- Understanding P2P Technology
- Software Requirements for Raspberry Pi
- Step-by-Step Setup Process
- Implementing Security Measures
- Troubleshooting Common Issues
- Best Practices for Maintaining Secure Connections
- Conclusion and Next Steps
Introduction to IoT and Remote Connections
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. Remote IoT connections allow these devices to communicate across distances, making it possible to monitor and control them from anywhere in the world. However, ensuring these connections are secure is paramount to protecting sensitive data and maintaining device integrity.
Why Secure Connections Are Essential
Without proper security measures, IoT devices can be vulnerable to cyber threats such as hacking, data breaches, and unauthorized access. A secure connection ensures that only authorized users can interact with your devices, safeguarding both your personal and professional information.
Role of P2P in IoT
Peer-to-peer (P2P) technology eliminates the need for centralized servers, allowing devices to communicate directly. This reduces latency and dependency on third-party services, making it an ideal solution for remote IoT applications.
Raspberry Pi: An Overview
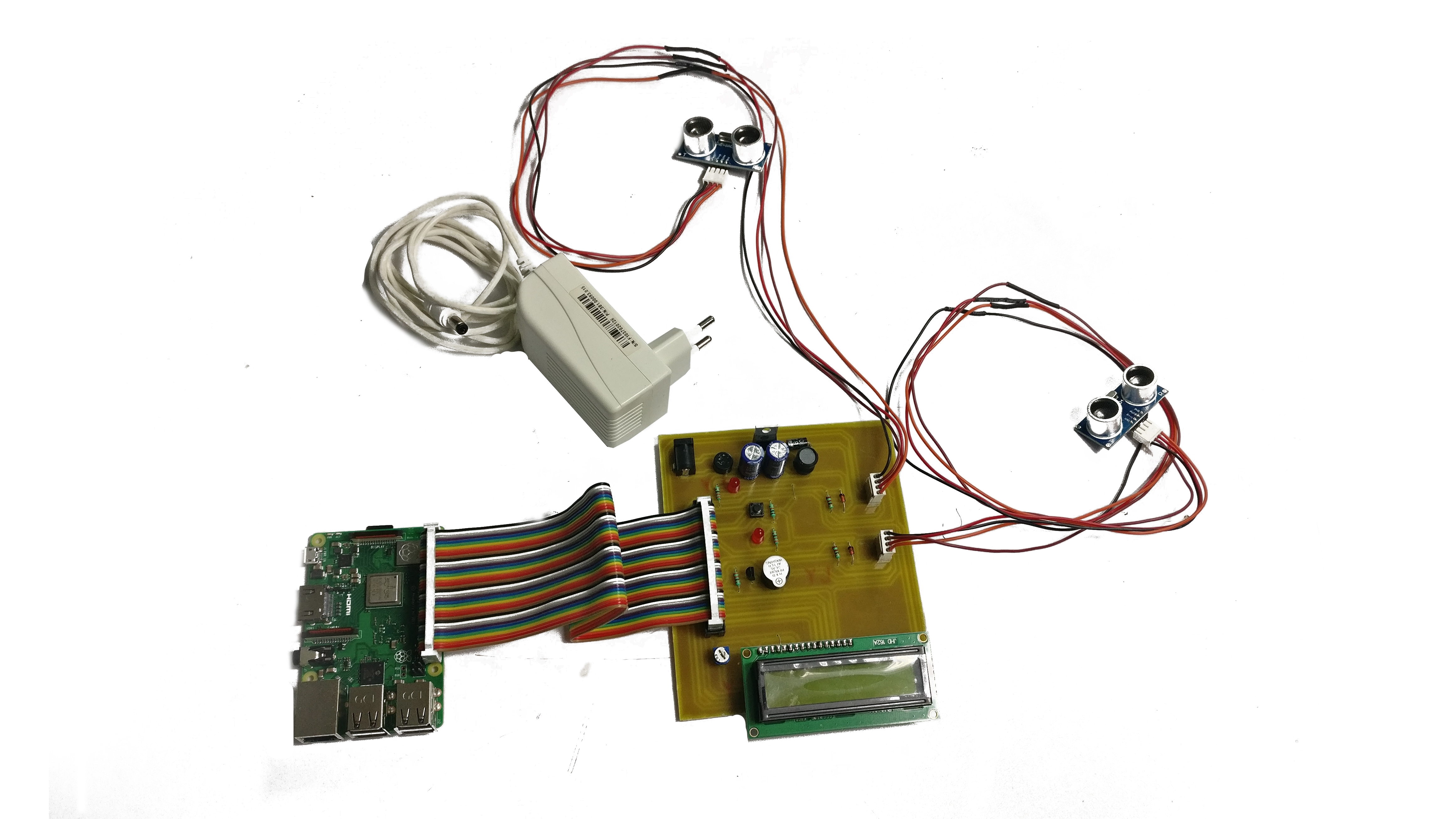
Raspberry Pi is a compact, affordable single-board computer widely used in educational and DIY projects. Its versatility and open-source nature make it an excellent choice for setting up secure remote IoT connections.
