As the Internet of Things (IoT) continues to revolutionize how we interact with technology, managing remote IoT devices securely has become a top priority for developers and engineers. Remote IoT device SSH (Secure Shell) is one of the most reliable methods to access and manage these devices from anywhere in the world. This tutorial will guide you step-by-step on how to set up, configure, and secure SSH connections for your IoT devices.
Whether you're a beginner or an experienced professional, understanding SSH for IoT devices is crucial for ensuring secure communication between your network and devices. This tutorial will cover everything from the basics of SSH to advanced configurations, making it easier for you to manage your IoT ecosystem efficiently.
By the end of this guide, you'll have a clear understanding of how to leverage SSH for remote IoT device management, enhancing both security and functionality. Let's dive in and explore the world of remote IoT device SSH management.
Read also:Movierulz 2023 Telugu Your Ultimate Guide To Telugu Movies
Table of Contents
- Introduction to SSH
- Why Use SSH for IoT Devices?
- Preparing Your IoT Device
- Installing an SSH Server
- Configuring SSH
- Connecting to Your Remote IoT Device
- Securing Your SSH Connection
- Troubleshooting Common Issues
- Best Practices for Remote IoT Device SSH
- Conclusion
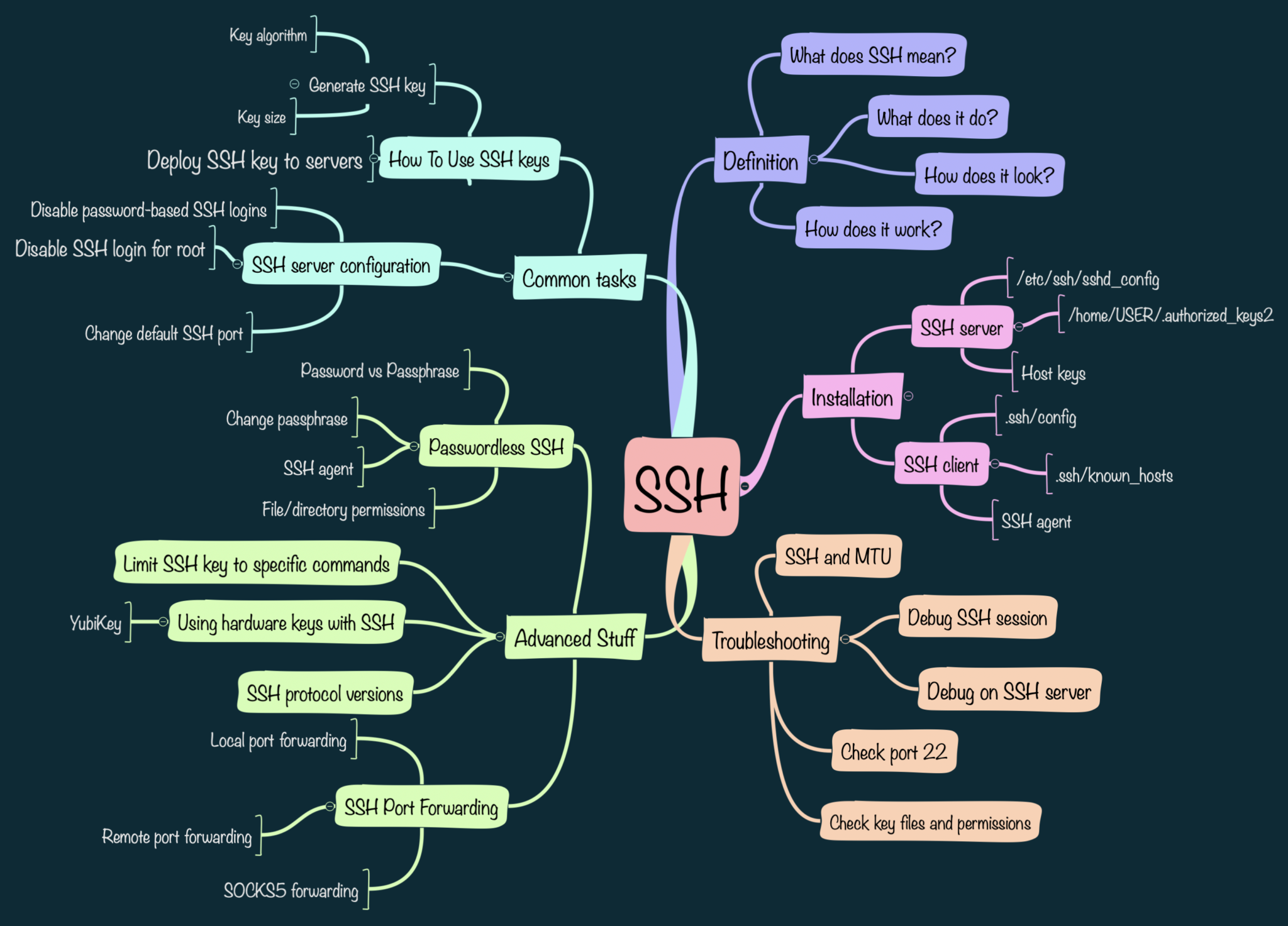
Introduction to SSH
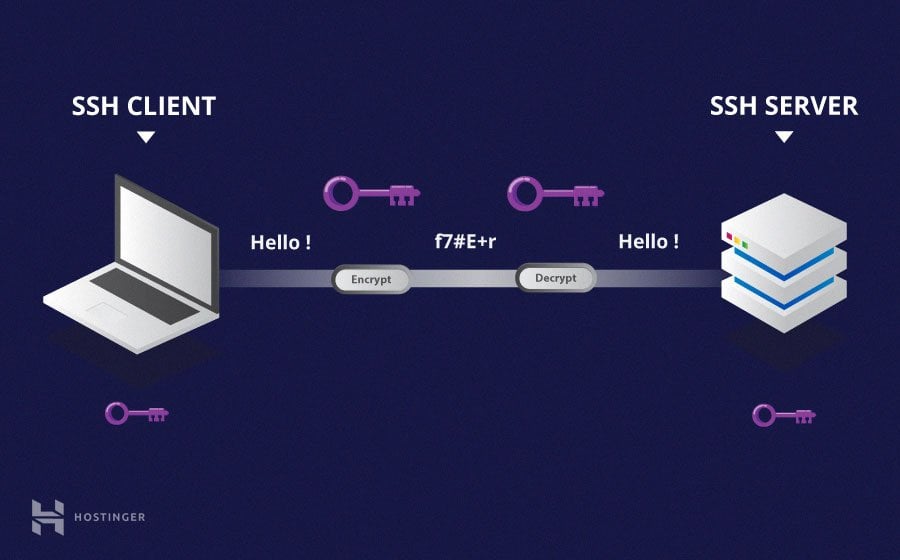
Secure Shell (SSH) is a cryptographic network protocol that allows secure communication over an unsecured network. It is widely used for remote login and other secure network services. In the context of IoT devices, SSH provides a secure way to access and manage devices remotely, ensuring that sensitive data remains protected.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between the client and server, preventing unauthorized access.
- Authentication: SSH supports multiple authentication methods, including passwords and public-key authentication, ensuring only authorized users can access the system.
- Command Execution: You can execute commands on remote devices as if you were physically present, making it ideal for IoT device management.
Why Use SSH for IoT Devices?
IoT devices are often deployed in remote locations, making physical access impractical. SSH offers a secure and efficient way to manage these devices from anywhere in the world. Here are some reasons why SSH is the preferred choice for IoT device management:
Security
SSH encrypts all communication between the client and server, ensuring that sensitive data remains secure. This is particularly important for IoT devices that handle critical data.
Flexibility
SSH supports a wide range of functionalities, from simple file transfers to complex command executions. This flexibility makes it ideal for managing IoT devices with varying requirements.
Preparing Your IoT Device
Before setting up SSH on your IoT device, ensure that it meets the necessary requirements. Here's a checklist to help you prepare:
- Ensure your IoT device has a stable internet connection.
- Update the operating system and all installed software to the latest versions.
- Create a backup of your current configuration to prevent data loss during setup.
Checking Hardware Compatibility
Not all IoT devices support SSH out of the box. Check the device specifications to ensure compatibility. Most modern IoT devices running Linux-based operating systems, such as Raspberry Pi, support SSH natively.
Read also:Kim Kardashian Siblings The Complete Guide To Their Lives Careers And Influence
Installing an SSH Server
Once your IoT device is ready, the next step is to install an SSH server. This process varies depending on the operating system running on your device. Below are instructions for some common IoT operating systems:
Installing SSH on Raspberry Pi
For Raspberry Pi devices running Raspbian, SSH is enabled by default. To ensure it's active, open the terminal and type:
sudo systemctl status ssh
If SSH is not active, enable it using:
sudo systemctl enable ssh
Installing SSH on Other Linux Distributions
For other Linux-based IoT devices, you can install the OpenSSH server using the following command:
sudo apt-get install openssh-server
Configuring SSH
After installing the SSH server, the next step is to configure it to suit your needs. The SSH configuration file is located at /etc/ssh/sshd_config. Here are some key configurations to consider:
Changing the Default Port
Changing the default SSH port (22) can enhance security by reducing the risk of automated attacks. To change the port, edit the configuration file:
sudo nano /etc/ssh/sshd_config
Find the line that says Port 22 and change it to your desired port number. Remember to update your firewall rules to allow traffic on the new port.
