In today's rapidly advancing world of the Internet of Things (IoT), SSH remote access plays a pivotal role in managing and securing IoT devices, especially when it comes to Raspberry Pi. Whether you're a hobbyist or a professional developer, understanding how to implement the best SSH remote IoT Raspberry Pi solutions can significantly boost your project's efficiency and security.
SSH, or Secure Shell, is a cryptographic network protocol that ensures secure communication between devices over an unsecured network. For Raspberry Pi users, SSH is indispensable for remote management, automation, and monitoring. This article dives deep into the best SSH remote IoT Raspberry Pi configurations, exploring their setup, benefits, and potential challenges.
By the end of this guide, you'll have a comprehensive understanding of how to leverage SSH for IoT projects using Raspberry Pi, empowering you to create secure, scalable, and efficient systems tailored to your needs. Let's get started!
Read also:How Tall Is Dorit Kemsley Discover The Real Facts About This Reality Star
Table of Contents
- Introduction to SSH Remote IoT Raspberry Pi
- Benefits of Using SSH for IoT on Raspberry Pi
- Step-by-Step SSH Setup Guide for Raspberry Pi
- Best Practices for Secure SSH Remote IoT Raspberry Pi
- Advanced SSH Configurations for IoT
- Common Issues and Troubleshooting
- Tools and Software for Enhanced SSH Management
- SSH Automation for IoT Devices
- Security Considerations for SSH Remote IoT
- Future Trends in SSH Remote IoT Raspberry Pi
Introduction to SSH Remote IoT Raspberry Pi
The best SSH remote IoT Raspberry Pi solutions are designed to provide seamless connectivity and control over your IoT devices. SSH ensures that your data is encrypted and secure, making it an ideal choice for remote management. By leveraging SSH, you can remotely access your Raspberry Pi, execute commands, transfer files, and monitor your IoT setup without compromising security.
Why SSH is Essential for IoT Projects
SSH is more than just a tool; it's a protocol that guarantees secure communication. For IoT enthusiasts, this means:
- Encrypted data transfer
- Remote access without physical presence
- Scalability for large IoT networks
- Compatibility with various operating systems
Benefits of Using SSH for IoT on Raspberry Pi
Using SSH for IoT on Raspberry Pi offers numerous advantages, including enhanced security, flexibility, and ease of use. Below are some key benefits:
Security and Privacy
SSH encrypts all communication between your device and the Raspberry Pi, ensuring that sensitive data remains protected from unauthorized access.
Remote Access
With SSH, you can manage your Raspberry Pi from anywhere in the world, as long as you have an internet connection. This is particularly useful for IoT projects that require constant monitoring and maintenance.
Step-by-Step SSH Setup Guide for Raspberry Pi
Setting up SSH on your Raspberry Pi is straightforward. Follow these steps to get started:
Read also:Hdhub4uin Movie Your Ultimate Destination For Highquality Films
Enabling SSH on Raspberry Pi OS
- Boot up your Raspberry Pi and log in.
- Open the terminal and type the following command:
sudo raspi-config. - Navigate to "Interfacing Options" and select "SSH".
- Choose "Yes" to enable SSH and reboot your Raspberry Pi.
