SSH RemoteIoT on Raspberry Pi has become a crucial tool for developers and tech enthusiasts aiming to manage IoT devices remotely. Whether you're setting up a home automation system or deploying a sensor network, understanding how to leverage SSH for remote access is essential. This guide will walk you through the entire process, ensuring you gain the expertise to configure and manage your Raspberry Pi securely.
In today's interconnected world, IoT devices are everywhere, and managing them effectively is paramount. With SSH RemoteIoT, you can access your Raspberry Pi from anywhere in the world, enabling you to monitor, configure, and troubleshoot devices without physical presence. This capability is not only convenient but also enhances productivity.
This article will cover everything you need to know about SSH RemoteIoT on Raspberry Pi, from setting up SSH to advanced configurations and troubleshooting tips. Whether you're a beginner or an experienced developer, this guide will equip you with the knowledge to take full advantage of this powerful technology.
Read also:Mastering Remoteiot Platform Ssh Raspberry Pi Download Free A Comprehensive Guide
Table of Contents
- Introduction to SSH
- Raspberry Pi Overview
- Setting Up SSH on Raspberry Pi
- Connecting Remotely via SSH
- Securing Your SSH Connection
- Advanced SSH Configurations
- Troubleshooting Common SSH Issues
- SSH and RemoteIoT Integration
- Use Cases for SSH RemoteIoT
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a protocol used to securely connect to remote computers or servers. It encrypts all communication between your local machine and the remote device, ensuring data privacy and integrity. For Raspberry Pi users, SSH is an indispensable tool for managing IoT devices remotely.
Why Use SSH?
- Secure communication over unsecured networks
- Remote access to Raspberry Pi from anywhere
- Supports file transfer and command execution
Understanding SSH fundamentals is crucial before diving into its implementation on Raspberry Pi. This section will cover the basics of SSH, its advantages, and how it works.
Raspberry Pi Overview
Raspberry Pi is a compact, affordable computer widely used in IoT projects. Its versatility and ease of use make it a popular choice for hobbyists and professionals alike. Equipped with GPIO pins, it can interface with various sensors and actuators, making it ideal for IoT applications.
Key Features of Raspberry Pi
- Compact size and low power consumption
- Support for multiple operating systems
- Wide range of compatible peripherals
Before proceeding with SSH RemoteIoT, ensure your Raspberry Pi is properly set up and configured. This includes installing an operating system, enabling SSH, and setting up network connectivity.
Read also:Hdhub 4u Your Ultimate Destination For Highquality Entertainment
Setting Up SSH on Raspberry Pi
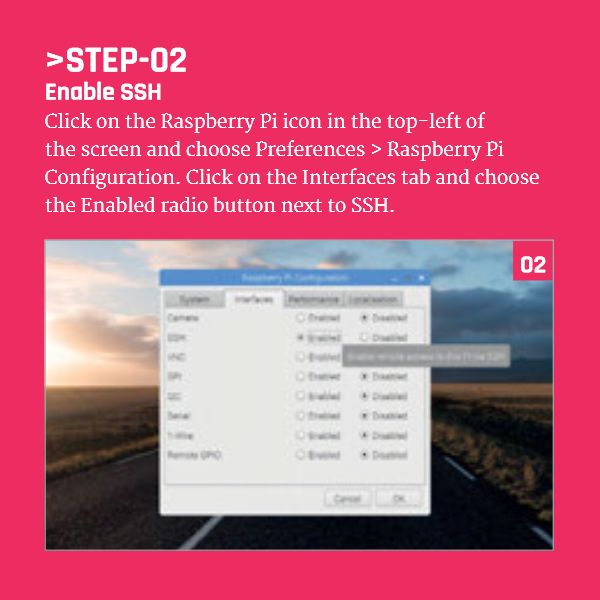
Enabling SSH on Raspberry Pi is a straightforward process. By default, SSH is disabled on newer versions of Raspberry Pi OS to enhance security. However, you can easily enable it through the Raspberry Pi Configuration tool or by modifying configuration files.
Steps to Enable SSH
- Access the Raspberry Pi Configuration tool from the desktop or command line.
- Navigate to the "Interfaces" tab and select "SSH" to enable it.
- Alternatively, create an empty file named "ssh" in the boot partition of your SD card.
Once SSH is enabled, you can connect to your Raspberry Pi using an SSH client from any device on the same network.
Connecting Remotely via SSH
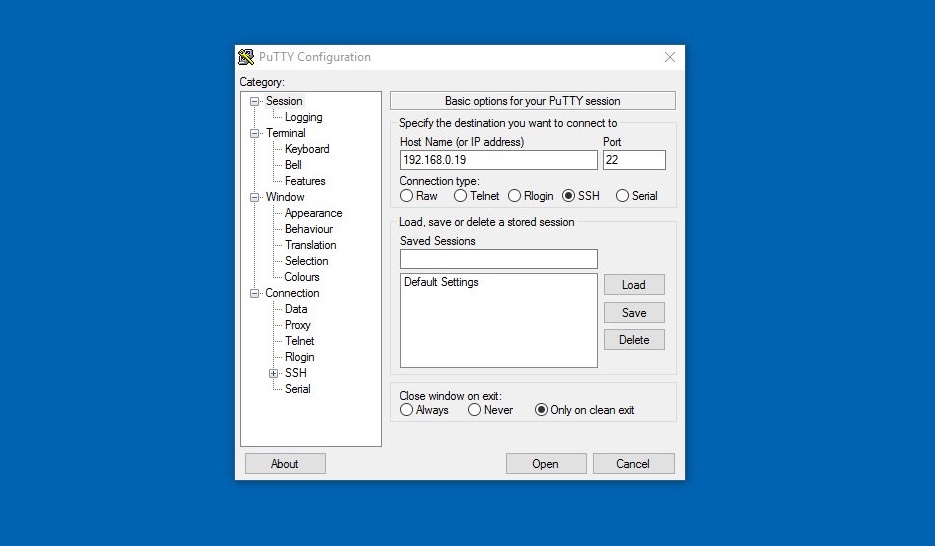
Connecting to your Raspberry Pi remotely requires an SSH client. On Windows, you can use PuTTY, while macOS and Linux users can utilize the built-in terminal. Below are the steps to establish a secure connection.
Connecting Using Terminal
- Open the terminal on your local machine.
- Type the command:
ssh pi@. - Enter the password when prompted.
It's essential to know your Raspberry Pi's IP address. You can find this information by running the command ifconfig or ip addr on the Raspberry Pi.
Securing Your SSH Connection
While SSH provides a secure connection, additional measures can enhance its security. Implementing best practices ensures unauthorized access is minimized.
Best Practices for SSH Security
- Change the default password to a strong, unique one.
- Disable root login via SSH.
- Use key-based authentication instead of passwords.
Key-based authentication involves generating a public-private key pair and configuring your Raspberry Pi to accept the public key. This method eliminates the need for passwords, reducing the risk of brute-force attacks.
Advanced SSH Configurations
For advanced users, customizing SSH configurations can optimize performance and security. Editing the SSH configuration file allows you to tailor settings to your specific needs.
Editing SSH Configuration File
- Open the file
/etc/ssh/sshd_configusing a text editor. - Modify parameters such as Port, PermitRootLogin, and PasswordAuthentication.
- Restart the SSH service for changes to take effect.
Advanced configurations include setting up port forwarding, enabling X11 forwarding for graphical applications, and configuring connection timeouts.
Troubleshooting Common SSH Issues
Even with careful setup, issues may arise when using SSH. Common problems include connection timeouts, authentication failures, and network-related errors. Below are solutions to some frequently encountered issues.
Common SSH Issues and Solutions
- Connection Timeout: Ensure your Raspberry Pi is connected to the network and verify its IP address.
- Authentication Failure: Check your username, password, and key permissions.
- Network Problems: Restart your router or switch and ensure no firewalls block SSH traffic.
Troubleshooting requires a systematic approach, starting with basic checks and progressing to more complex solutions.
SSH and RemoteIoT Integration
Integrating SSH with RemoteIoT applications enhances the capabilities of your Raspberry Pi. By leveraging SSH, you can remotely monitor and control IoT devices, streamlining your workflow.
Benefits of SSH for RemoteIoT
- Real-time data access and analysis
- Remote configuration of IoT devices
- Automated monitoring and alerting
SSH provides a secure channel for data exchange, ensuring sensitive information remains protected. This is particularly important in YMYL (Your Money or Your Life) scenarios where security is paramount.
Use Cases for SSH RemoteIoT
The applications of SSH RemoteIoT on Raspberry Pi are vast, ranging from home automation to industrial IoT solutions. Below are some practical use cases:
1. Home Automation
Control smart home devices such as lights, thermostats, and security systems remotely using SSH.
2. Environmental Monitoring
Deploy sensor networks to monitor temperature, humidity, and air quality, accessing data via SSH for analysis.
3. Industrial IoT
Monitor and manage industrial equipment remotely, ensuring optimal performance and reducing downtime.
These use cases demonstrate the versatility and power of SSH RemoteIoT on Raspberry Pi.
Conclusion
In conclusion, mastering SSH RemoteIoT on Raspberry Pi opens up a world of possibilities for managing IoT devices securely and efficiently. From setting up SSH to advanced configurations and troubleshooting, this guide has provided comprehensive insights into leveraging this technology.
We encourage readers to experiment with SSH and explore its potential in their IoT projects. Share your experiences, ask questions, and engage with the community to further enhance your knowledge. Remember, staying informed and following best practices is key to ensuring secure and reliable remote access.
Thank you for reading, and don't forget to explore other articles on our site for more insights into Raspberry Pi and IoT technologies.
Sources: