In today's interconnected world, managing IoT devices remotely is crucial for businesses and individuals alike. However, using RemoteIoT behind a firewall introduces unique challenges that need to be addressed effectively. In this article, we'll explore how to use RemoteIoT behind a firewall while maintaining security and efficiency.
As more organizations adopt IoT technologies, the need for secure remote access becomes increasingly important. Firewalls play a critical role in protecting networks, but they can also block necessary communications. This guide will help you navigate these challenges and ensure seamless connectivity.
Whether you're a network administrator or a tech enthusiast, understanding how to use RemoteIoT behind a firewall is essential. By following the strategies outlined in this article, you'll be able to maintain robust security while enabling remote access to your IoT devices.
Read also:Till Lindemann Wife Discovering The Life And Love Of The Legendary Rammstein Frontman
Table of Contents
- Introduction
- Understanding Firewalls and Their Role
- Basics of RemoteIoT
- Challenges of Using RemoteIoT Behind Firewall
- Solutions for RemoteIoT Behind Firewall
- Port Forwarding
- Using a Virtual Private Network (VPN)
- Cloud-Based Solutions
- Best Practices for Security
- Troubleshooting Tips
- Conclusion
Introduction
In the rapidly evolving landscape of IoT technology, the ability to manage devices remotely has become indispensable. However, organizations often face challenges when attempting to use RemoteIoT behind a firewall. Firewalls are designed to protect networks from unauthorized access, but they can inadvertently block legitimate traffic. This article aims to provide a comprehensive guide on how to overcome these obstacles.
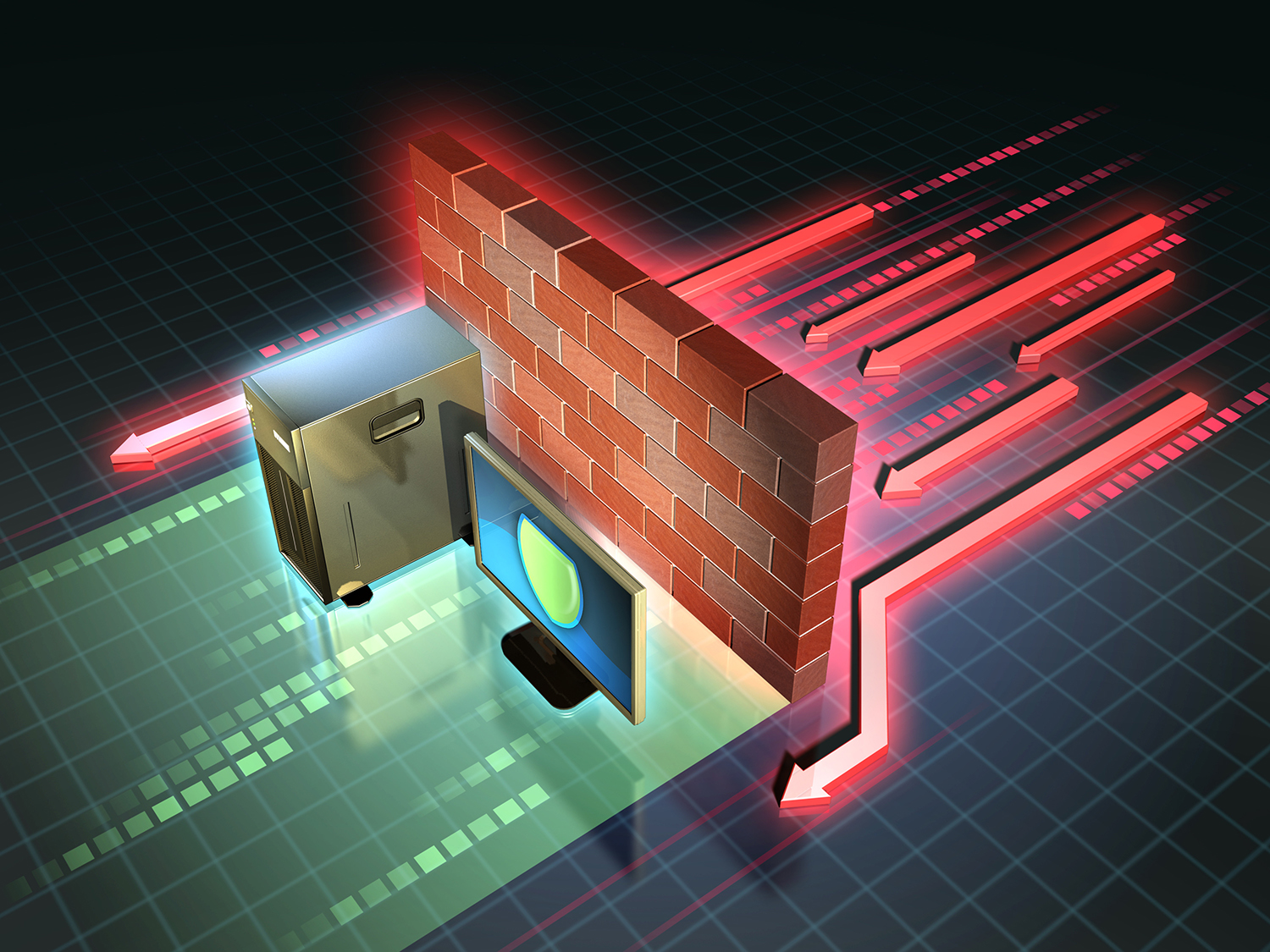
Understanding Firewalls and Their Role
Firewalls act as a barrier between internal networks and external threats. They monitor and control incoming and outgoing network traffic based on predetermined security rules. Understanding how firewalls operate is essential when implementing RemoteIoT solutions.