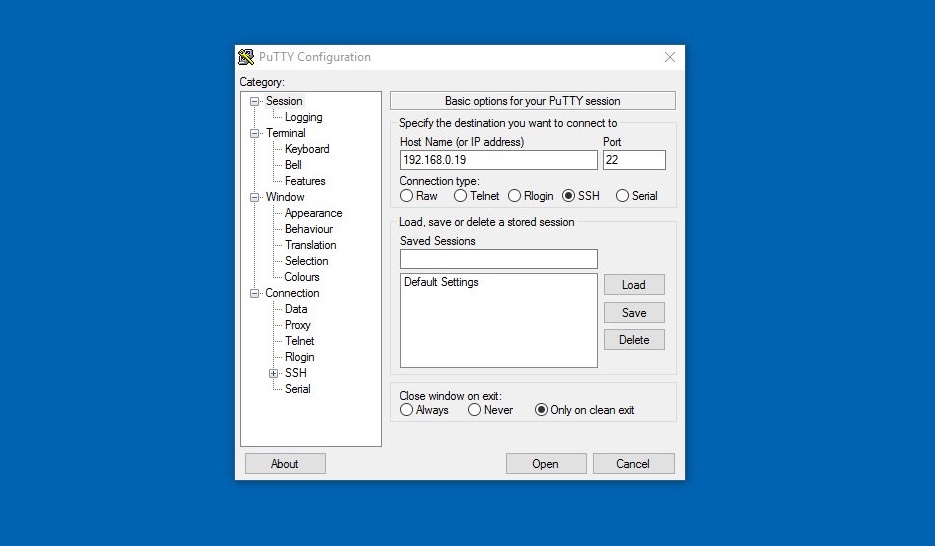
Connecting to Your Raspberry Pi via SSH
Once SSH is enabled, you can connect to your Raspberry Pi using an SSH client. On Windows, you can use PuTTY, while macOS and Linux users can use the built-in terminal. Simply type:
ssh pi@Best Practices for Secure SSH Remote IoT Raspberry Pi
Implementing best practices is crucial to ensure the security and reliability of your SSH setup. Here are some tips:
Change Default Credentials
Always change the default username and password for your Raspberry Pi to prevent unauthorized access.
Use Public Key Authentication
Public key authentication enhances security by eliminating the need for passwords. Generate a public-private key pair and add the public key to your Raspberry Pi's authorized_keys file.
Advanced SSH Configurations for IoT
For advanced users, there are several configurations that can optimize your SSH setup for IoT projects.
Port Forwarding
Port forwarding allows you to securely access your Raspberry Pi from outside your local network. This is particularly useful for remote IoT monitoring.
Tunneling
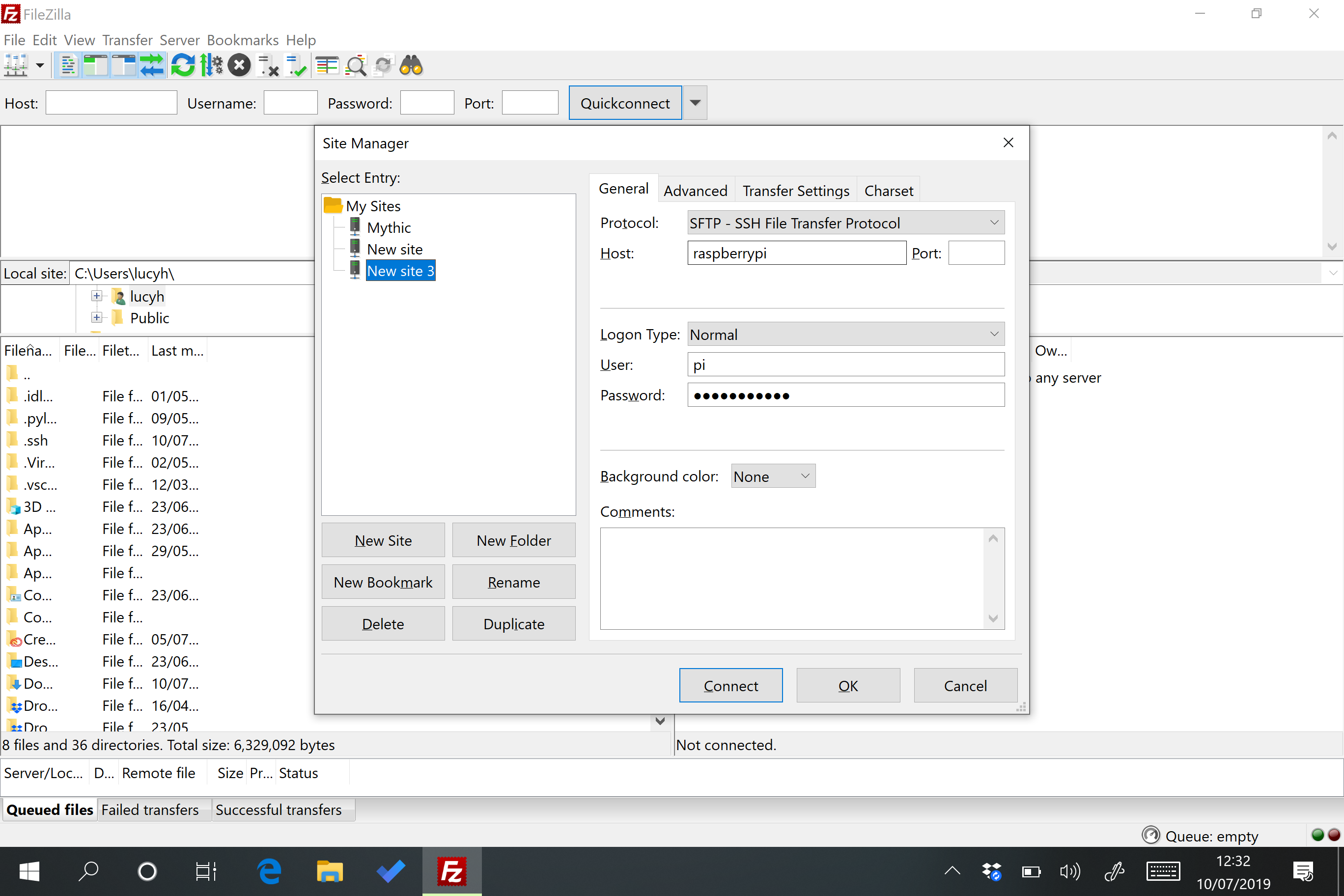
SSH tunneling enables you to securely transfer data between your local machine and your Raspberry Pi. This is ideal for IoT applications that require secure file transfers.
Common Issues and Troubleshooting
While SSH is a robust protocol, issues can arise. Below are some common problems and their solutions:
Connection Refused
If you receive a "connection refused" error, ensure that SSH is enabled on your Raspberry Pi and that your IP address is correct.
Authentication Failed
Authentication failures are often due to incorrect credentials or misconfigured SSH settings. Double-check your username, password, and public key settings.
Tools and Software for Enhanced SSH Management
Several tools and software can enhance your SSH management experience:
SSH Client Applications
- PuTTY (Windows)
- Terminal (macOS/Linux)