Disabling Password Authentication
Using public-key authentication instead of passwords adds an extra layer of security. To disable password authentication, edit the configuration file and set:
PasswordAuthentication no
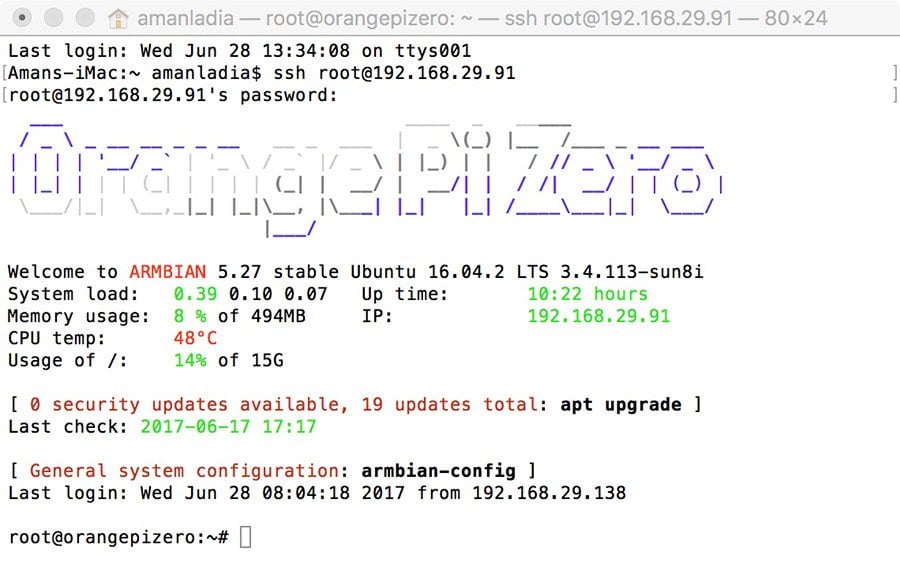
Connecting to Your Remote IoT Device
With SSH configured, you can now connect to your IoT device from a remote location. Use the following command to establish a connection:
ssh username@ip_address -p port_number
Replace username with your device's username, ip_address with the device's IP address, and port_number with the SSH port you configured earlier.
Using SSH Clients
For Windows users, tools like PuTTY can be used to connect to your IoT device. Simply enter the device's IP address, port number, and username in the respective fields and click "Open" to establish the connection.
Securing Your SSH Connection
While SSH is inherently secure, additional measures can further enhance its security. Below are some best practices:
- Use strong, unique passwords or public-key authentication.
- Limit access to specific IP addresses using firewall rules.
- Regularly update the SSH server and related software to patch vulnerabilities.
Implementing Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security by requiring users to provide two forms of identification before accessing the system. Tools like Google Authenticator can be integrated with SSH for added security.
Troubleshooting Common Issues
Even with proper setup, issues can arise when using SSH for IoT devices. Below are some common problems and their solutions:
Connection Refused
If you receive a "Connection refused" error, ensure that:
- The SSH server is running on the device.
- The correct IP address and port number are used.
- Firewall rules allow traffic on the SSH port.
Authentication Failed
If authentication fails, verify that:
- The username and password are correct.
- Public-key authentication is properly configured.
Best Practices for Remote IoT Device SSH
Adhering to best practices ensures that your SSH setup remains secure and efficient. Here are some tips:
- Regularly monitor SSH logs for suspicious activity.
- Limit the number of failed login attempts to prevent brute-force attacks.
- Use SSH keys with strong passphrases for authentication.
Regular Audits
Conduct regular audits of your SSH setup to identify and address potential vulnerabilities. This proactive approach can prevent security breaches and ensure the longevity of your IoT ecosystem.
Conclusion
This comprehensive remote IoT device SSH tutorial has covered everything you need to know about setting up, configuring, and securing SSH connections for your IoT devices. By following the steps outlined in this guide, you can ensure that your IoT devices remain secure and manageable from anywhere in the world.
We encourage you to share this article with your peers and explore our other resources for more insights into IoT and cybersecurity. Leave a comment below if you have any questions or suggestions for future topics. Together, let's build a safer and more connected world!