As the Internet of Things (IoT) continues to revolutionize the way we interact with technology, ensuring secure connections has become a top priority for businesses and individuals alike. The ability to remotely connect IoT devices through Virtual Private Cloud (VPC) setups, especially when using versatile hardware like the Raspberry Pi, offers immense potential. However, this process must be done securely to protect sensitive data and maintain system integrity.
In this article, we will explore how to securely connect remote IoT devices using a VPC setup, focusing on the Raspberry Pi as a key component. We’ll also guide you on downloading the necessary software and integrating it with Windows systems. By following these steps, you can create a robust and secure network for your IoT devices.
Whether you're a beginner or an experienced developer, this guide aims to provide comprehensive insights into setting up a secure IoT environment. Let's dive into the details and ensure your IoT ecosystem is protected against potential threats.
Read also:Telugu Movierulz 2025 The Ultimate Guide To Telugu Movies And Beyond
Table of Contents
- Introduction to Secure IoT Connections
- What is a Virtual Private Cloud (VPC)?
- The Role of Raspberry Pi in IoT
- Setting Up a Secure IoT VPC
- Downloading Necessary Software for Raspberry Pi
- Integrating IoT VPC with Windows
- Enhancing Security Measures
- Common Issues and Troubleshooting
- Real-World Case Studies
- Conclusion and Next Steps
Introduction to Secure IoT Connections
The Internet of Things (IoT) has transformed the way we live and work, enabling devices to communicate and share data seamlessly. However, as the number of connected devices grows, so does the risk of cyber threats. Securing IoT connections is crucial, especially when dealing with remote setups. In this section, we will discuss the importance of secure connections and the role of VPC in IoT environments.
Why Security Matters in IoT
IoT devices often handle sensitive data, from personal information to industrial controls. Without proper security measures, these devices can become vulnerable to hacking, data breaches, and unauthorized access. A secure connection ensures that data remains protected and that only authorized users can access the network.
Understanding the Risks
Cyber threats in IoT environments include unauthorized access, data interception, and device hijacking. These risks can lead to significant financial losses and reputational damage. By implementing secure protocols, such as VPC setups, you can mitigate these risks and ensure the safety of your IoT ecosystem.
What is a Virtual Private Cloud (VPC)?
A Virtual Private Cloud (VPC) is a secure and isolated network environment within the cloud. It allows you to create a private network for your IoT devices, ensuring that they communicate securely over the internet. In this section, we will explore the key features and benefits of using a VPC for IoT applications.
Key Features of VPC
- Private IP addresses for devices
- Customizable network configurations
- Enhanced security through encryption
- Scalability for growing IoT ecosystems
Benefits of Using VPC for IoT
VPC provides a secure and reliable environment for IoT devices, reducing the risk of unauthorized access and data breaches. It also offers flexibility in network design, allowing you to tailor the setup to your specific needs. By leveraging VPC, you can ensure that your IoT devices remain protected and perform optimally.
