In the rapidly evolving world of technology, SSH remote IoT has become a cornerstone for managing internet-connected devices securely and efficiently. As businesses and individuals seek cost-effective solutions, the concept of SSH remote IoT free has gained significant traction. This article delves into the intricacies of SSH remote IoT, its applications, benefits, and how you can leverage it without incurring unnecessary costs.
SSH remote IoT offers a robust solution for controlling and monitoring devices remotely. Whether you're a tech enthusiast, a developer, or a business owner, understanding this technology can significantly enhance your IoT infrastructure's security and functionality.
This comprehensive guide will explore everything you need to know about SSH remote IoT free, including practical tips, best practices, and expert insights to help you get started.
Read also:Tangled Lantern Png A Comprehensive Guide To Enhancing Your Designs
Table of Contents
- Introduction to SSH Remote IoT
- A Brief History of SSH and IoT
- Benefits of SSH Remote IoT Free
- Setting Up SSH Remote IoT
- Enhancing Security in SSH Remote IoT
- Applications of SSH Remote IoT
- Top Tools for SSH Remote IoT
- Common Issues and Troubleshooting
- The Future of SSH Remote IoT
- Conclusion and Call to Action
Introduction to SSH Remote IoT
SSH remote IoT refers to the use of Secure Shell (SSH) protocol to manage and interact with Internet of Things (IoT) devices remotely. This technology enables users to access and control devices securely over the internet without physical proximity.
One of the most appealing aspects of SSH remote IoT is its availability as a free solution. By leveraging open-source tools and configurations, individuals and businesses can implement secure IoT management without incurring significant expenses.
In this section, we will explore the basics of SSH remote IoT, including its definition, purpose, and relevance in today's tech landscape.
A Brief History of SSH and IoT
Secure Shell (SSH) was first developed in 1995 by Tatu Ylönen as a secure alternative to unencrypted protocols like Telnet. Over the years, SSH has evolved into a widely adopted standard for secure communication, especially in networked environments.
IoT, on the other hand, has grown exponentially since the early 2000s, with billions of connected devices now in use worldwide. The convergence of SSH and IoT has created a powerful synergy, allowing users to manage these devices securely and efficiently.
This section will trace the historical development of SSH and IoT, highlighting key milestones and their integration into modern technology.
Read also:Rachel Pizzolato Nude Unveiling The Truth Behind The Controversy
Benefits of SSH Remote IoT Free
Cost-Effectiveness
One of the primary advantages of SSH remote IoT free is its cost-effectiveness. By utilizing open-source tools and configurations, users can implement secure IoT management without paying for expensive proprietary solutions.
Enhanced Security
SSH provides robust encryption and authentication mechanisms, ensuring that data transmitted between devices remains secure. This is particularly important in IoT environments, where security breaches can have severe consequences.
Flexibility and Scalability
SSH remote IoT solutions are highly flexible and scalable, making them suitable for a wide range of applications, from small-scale personal projects to large-scale industrial deployments.
- Cost savings through open-source tools
- Strong encryption and secure authentication
- Adaptability to various use cases
Setting Up SSH Remote IoT
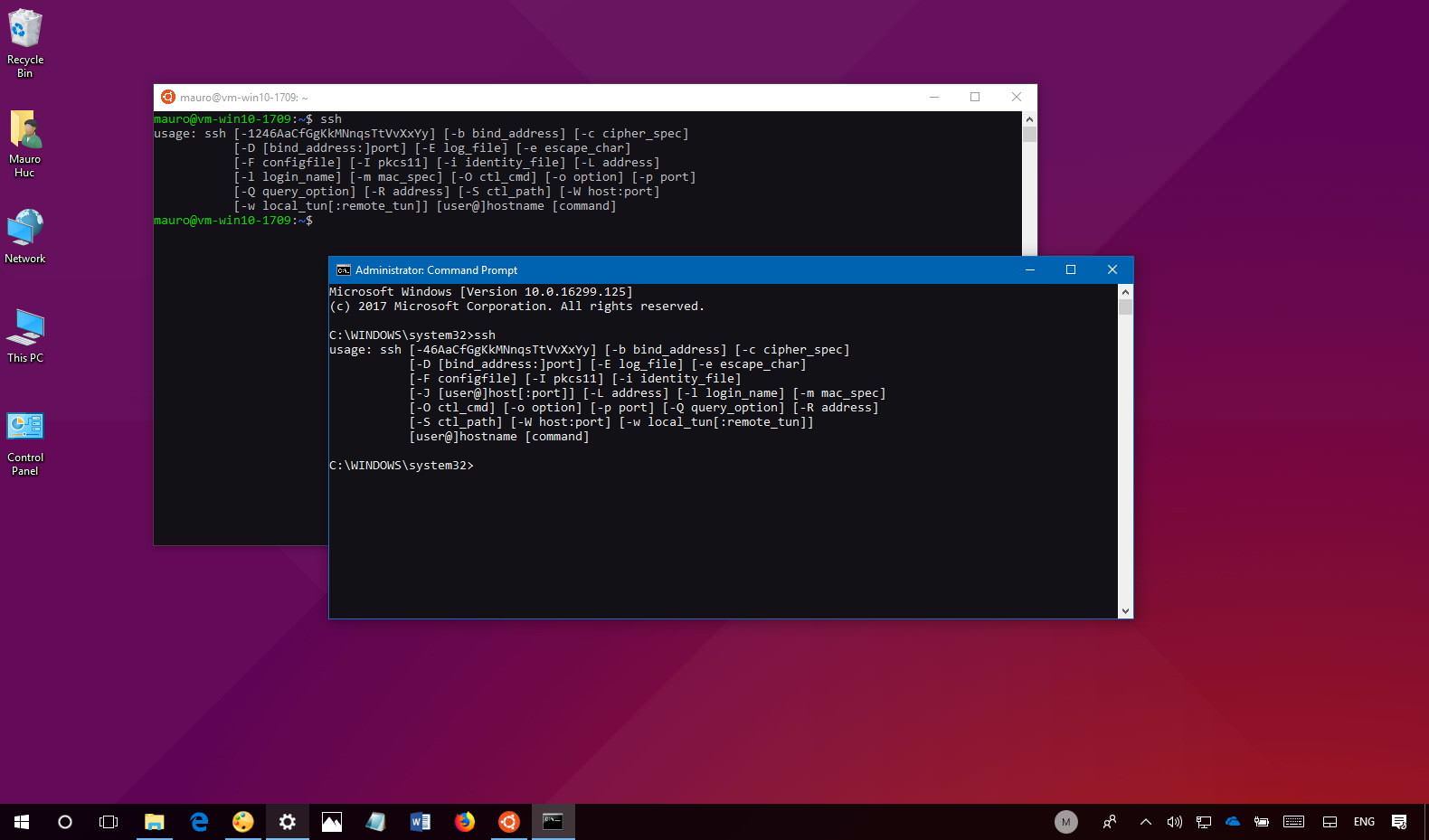
Setting up SSH remote IoT involves several key steps, including configuring the SSH server, enabling remote access, and securing the connection. Below is a step-by-step guide to help you get started:
- Install an SSH server on your IoT device (e.g., OpenSSH for Linux-based systems).
- Configure the server settings to allow remote connections.