- Bitvise SSH Client
SSH Configuration Tools
- Ansible
- Puppet
- Chef
SSH Automation for IoT Devices
Automation can significantly streamline your IoT projects. By scripting SSH commands, you can automate tasks such as data collection, system updates, and device monitoring.
Scripting with Bash
Bash scripts can automate repetitive tasks, making your IoT setup more efficient. For example, you can create a script to periodically check the status of your IoT devices and send alerts if issues arise.
Security Considerations for SSH Remote IoT
Security is paramount when managing IoT devices remotely. Here are some security considerations:
Firewall Configuration
Configure your firewall to allow only necessary ports and IP addresses. This minimizes the risk of unauthorized access.
Regular Updates
Keep your Raspberry Pi and SSH software up to date to protect against vulnerabilities.
Future Trends in SSH Remote IoT Raspberry Pi
As IoT continues to evolve, SSH will remain a cornerstone of secure remote management. Future trends include:
Quantum-Safe Encryption
With the advent of quantum computing, quantum-safe encryption methods will become essential for securing IoT devices.
Edge Computing
Edge computing will enable more efficient data processing at the source, reducing latency and enhancing IoT performance.
Conclusion
The best SSH remote IoT Raspberry Pi solutions offer unparalleled security, flexibility, and scalability for your IoT projects. By following the steps outlined in this guide, you can set up a robust SSH environment that meets your needs. Remember to implement best practices and stay updated with the latest security trends to ensure the longevity and reliability of your IoT setup.
We encourage you to share your thoughts and experiences in the comments below. Additionally, feel free to explore other articles on our site for more insights into IoT and Raspberry Pi projects. Together, let's build a smarter, more connected world!