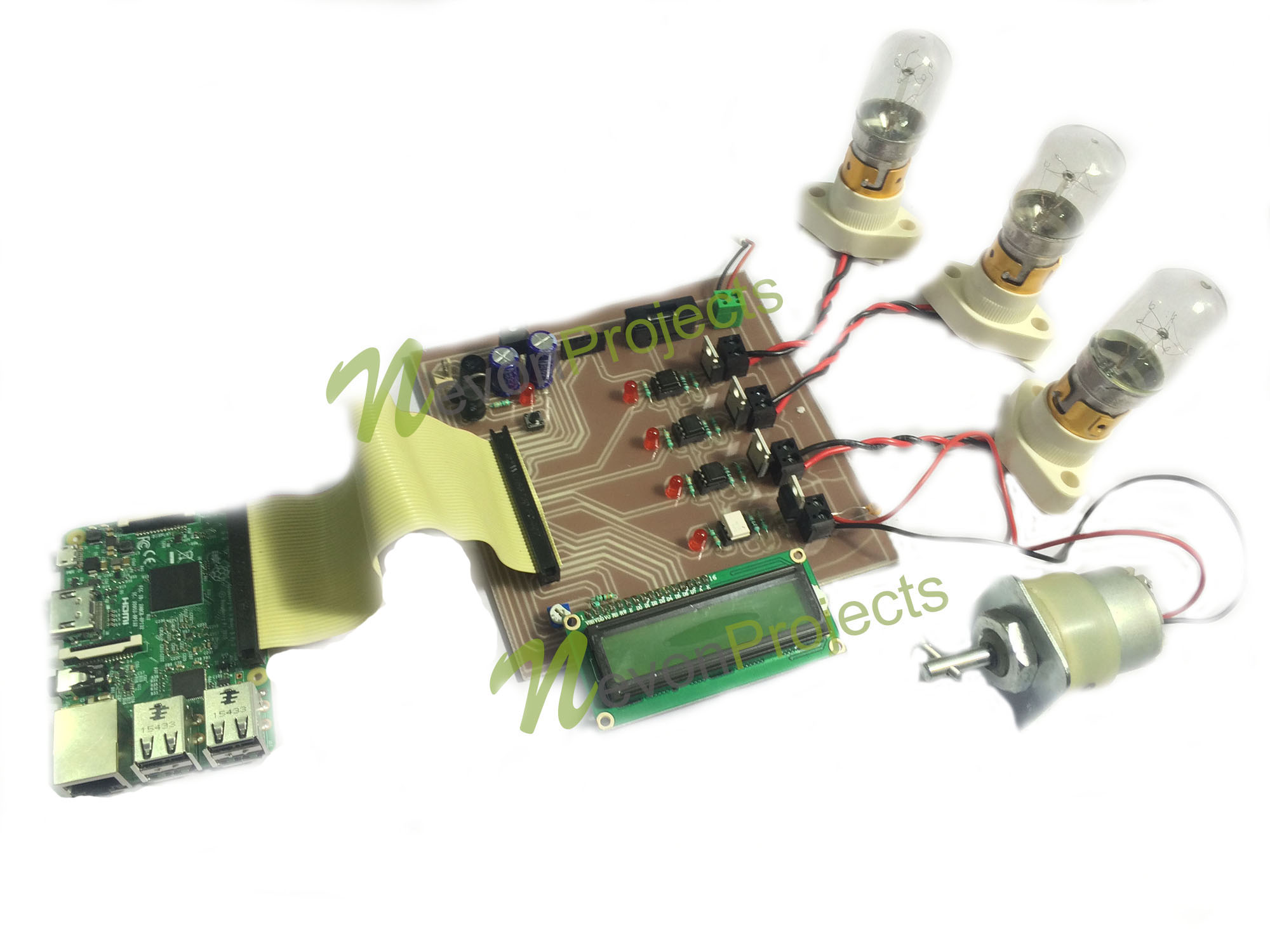
The Role of Raspberry Pi in IoT
The Raspberry Pi is a versatile and cost-effective single-board computer that has become a popular choice for IoT projects. Its ability to run various operating systems and support a wide range of peripherals makes it an ideal platform for building secure IoT setups. In this section, we will discuss how the Raspberry Pi can be used to connect IoT devices securely.
Read also:Lauren Graham Kids A Comprehensive Look Into The Lives Of Lauren Grahams Children
Advantages of Using Raspberry Pi
- Low cost and energy-efficient
- Supports multiple operating systems
- Highly customizable hardware and software
- Large community support for troubleshooting
Setting Up Raspberry Pi for IoT
To use the Raspberry Pi in your IoT setup, you will need to install an operating system, configure the network settings, and secure the device. This process involves downloading the necessary software, setting up the VPC, and ensuring that all components are properly connected.
Setting Up a Secure IoT VPC
Setting up a secure IoT VPC involves several steps, including configuring the network, securing the connection, and testing the setup. In this section, we will guide you through the process, step by step, to ensure a successful implementation.
Step 1: Plan Your Network Architecture
Before setting up the VPC, it’s important to plan your network architecture. This includes identifying the devices that will be connected, determining the required bandwidth, and selecting the appropriate security protocols.
Step 2: Configure the VPC
Using a cloud provider’s VPC service, such as AWS or Google Cloud, configure the VPC settings to match your network requirements. This includes setting up subnets, routing tables, and security groups.
