In today's digital age, connecting to IoT devices remotely has become increasingly important for businesses and individuals alike. However, ensuring secure access to these devices while operating behind a firewall is a critical challenge. If you're wondering how to use RemoteIoT behind firewall using advanced techniques, this guide will provide you with step-by-step instructions and expert insights to achieve secure and reliable connections.
As the Internet of Things (IoT) continues to expand, more devices are being integrated into corporate networks and home setups. These devices often require remote access for monitoring, troubleshooting, and management. However, security concerns and network configurations like firewalls can pose significant hurdles. This article addresses those challenges and offers practical solutions.
Whether you're a network administrator, IT professional, or simply someone interested in secure IoT connectivity, this guide will equip you with the knowledge and tools necessary to use RemoteIoT behind a firewall effectively. Let's dive in!
Read also:Exploring The Rise Of Goodtimeswithskyler Tits In Digital Content Creation
Table of Contents:
- Understanding RemoteIoT and Firewalls
- Overview of Firewalls and Their Role in IoT Security
- Setting Up RemoteIoT Behind Firewall
- Advanced Techniques for Secure Connections
- Using SSH Tunneling for Secure Access
- Implementing VPNs for RemoteIoT
- Managing Ports and Firewall Rules
- Tools and Software for RemoteIoT Deployment
- Best Practices for Secure IoT Management
- Troubleshooting Common Issues
Understanding RemoteIoT and Firewalls
RemoteIoT refers to the practice of accessing IoT devices from a remote location, typically outside the local network where the devices are physically located. Firewalls, on the other hand, are security systems designed to monitor and control incoming and outgoing network traffic based on predetermined security rules.
When attempting to use RemoteIoT behind firewall, the primary challenge lies in ensuring that the communication between the remote user and the IoT device remains secure while adhering to the firewall's rules. This requires a thorough understanding of both RemoteIoT technology and firewall configurations.
Key Components of RemoteIoT
Before delving into the specifics of using RemoteIoT behind firewall, it's essential to understand the key components involved:
- IoT Devices: Sensors, cameras, and other connected devices that require remote access.
- Network Infrastructure: The routers, switches, and firewalls that manage data flow within the network.
- Security Protocols: Encryption methods and authentication mechanisms to protect data during transmission.
Overview of Firewalls and Their Role in IoT Security
Firewalls play a crucial role in securing IoT networks by filtering traffic and preventing unauthorized access. They act as a barrier between the internal network and the external world, ensuring that only legitimate traffic is allowed to pass through.
Types of Firewalls
There are several types of firewalls, each with its own set of features and capabilities:
Read also:Controversial Topic The Truth Behind Buscar Kid And His Mom Cctv Video Leak
- Packet Filtering Firewalls: Basic firewalls that examine packets and decide whether to allow or block them based on predefined rules.
- Stateful Inspection Firewalls: More advanced firewalls that track the state of active connections and use this information to make decisions.
- Next-Generation Firewalls (NGFW): Firewalls that combine traditional packet filtering with deep packet inspection, intrusion prevention, and application awareness.
Setting Up RemoteIoT Behind Firewall
Setting up RemoteIoT behind firewall involves several steps, starting with configuring the IoT devices and the firewall itself. Below is a step-by-step guide to help you get started:
Step 1: Configure IoT Devices
Ensure that your IoT devices are properly configured for remote access. This may involve setting up static IP addresses, enabling remote management features, and configuring security settings such as encryption and authentication.
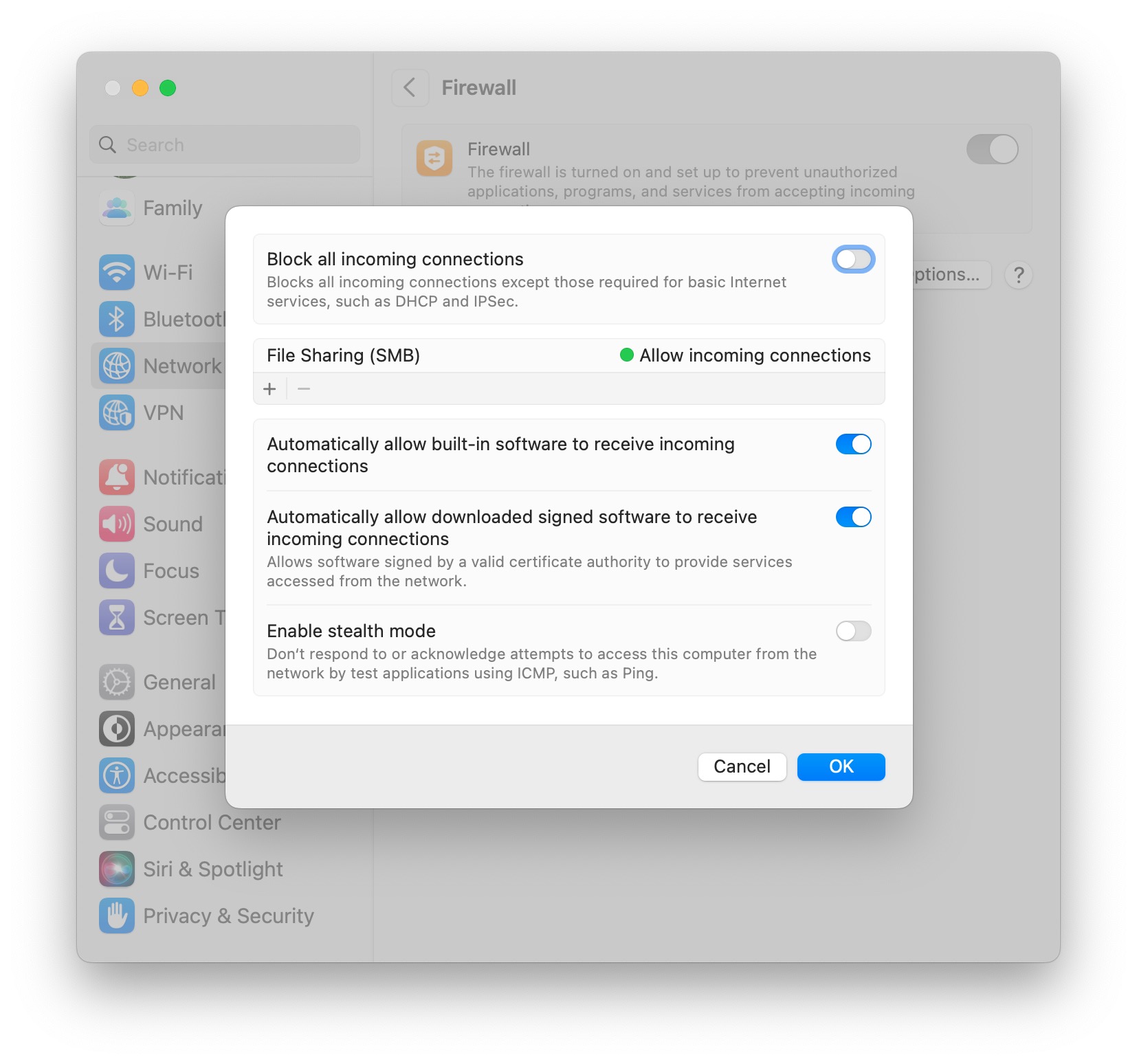
Step 2: Update Firewall Rules
Modify your firewall rules to allow incoming and outgoing traffic for the specific ports used by your IoT devices. Be sure to restrict access to only authorized users and devices.
Step 3: Test the Connection