Read also:Bolly4u Org Your Ultimate Destination For Bollywood Entertainment
Key Features of Raspberry Pi
- Compact and lightweight design
- Support for various operating systems
- Rich community and extensive documentation
- Compatibility with numerous sensors and peripherals
Raspberry Pi's affordability and ease of use make it accessible to users of all skill levels, from beginners to advanced developers.
Benefits of Securely Connecting Remote IoT Devices
Establishing a secure connection for remote IoT devices offers several advantages:
- Data Protection: Ensures sensitive information remains confidential.
- Reliability: Minimizes the risk of unauthorized access or data loss.
- Scalability: Allows seamless expansion of your IoT network.
- Cost-Effectiveness: Reduces the need for expensive infrastructure.
By prioritizing security, you can build robust IoT solutions that meet the demands of modern applications.
Understanding P2P Technology
P2P technology enables devices to communicate directly without relying on centralized servers. This decentralized approach offers several benefits, including reduced latency and improved efficiency.
How P2P Works
In a P2P network, devices act as both clients and servers, sharing resources and data directly. This eliminates bottlenecks associated with traditional client-server architectures, making it ideal for remote IoT applications.
Advantages of P2P for IoT
- Enhanced security through direct connections
- Improved performance with reduced latency
- Lower costs due to minimal infrastructure requirements
Understanding P2P technology is crucial for leveraging its full potential in IoT projects.
Software Requirements for Raspberry Pi
To set up a secure remote IoT P2P connection using Raspberry Pi, you'll need the following software:
- Raspbian OS (or any compatible operating system)
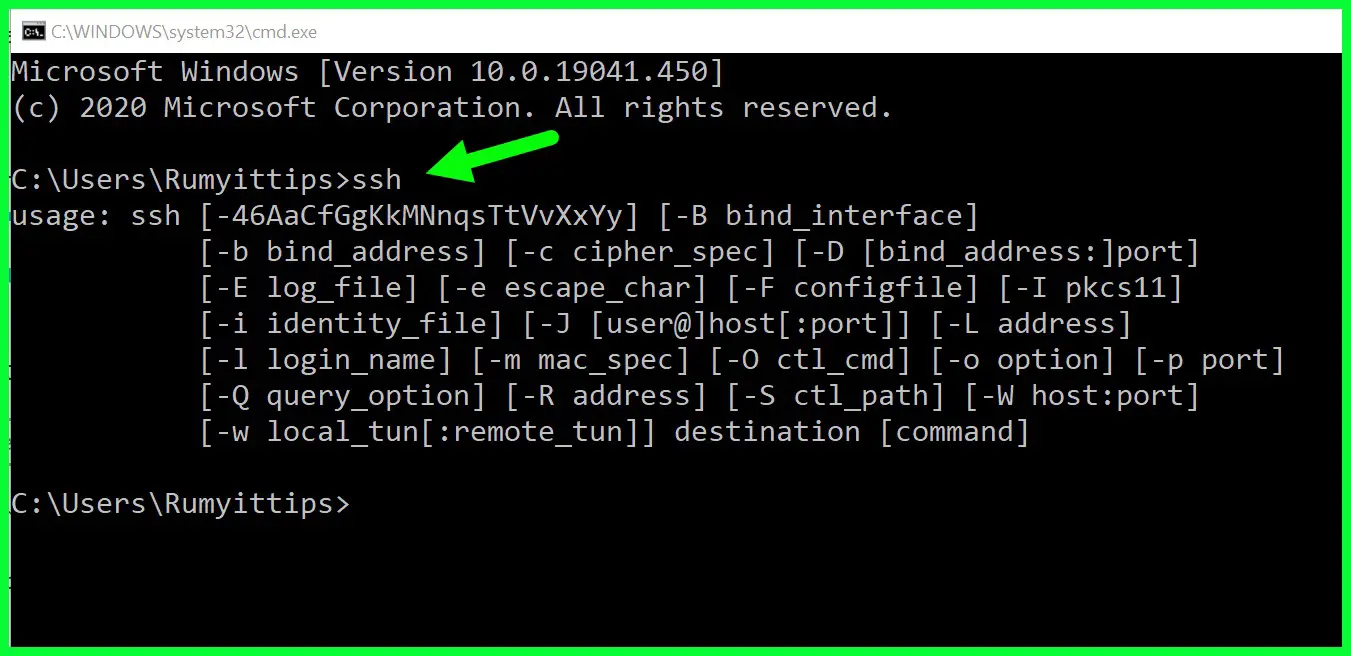
- SSH (Secure Shell) for remote access
- OpenVPN or similar software for secure communication
- Python or Node.js for scripting and automation
Ensure all software is up to date to take advantage of the latest features and security patches.
Step-by-Step Setup Process
Follow these steps to securely connect your remote IoT devices using Raspberry Pi:
Step 1: Install Raspbian OS
Download the latest version of Raspbian OS from the official website and install it on your Raspberry Pi. Follow the installation instructions carefully to ensure a smooth setup.
Step 2: Enable SSH
SSH allows you to access your Raspberry Pi remotely. Enable SSH by navigating to the Raspberry Pi configuration settings and selecting the SSH option.