Step 3: Secure the Connection
Implement encryption and authentication protocols to secure the connection between your IoT devices and the VPC. This ensures that data is transmitted safely and that only authorized users can access the network.
Downloading Necessary Software for Raspberry Pi
To connect your Raspberry Pi to the IoT VPC, you will need to download and install the appropriate software. This includes the operating system, network configuration tools, and security software. In this section, we will provide a detailed guide on downloading and installing the necessary software.
Step 1: Download the Raspberry Pi OS
Visit the official Raspberry Pi website to download the latest version of the Raspberry Pi OS. Choose the version that best suits your project requirements, such as the full desktop version or the lightweight version.
Step 2: Install Network Configuration Tools
Once the OS is installed, use the package manager to install network configuration tools, such as SSH and Wi-Fi utilities. These tools will help you manage the network settings and ensure a secure connection.
Step 3: Secure the Device
Install security software, such as firewalls and intrusion detection systems, to protect your Raspberry Pi from potential threats. Regularly update the software to ensure that it remains effective against new vulnerabilities.
Integrating IoT VPC with Windows
Integrating your IoT VPC with a Windows system allows you to manage and monitor your devices from a centralized location. In this section, we will discuss the steps involved in integrating the two systems and ensuring a seamless connection.
Step 1: Set Up Remote Access
Configure remote access settings on your Windows system to allow secure connections to the IoT VPC. This may involve setting up a virtual private network (VPN) or using remote desktop software.
Step 2: Monitor Device Performance
Use monitoring tools to track the performance of your IoT devices and identify any potential issues. This will help you maintain optimal performance and quickly address any problems that arise.
Step 3: Automate Tasks
Set up automation scripts to streamline tasks such as data collection, analysis, and reporting. This will save time and reduce the risk of human error in managing your IoT ecosystem.
Enhancing Security Measures
While setting up a secure IoT VPC is essential, it’s also important to continuously enhance your security measures to protect against evolving threats. In this section, we will explore additional steps you can take to strengthen your IoT security.
Implement Multi-Factor Authentication
Require users to provide multiple forms of identification before accessing the network. This adds an extra layer of security and reduces the risk of unauthorized access.
Regularly Update Software
Keep all software and firmware up to date to ensure that they contain the latest security patches. This will protect your devices from known vulnerabilities and emerging threats.
Monitor Network Activity
Use network monitoring tools to detect and respond to suspicious activity. This will help you identify potential threats early and take appropriate action to mitigate them.
Common Issues and Troubleshooting
Even with the best planning and implementation, issues can arise when setting up a secure IoT VPC. In this section, we will discuss common problems and provide solutions to help you troubleshoot effectively.
Issue 1: Connectivity Problems
If you experience connectivity issues, check the network settings and ensure that all devices are properly configured. Verify that the VPC settings are correct and that the necessary ports are open.
Issue 2: Security Breaches
In the event of a security breach, immediately isolate the affected devices and investigate the source of the breach. Update security protocols and implement additional measures to prevent future incidents.
Real-World Case Studies
To better understand the practical applications of secure IoT VPC setups, let’s look at some real-world case studies. These examples demonstrate how organizations have successfully implemented secure IoT solutions using Raspberry Pi and VPC technology.
Case Study 1: Smart Home Automation
A homeowner used a Raspberry Pi and VPC setup to securely connect smart home devices, enabling remote control and monitoring from a Windows PC. The system provided enhanced security and convenience, allowing the homeowner to manage their devices effortlessly.
Case Study 2: Industrial IoT
An industrial company implemented a secure IoT VPC setup to monitor and control manufacturing processes. By leveraging Raspberry Pi devices and integrating them with Windows systems, they achieved greater efficiency and reliability in their operations.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices through a VPC setup using Raspberry Pi and Windows integration offers numerous benefits, including enhanced security, flexibility, and scalability. By following the steps outlined in this article, you can create a robust and secure IoT ecosystem that meets your specific needs.
We encourage you to take action by implementing these strategies in your own projects. Share your experiences and insights in the comments section below, and don’t forget to explore other articles on our site for more valuable information on IoT and cybersecurity.