In today's digital era, remote IoT web SSH has become an essential tool for managing devices and networks securely from anywhere in the world. Whether you're a network administrator, IT professional, or hobbyist, understanding how to leverage SSH for remote IoT device management can significantly enhance your operational efficiency and security.
As more devices become connected through the Internet of Things (IoT), the need for secure remote access solutions has grown exponentially. RemoteIoT web SSH provides a robust framework for controlling and monitoring IoT devices, ensuring data integrity and system reliability.
This comprehensive guide will delve into the intricacies of remote IoT web SSH, exploring its applications, best practices, security considerations, and troubleshooting tips. By the end of this article, you'll have a solid understanding of how to implement and manage secure remote connections for IoT devices.
Read also:Kim Howard Unveiling The Life Achievements And Legacy Of A Remarkable Individual
Table of Contents
- Introduction to RemoteIoT Web SSH
- What is SSH and Why is it Important?
- Understanding IoT and Its Challenges
- Benefits of RemoteIoT Web SSH
- Setting Up RemoteIoT Web SSH
- Security Considerations for RemoteIoT Web SSH
- Best Practices for Managing RemoteIoT Web SSH
- Common Issues and Troubleshooting Tips
- Future Trends in RemoteIoT Web SSH
- Conclusion
Introduction to RemoteIoT Web SSH
RemoteIoT web SSH refers to the use of the Secure Shell (SSH) protocol to remotely access and manage Internet of Things (IoT) devices over the web. This technology enables users to securely connect to IoT devices from any location, provided they have an internet connection and the necessary credentials.
One of the key advantages of remote IoT web SSH is its ability to provide encrypted communication between the user and the target device. This ensures that sensitive data remains protected from unauthorized access and potential cyber threats. Additionally, SSH offers a wide range of features, such as file transfer, command execution, and session management, making it an indispensable tool for IoT device management.
What is SSH and Why is it Important?
Definition and Core Features
Secure Shell (SSH) is a cryptographic network protocol designed to facilitate secure communication over unsecured networks. It provides a secure channel for data transmission by encrypting all information exchanged between the client and server. Some of the core features of SSH include:
- Encryption: Ensures data confidentiality during transmission.
- Authentication: Verifies the identity of both the client and server.
- Integrity: Protects data from tampering during transmission.
Importance in IoT
In the context of IoT, SSH plays a crucial role in securing device communications and preventing unauthorized access. Given the increasing number of connected devices, ensuring robust security measures is paramount. SSH helps address these concerns by providing a secure and reliable method for remote device management.
Understanding IoT and Its Challenges
What is IoT?
The Internet of Things (IoT) refers to the network of physical devices, vehicles, home appliances, and other items embedded with sensors, software, and connectivity, enabling them to collect and exchange data. IoT devices range from simple sensors to complex industrial machinery, all interconnected through the internet.
Challenges in IoT Security
While IoT offers numerous benefits, it also presents significant security challenges. Some of the common issues include:
Read also:Kim Kardashian Siblings The Complete Guide To Their Lives Careers And Influence
- Limited Resources: Many IoT devices have limited processing power and memory, making it difficult to implement robust security measures.
- Device Heterogeneity: The wide variety of IoT devices and platforms complicates security management.
- Scalability: As the number of connected devices grows, maintaining security becomes increasingly challenging.
Benefits of RemoteIoT Web SSH
Implementing remote IoT web SSH offers several advantages for organizations and individuals managing IoT devices. Some of the key benefits include:
- Enhanced Security: SSH encrypts all data transmitted between the user and the device, reducing the risk of data breaches.
- Improved Efficiency: Remote access allows users to manage devices without being physically present, saving time and resources.
- Flexibility: Users can access IoT devices from anywhere, provided they have an internet connection.
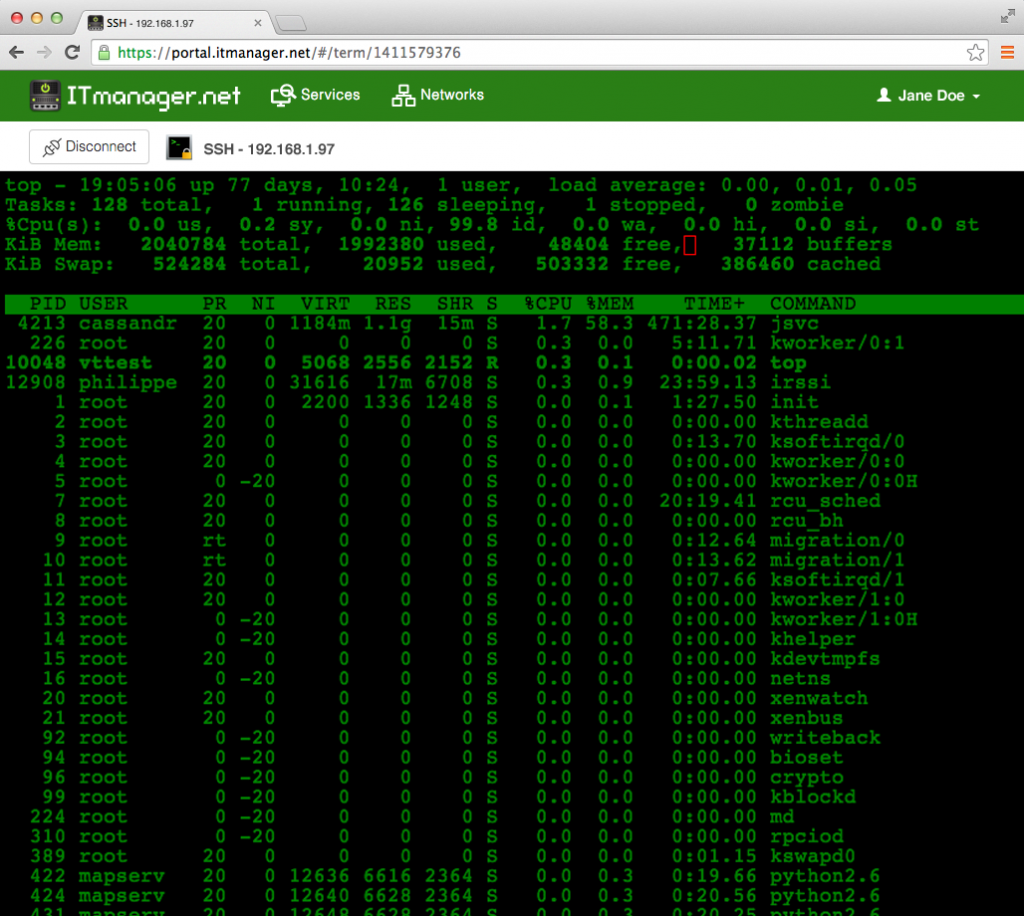
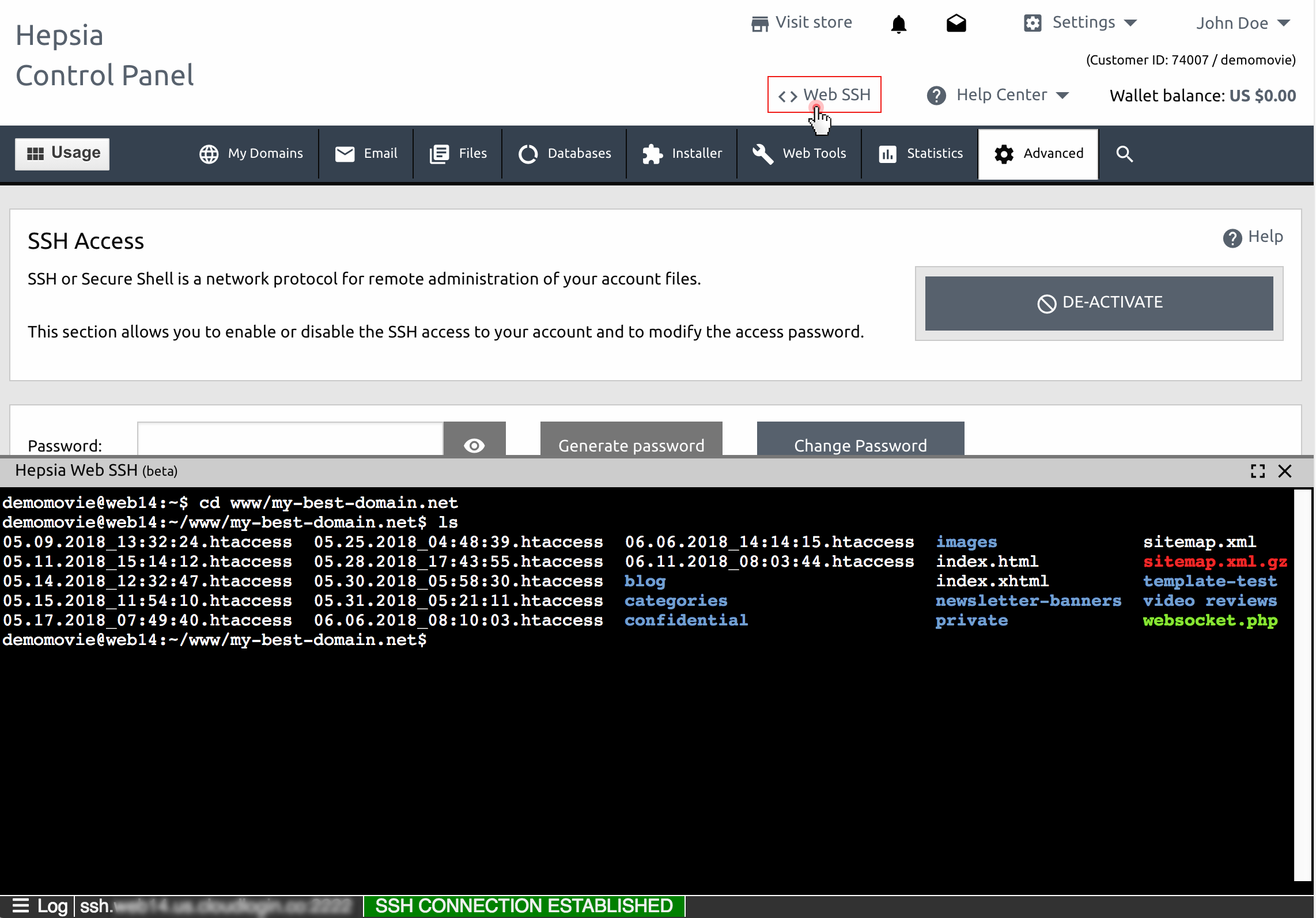
Setting Up RemoteIoT Web SSH
Step-by-Step Guide
Setting up remote IoT web SSH involves several steps, including configuring the server, generating SSH keys, and establishing the connection. Below is a step-by-step guide:
- Install SSH Server: Ensure the IoT device has an SSH server installed and configured.
- Generate SSH Keys: Create public and private keys for secure authentication.
- Configure Firewall Settings: Allow SSH traffic through the firewall to enable remote access.
- Test the Connection: Use an SSH client to connect to the IoT device and verify the setup.
Tips for Successful Implementation
To ensure a smooth setup process, consider the following tips:
- Regularly update the SSH server and client software to address security vulnerabilities.
- Use strong passwords and implement multi-factor authentication for added security.
- Monitor SSH logs for suspicious activity and take appropriate action if necessary.
Security Considerations for RemoteIoT Web SSH
Best Practices for Securing SSH Connections
Securing SSH connections is critical to protecting IoT devices from cyber threats. Below are some best practices to enhance SSH security:
- Disable Password Authentication: Use public key authentication instead of passwords to reduce the risk of brute-force attacks.
- Restrict Access: Limit SSH access to trusted IP addresses and users.
- Use Strong Encryption: Configure SSH to use strong encryption algorithms and ciphers.
Common Security Threats
Some of the common security threats associated with SSH include:
- Brute-Force Attacks: Automated attempts to guess passwords or private keys.
- Man-in-the-Middle Attacks: Intercepting and altering communications between the client and server.
- Configuration Errors: Misconfigured SSH settings can expose devices to unauthorized access.
Best Practices for Managing RemoteIoT Web SSH
Regular Maintenance
Regular maintenance is essential for ensuring the long-term reliability and security of remote IoT web SSH. This includes:
- Updating software and firmware to address security vulnerabilities.
- Monitoring system logs for unusual activity.
- Performing routine backups of critical data.
Training and Awareness
Training staff and raising awareness about SSH security best practices can help prevent security breaches. Educate users on the importance of strong passwords, multi-factor authentication, and secure connection practices.
Common Issues and Troubleshooting Tips
Connection Problems
Connection issues are one of the most common problems encountered when using remote IoT web SSH. Some possible causes include:
- Incorrect IP Address: Verify that the correct IP address is being used for the connection.
- Firewall Restrictions: Ensure that the firewall allows SSH traffic on the appropriate port.
- Network Issues: Check for network connectivity problems that may prevent the connection.
Authentication Failures
Authentication failures can occur due to incorrect credentials or misconfigured authentication settings. To resolve these issues:
- Double-check the username and password or private key being used.
- Verify that public key authentication is properly configured.
- Check the SSH server logs for more information about the failure.
Future Trends in RemoteIoT Web SSH
As technology continues to evolve, so too will the tools and techniques used for remote IoT device management. Some emerging trends in remote IoT web SSH include:
- Quantum-Resistant Encryption: Developing encryption methods that can withstand attacks from quantum computers.
- Artificial Intelligence: Leveraging AI for automated threat detection and response.
- Edge Computing: Shifting processing power closer to the devices to improve performance and reduce latency.
Conclusion
RemoteIoT web SSH is a powerful tool for managing IoT devices securely and efficiently from anywhere in the world. By understanding its capabilities, implementing best practices, and staying informed about emerging trends, you can harness the full potential of this technology. We encourage you to share your thoughts and experiences in the comments section below, and don't forget to explore other articles on our site for more insightful content.