Once the devices and firewall are configured, test the connection to ensure that remote access is functioning correctly. Use tools like ping and traceroute to diagnose any issues that may arise.
Advanced Techniques for Secure Connections
To enhance the security of your RemoteIoT setup, consider implementing advanced techniques such as encryption, authentication, and access control. These measures will help protect your IoT devices from unauthorized access and potential cyber threats.
Encryption Protocols
Use strong encryption protocols like TLS (Transport Layer Security) to secure data transmissions between the remote user and the IoT device. This ensures that sensitive information remains confidential and protected from eavesdropping.
Using SSH Tunneling for Secure Access
SSH tunneling is a popular method for securing remote connections. By creating an encrypted tunnel between the remote user and the IoT device, SSH ensures that all data transmitted over the network remains secure and private.
Benefits of SSH Tunneling
- Encryption: All data transmitted through the tunnel is encrypted, preventing unauthorized access.
- Authentication: Users must authenticate themselves before gaining access to the tunnel, adding an extra layer of security.
- Flexibility: SSH tunnels can be used to access a wide range of services and applications, making them versatile for various use cases.
Implementing VPNs for RemoteIoT
Virtual Private Networks (VPNs) are another effective way to secure remote IoT connections. By creating a secure, encrypted connection between the remote user and the IoT device, VPNs provide a high level of security and privacy.
Choosing the Right VPN
When selecting a VPN for your RemoteIoT setup, consider factors such as performance, security features, and ease of use. Some popular options include OpenVPN, WireGuard, and IPsec.
Managing Ports and Firewall Rules
Properly managing ports and firewall rules is essential for ensuring secure and reliable RemoteIoT connections. Below are some best practices to follow:
Best Practices for Port Management
- Minimize Open Ports: Only open the ports necessary for your IoT devices to function properly.
- Use Non-Standard Ports: Consider using non-standard ports to reduce the risk of unauthorized access.
- Regularly Review Rules: Periodically review your firewall rules to ensure they remain up-to-date and effective.
Tools and Software for RemoteIoT Deployment
Several tools and software solutions are available to assist with RemoteIoT deployment and management. These tools can help simplify the process and improve overall security.
Popular Tools
- PRTG Network Monitor: A comprehensive network monitoring solution that supports IoT devices.
- Device42: An asset management platform designed for IoT and IT infrastructure.
- FreeRADIUS: An open-source RADIUS server for authentication and access control.
Best Practices for Secure IoT Management
Adhering to best practices is crucial for maintaining the security and reliability of your RemoteIoT setup. Below are some recommendations to follow:
Security Recommendations
- Regular Updates: Keep your IoT devices and firmware up-to-date to protect against vulnerabilities.
- Strong Passwords: Use strong, unique passwords for all devices and accounts.
- Network Segmentation: Isolate IoT devices on a separate network to reduce the risk of unauthorized access.
Troubleshooting Common Issues
Even with careful planning and implementation, issues may arise when using RemoteIoT behind firewall. Below are some common problems and their solutions:
Connection Issues
If you're experiencing connection issues, check the following:
- Firewall Rules: Ensure that the necessary ports are open and the rules are correctly configured.
- Device Configuration: Verify that the IoT devices are properly configured for remote access.
- Network Connectivity: Confirm that the network connection is stable and functioning correctly.
Conclusion
In conclusion, using RemoteIoT behind firewall requires a combination of technical expertise, proper configuration, and adherence to best practices. By following the steps and recommendations outlined in this guide, you can achieve secure and reliable remote access to your IoT devices while maintaining the integrity of your network.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and network management. Together, let's build a safer and more connected digital world!
Data Source: Cisco IoT Security, Akamai IoT Security Whitepaper