Modern firewalls offer advanced features such as:
- Intrusion detection and prevention
- Application filtering
- Deep packet inspection
These features enhance security but can complicate remote access configurations.
Basics of RemoteIoT
RemoteIoT refers to the ability to manage and monitor IoT devices from a distance. This technology enables users to control devices, collect data, and perform updates without physical access. Key components of RemoteIoT include:
- Communication protocols
- Cloud platforms
- Device management software
Understanding these components is crucial for successful implementation behind a firewall.
Read also:Lauren Graham Kids A Comprehensive Look Into The Lives Of Lauren Grahams Children
Challenges of Using RemoteIoT Behind Firewall
Restricted Access
Firewalls often restrict access to certain ports and protocols, making it difficult to establish a connection with IoT devices. This can lead to connectivity issues and hinder remote management.
Data Security
Ensuring the security of data transmitted through a firewall is a significant challenge. Unauthorized access to sensitive information can have severe consequences, making security a top priority.
Performance Issues
Firewalls can introduce latency and affect the performance of RemoteIoT connections. Optimizing configurations is necessary to maintain efficient communication.
Solutions for RemoteIoT Behind Firewall
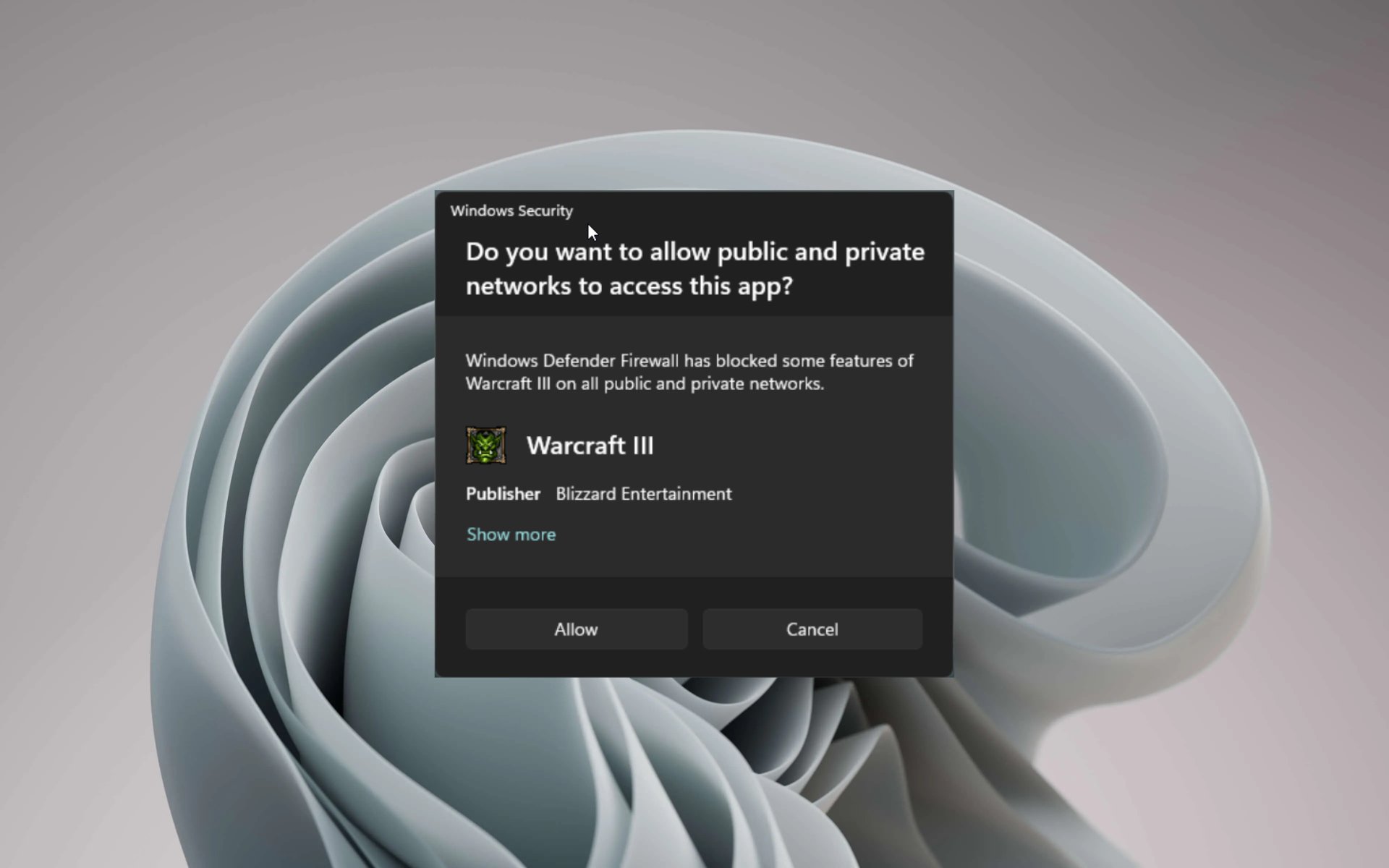
Configuring Firewall Rules
Adjusting firewall settings to allow specific traffic is one of the most effective solutions. By creating rules that permit necessary ports and protocols, you can ensure seamless connectivity without compromising security.
Port Forwarding
Port forwarding is a technique used to direct incoming traffic to a specific device within a network. This method allows RemoteIoT devices to communicate with external systems while remaining protected by the firewall.
Steps for implementing port forwarding:
- Identify the required ports for RemoteIoT communication
- Access your router's settings
- Create forwarding rules for the identified ports
- Test the connection to ensure proper functionality
Using a Virtual Private Network (VPN)
A Virtual Private Network (VPN) provides a secure tunnel for communication between devices. By using a VPN, you can bypass firewall restrictions while maintaining data encryption and privacy.
Benefits of using a VPN for RemoteIoT:
- Enhanced security
- Improved privacy
- Seamless connectivity
Cloud-Based Solutions
Cloud platforms offer scalable and secure solutions for managing IoT devices remotely. By leveraging cloud services, you can overcome firewall limitations and ensure reliable communication.
Popular cloud platforms for RemoteIoT include:
- Amazon Web Services (AWS)
- Microsoft Azure
- Google Cloud Platform
These platforms provide robust features for device management and data analytics.
Best Practices for Security
Maintaining security is paramount when using RemoteIoT behind a firewall. Here are some best practices to follow:
- Regularly update firmware and software
- Implement strong authentication mechanisms
- Monitor network activity for suspicious behavior
- Encrypt all data transmissions
By adhering to these practices, you can minimize the risk of security breaches.
Troubleshooting Tips
Even with proper configurations, issues may arise when using RemoteIoT behind a firewall. Here are some troubleshooting tips:
- Check firewall logs for blocked connections
- Verify port forwarding settings
- Test connectivity using alternative devices
- Consult documentation and support forums
These steps can help identify and resolve common problems.
Conclusion
Using RemoteIoT behind a firewall requires careful planning and implementation. By understanding the challenges and adopting effective solutions, you can ensure secure and efficient remote access to your IoT devices. This guide has provided insights into configuring firewalls, utilizing port forwarding, employing VPNs, and leveraging cloud-based solutions.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more valuable information. Together, let's build a safer and more connected future!