Step 3: Configure OpenVPN
Install and configure OpenVPN to establish a secure connection between your devices. This step ensures that all communication is encrypted and protected from potential threats.
Step 4: Test the Connection
Once the setup is complete, test the connection to ensure everything is functioning as expected. Use tools like ping or traceroute to verify connectivity and identify any issues.
Implementing Security Measures
Securing your remote IoT connections requires a multi-layered approach:
- Use Strong Passwords: Ensure all devices and accounts use complex, unique passwords.
- Enable Two-Factor Authentication: Add an extra layer of security by requiring a second form of verification.
- Regularly Update Software: Keep all software up to date to protect against vulnerabilities.
- Monitor Activity: Regularly review logs and activity reports to detect any suspicious behavior.
By implementing these measures, you can significantly enhance the security of your IoT network.
Troubleshooting Common Issues
Encountering issues during setup is common. Here are some solutions to common problems:
- Connection Issues: Check network settings and ensure all devices are connected to the same network.
- SSH Not Working: Verify that SSH is enabled and the correct port is being used.
- OpenVPN Errors: Review configuration files and ensure all settings are correct.
If problems persist, consult the official documentation or seek assistance from the Raspberry Pi community.
Best Practices for Maintaining Secure Connections
To maintain secure remote IoT connections, adhere to the following best practices:
- Regularly review and update security protocols.
- Limit access to authorized users only.
- Perform routine maintenance and backups.
- Stay informed about the latest security trends and threats.
By following these practices, you can ensure the longevity and reliability of your IoT network.
Conclusion and Next Steps
Securing remote IoT connections using Raspberry Pi is a powerful way to protect your devices and data. By leveraging P2P technology and implementing robust security measures, you can create a reliable and scalable IoT solution. Remember to regularly update your systems and stay informed about the latest developments in the field.
We invite you to share your thoughts and experiences in the comments section below. Feel free to ask questions or suggest topics for future articles. Together, we can build a safer and more connected world. Don't forget to explore our other resources and guides to further enhance your knowledge and skills.
Sources: