In the era of rapid technological advancement, securely connecting remote IoT P2P downloads on Mac has become an essential skill for tech enthusiasts and professionals alike. As the Internet of Things (IoT) continues to grow, so does the need for secure communication between devices. This article will explore the most effective methods to ensure your IoT P2P connections are secure on a Mac device. Whether you're a beginner or an experienced user, this guide will provide valuable insights to enhance your cybersecurity knowledge.
Connecting IoT devices securely is no longer optional; it's a necessity. With the increasing number of cyber threats targeting IoT devices, understanding how to protect your data and devices is crucial. This article will delve into the importance of secure connections, the risks associated with unsecured IoT P2P downloads, and practical steps to safeguard your Mac.
Our focus will be on providing actionable advice and technical insights to help you create a secure environment for your IoT P2P downloads. By the end of this guide, you'll have the knowledge and tools necessary to protect your devices and maintain privacy in an increasingly connected world.
Read also:Hdhub4u Tv Your Ultimate Destination For Hindi Movie Downloads
Table of Contents
- Importance of Secure Connections for IoT Devices
- Risks Associated with Unsecured IoT P2P Connections
- How to Securely Connect Remote IoT Devices
- Mac-Specific Security Measures for IoT Connections
- Understanding P2P Protocols and Their Role in Security
- Tools and Software for Secure IoT P2P Connections
- Encryption Methods for IoT P2P Downloads
- Firewall and Security Settings on Mac
- Best Practices for Securing IoT P2P Connections
- The Future of IoT Security
Importance of Secure Connections for IoT Devices
In today's interconnected world, IoT devices play a pivotal role in enhancing productivity and convenience. However, the importance of secure connections for IoT devices cannot be overstated. Securely connect remote IoT P2P download Mac environments are essential to protect sensitive data and prevent unauthorized access. Without proper security measures, IoT devices can become vulnerable to cyberattacks, leading to data breaches and financial losses.
Securing IoT connections involves implementing robust encryption protocols, regularly updating firmware, and using secure authentication methods. These measures ensure that data transmitted between devices remains confidential and tamper-proof. By prioritizing security, organizations and individuals can enjoy the benefits of IoT technology without compromising their privacy.
Impact of Insecure Connections
- Data breaches leading to exposure of personal information
- Unauthorized access to critical systems
- Increased risk of malware and ransomware attacks
Risks Associated with Unsecured IoT P2P Connections
Unsecured IoT P2P connections pose significant risks to both individuals and organizations. When devices are connected without proper security measures, they become easy targets for hackers. These vulnerabilities can lead to various cybersecurity threats, including data theft, network infiltration, and even physical harm in some cases.
One of the primary risks is the potential for malicious actors to intercept data transmitted between devices. This can result in sensitive information being exposed, leading to financial losses and reputational damage. Additionally, unsecured IoT devices can be used as entry points for larger-scale attacks on corporate networks, making it crucial to implement robust security protocols.
Common Threats
- Man-in-the-middle (MITM) attacks
- Denial of Service (DoS) attacks
- Device hijacking and unauthorized control
How to Securely Connect Remote IoT Devices
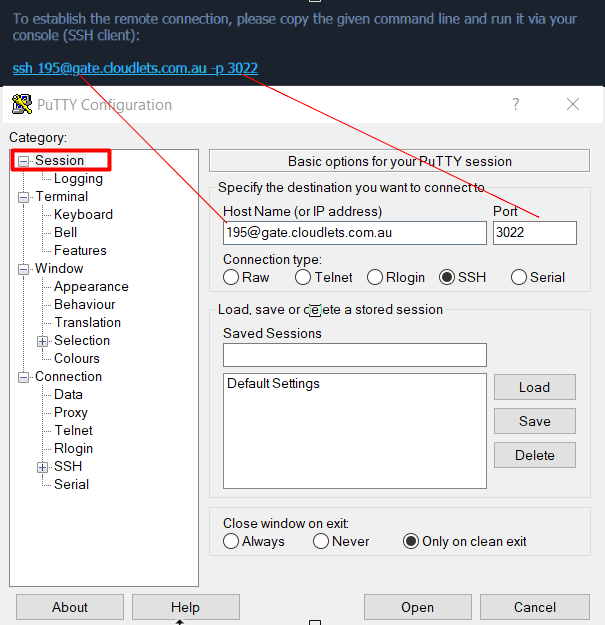
Securing remote IoT devices requires a multi-faceted approach that combines hardware, software, and network security measures. To securely connect remote IoT P2P downloads on a Mac, users should focus on implementing strong authentication methods, encrypting data transmissions, and regularly updating software.
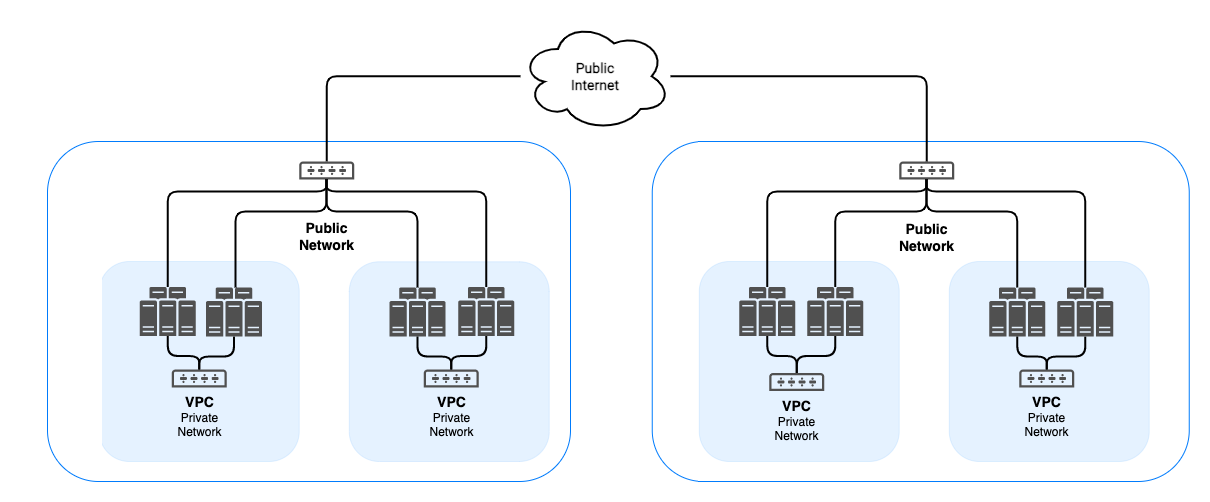
One effective method is to use Virtual Private Networks (VPNs) to create a secure tunnel for data transmission. Additionally, employing secure communication protocols such as HTTPS and TLS ensures that data remains encrypted during transit. By following these best practices, users can significantly reduce the risk of cyberattacks and protect their IoT devices.
Read also:How Tall Is Dorit Kemsley Discover The Real Facts About This Reality Star
Steps to Secure IoT Connections
- Implement strong passwords and two-factor authentication
- Use encryption protocols for data transmission
- Regularly update firmware and software
Mac-Specific Security Measures for IoT Connections
Mac users have access to several built-in security features that can enhance the security of IoT connections. macOS provides robust firewall settings, encryption options, and privacy controls that can be leveraged to protect IoT devices. By configuring these settings correctly, users can create a secure environment for their IoT P2P downloads.
Additionally, Mac users can utilize third-party security tools to complement the built-in features. These tools offer advanced threat detection, intrusion prevention, and real-time monitoring capabilities, ensuring that IoT devices remain secure at all times.
Key Security Features in macOS
- Firewall settings for network protection
- FileVault for full-disk encryption
- Gatekeeper for app security
Understanding P2P Protocols and Their Role in Security
P2P (Peer-to-Peer) protocols play a crucial role in enabling direct communication between IoT devices. These protocols allow devices to share data without relying on centralized servers, reducing latency and improving efficiency. However, the security of P2P connections depends on the protocols used and how they are implemented.
Securely connect remote IoT P2P download Mac environments require the use of secure protocols such as DHT (Distributed Hash Table) and uTP (Micro Transport Protocol). These protocols ensure that data is transmitted securely and efficiently, minimizing the risk of interception or tampering. Understanding the strengths and limitations of different P2P protocols is essential for maintaining secure IoT connections.
Popular P2P Protocols
- BitTorrent for file sharing
- libp2p for decentralized applications
- DHT for distributed data storage
Tools and Software for Secure IoT P2P Connections
Several tools and software solutions are available to enhance the security of IoT P2P connections. These tools provide features such as encryption, threat detection, and network monitoring, ensuring that devices remain protected from cyber threats. By leveraging these tools, users can create a secure environment for their IoT devices.
Some popular tools include NordVPN for secure data transmission, OpenVPN for custom configurations, and Wireshark for network analysis. These tools can be used in conjunction with macOS features to create a comprehensive security solution for IoT P2P connections.
Recommended Tools
- NordVPN for secure tunneling
- OpenVPN for advanced configurations
- Wireshark for network monitoring
Encryption Methods for IoT P2P Downloads
Encryption is a critical component of securing IoT P2P downloads. By encrypting data transmissions, users can ensure that sensitive information remains confidential and tamper-proof. There are several encryption methods available, each with its own strengths and limitations.
Some of the most commonly used encryption methods for IoT P2P downloads include AES (Advanced Encryption Standard), RSA (Rivest-Shamir-Adleman), and ECC (Elliptic Curve Cryptography). These methods provide varying levels of security and performance, making it important to choose the right one based on specific requirements.
Comparison of Encryption Methods
- AES for symmetric encryption
- RSA for asymmetric encryption
- ECC for efficient encryption
Firewall and Security Settings on Mac
Mac users can enhance the security of IoT P2P connections by configuring firewall and security settings. macOS provides robust firewall capabilities that can be customized to meet specific security needs. By enabling the firewall and configuring it to block incoming connections, users can protect their devices from unauthorized access.
Additionally, macOS offers privacy controls that allow users to manage app permissions and restrict access to sensitive data. By combining these settings with secure authentication methods and encryption protocols, users can create a secure environment for their IoT devices.
Configuring Firewall Settings
- Enable firewall in System Preferences
- Block incoming connections
- Allow specific apps through the firewall
Best Practices for Securing IoT P2P Connections
To ensure the security of IoT P2P connections, users should follow best practices that encompass hardware, software, and network security. These practices include implementing strong authentication methods, regularly updating firmware, and using encryption protocols. By adhering to these guidelines, users can create a secure environment for their IoT devices.
Additionally, users should stay informed about the latest cybersecurity threats and trends, enabling them to adapt their security measures accordingly. Regularly reviewing security settings and conducting vulnerability assessments can help identify potential weaknesses and address them proactively.
Key Best Practices
- Use strong passwords and two-factor authentication
- Regularly update firmware and software
- Monitor network activity for suspicious behavior
The Future of IoT Security
The future of IoT security lies in the development of advanced technologies and protocols that can address emerging threats. As IoT devices become more prevalent, the need for robust security measures will continue to grow. Innovations such as blockchain, AI-driven threat detection, and quantum encryption are expected to play a significant role in enhancing IoT security.
By staying ahead of the curve and adopting cutting-edge technologies, users and organizations can ensure the security of their IoT devices. The focus will shift towards creating seamless and secure ecosystems that prioritize user privacy and data protection.
Emerging Technologies
- Blockchain for secure data storage
- AI for threat detection
- Quantum encryption for advanced security
Kesimpulan
Securing IoT P2P connections on a Mac requires a comprehensive approach that combines hardware, software, and network security measures. By implementing strong authentication methods, using encryption protocols, and regularly updating software, users can create a secure environment for their IoT devices. This guide has provided actionable advice and technical insights to help you enhance your cybersecurity knowledge and protect your devices.
We encourage you to take the next step by reviewing your security settings, updating your firmware, and exploring the tools and software mentioned in this article. Your feedback is valuable, so please leave a comment or share this article with others who may find it helpful. Together, we can build a safer and more secure IoT ecosystem.