- Set up strong authentication methods, such as public key authentication, to enhance security.
- Test the connection to ensure everything is working correctly.
This section will provide detailed instructions and best practices for setting up SSH remote IoT on various platforms.
Enhancing Security in SSH Remote IoT
Security is a critical concern when managing IoT devices remotely. To protect your devices and data, it's essential to implement best practices and advanced security measures. Below are some strategies to enhance security in SSH remote IoT:
- Use strong, unique passwords and enable two-factor authentication.
- Regularly update your SSH server and device firmware to patch vulnerabilities.
- Limit access to trusted IP addresses and use firewall rules to restrict unauthorized connections.
- Monitor logs and implement intrusion detection systems to detect and respond to suspicious activities.
By following these guidelines, you can significantly reduce the risk of security breaches and ensure the integrity of your IoT infrastructure.
Applications of SSH Remote IoT
Home Automation
SSH remote IoT can be used to manage smart home devices, such as lighting, thermostats, and security systems, from anywhere in the world.
Industrial IoT
In industrial settings, SSH remote IoT enables remote monitoring and control of machinery, sensors, and other critical infrastructure components.
Environmental Monitoring
SSH remote IoT is also useful for environmental monitoring applications, such as weather stations and pollution sensors, allowing researchers to collect data remotely.
This section will explore the diverse applications of SSH remote IoT across various industries and use cases.
Top Tools for SSH Remote IoT
Several tools and platforms can facilitate SSH remote IoT implementation. Below are some of the most popular options:
- OpenSSH: A widely used open-source SSH server and client.
- Putty: A popular SSH client for Windows users.
- Paramiko: A Python library for implementing SSH functionality in Python-based IoT projects.
- Tunnlr: A secure tunneling service for remote access to IoT devices.
Each tool has its strengths and weaknesses, so it's essential to choose the one that best fits your specific needs and requirements.
Common Issues and Troubleshooting
While SSH remote IoT is a powerful technology, it can sometimes present challenges. Below are some common issues and their solutions:
- Connection Refused: Ensure the SSH server is running and the firewall allows incoming connections on port 22.
- Authentication Failed: Verify your credentials and ensure public key authentication is correctly configured.
- Slow Performance: Optimize your network settings and reduce unnecessary data transfer to improve performance.
This section will provide practical tips and solutions to help you overcome common obstacles in SSH remote IoT implementation.
The Future of SSH Remote IoT
As IoT continues to expand and evolve, the role of SSH remote IoT will become increasingly important. Advancements in encryption, authentication, and network protocols will further enhance the security and efficiency of remote IoT management.
Additionally, the growing adoption of edge computing and 5G technology will enable faster and more reliable connections, paving the way for new and innovative applications.
This section will explore emerging trends and future developments in SSH remote IoT, offering insights into what lies ahead for this transformative technology.
Conclusion and Call to Action
SSH remote IoT free represents a powerful and cost-effective solution for managing IoT devices securely and efficiently. By understanding its benefits, applications, and best practices, you can harness its potential to enhance your IoT infrastructure and stay ahead in the ever-changing tech landscape.
We encourage you to share your thoughts and experiences in the comments below. Additionally, feel free to explore our other articles for more insights and tips on leveraging technology for personal and professional growth.
Sources: