In today's digital landscape, managing SSH keys for remote IoT devices is crucial for maintaining security and efficiency. Organizations rely heavily on secure communication channels to ensure data integrity and protect against unauthorized access. As more devices become interconnected, the need for robust SSH key management solutions has never been greater.
RemoteIoT SSH key management plays a vital role in securing networks, safeguarding sensitive information, and preventing cyber threats. Without proper management, SSH keys can become a weak link in your security infrastructure, leaving your systems vulnerable to attacks.
This article delves into the best practices for managing SSH keys in remote IoT environments, providing actionable insights and expert guidance to help you implement a secure and efficient system. Whether you're a network administrator, IT professional, or cybersecurity enthusiast, this guide is designed to equip you with the knowledge you need to protect your digital assets.
Read also:Kylie Jenner Dob Exploring The Life And Journey Of A Global Icon
Table of Contents
- Introduction to RemoteIoT SSH Key Management
- Why SSH Key Management is Important
- Common Threats in SSH Key Management
- Best Practices for SSH Key Management
- Top Tools for RemoteIoT SSH Key Management
- Steps to Implement SSH Key Management
- Security Tips for RemoteIoT SSH Keys
- Real-World Case Studies
- Compliance and Regulatory Considerations
- Future Trends in SSH Key Management
- Conclusion
Introduction to RemoteIoT SSH Key Management
SSH (Secure Shell) keys serve as the backbone of secure communication between devices, especially in remote IoT environments. These cryptographic keys provide a secure way to authenticate users and devices without relying on passwords, reducing the risk of brute-force attacks and unauthorized access. Proper management of SSH keys is essential to ensure the security and reliability of your network.
RemoteIoT SSH key management involves organizing, monitoring, and maintaining SSH keys across various devices and systems. It requires a comprehensive approach that addresses key generation, distribution, storage, and revocation. Organizations must adopt best practices to mitigate risks and maintain compliance with industry standards.
As the number of IoT devices continues to grow, the complexity of SSH key management increases. This article explores the challenges and solutions associated with managing SSH keys in remote IoT environments, offering practical advice and expert insights.
Why SSH Key Management is Important
SSH key management is a critical component of cybersecurity, particularly in remote IoT deployments. Without proper management, SSH keys can become a liability, exposing your systems to potential threats such as unauthorized access, data breaches, and malicious attacks.
Key management ensures that only authorized users and devices can access your network, reducing the risk of security breaches. It also simplifies the process of auditing and monitoring key usage, making it easier to identify and respond to suspicious activities. By implementing robust SSH key management practices, organizations can enhance their overall security posture and protect sensitive information.
Furthermore, effective SSH key management helps organizations comply with regulatory requirements and industry standards, such as GDPR, HIPAA, and PCI-DSS. Failure to adhere to these regulations can result in hefty fines and damage to reputation.
Read also:Camilla Arauacutejo Nudes Unveiling The Truth And Debunking Myths
Common Threats in SSH Key Management
Despite its importance, SSH key management is often overlooked, leading to several common threats that can compromise your security:
- Unmanaged Keys: SSH keys that are not properly managed can become outdated or lost, leaving your systems vulnerable to attacks.
- Weak Keys: Using weak or poorly generated SSH keys increases the risk of brute-force attacks and key cracking.
- Shared Keys: Sharing SSH keys among multiple users or devices undermines accountability and makes it difficult to track access.
- Improper Storage: Storing SSH keys in insecure locations, such as unencrypted files or public repositories, exposes them to unauthorized access.
Addressing these threats requires a proactive approach to SSH key management, incorporating best practices and leveraging advanced tools and technologies.
Best Practices for SSH Key Management
Implement Key Rotation
Key rotation is a fundamental practice in SSH key management. It involves periodically replacing old SSH keys with new ones to reduce the risk of compromise. Key rotation should be performed on a regular basis, especially for keys that are used frequently or have been in use for an extended period.
To implement key rotation effectively:
- Set up a schedule for rotating keys.
- Automate the key rotation process using scripts or tools.
- Notify relevant stakeholders about key changes to avoid disruptions.
Enforce Access Control
Access control is another critical aspect of SSH key management. By enforcing strict access control policies, organizations can ensure that only authorized users and devices can access their systems. This involves:
- Assigning unique SSH keys to each user or device.
- Limiting access to specific resources based on user roles and responsibilities.
- Monitoring and auditing key usage to detect and respond to unauthorized access.
Implementing these practices helps organizations maintain control over their SSH keys and reduce the risk of security breaches.
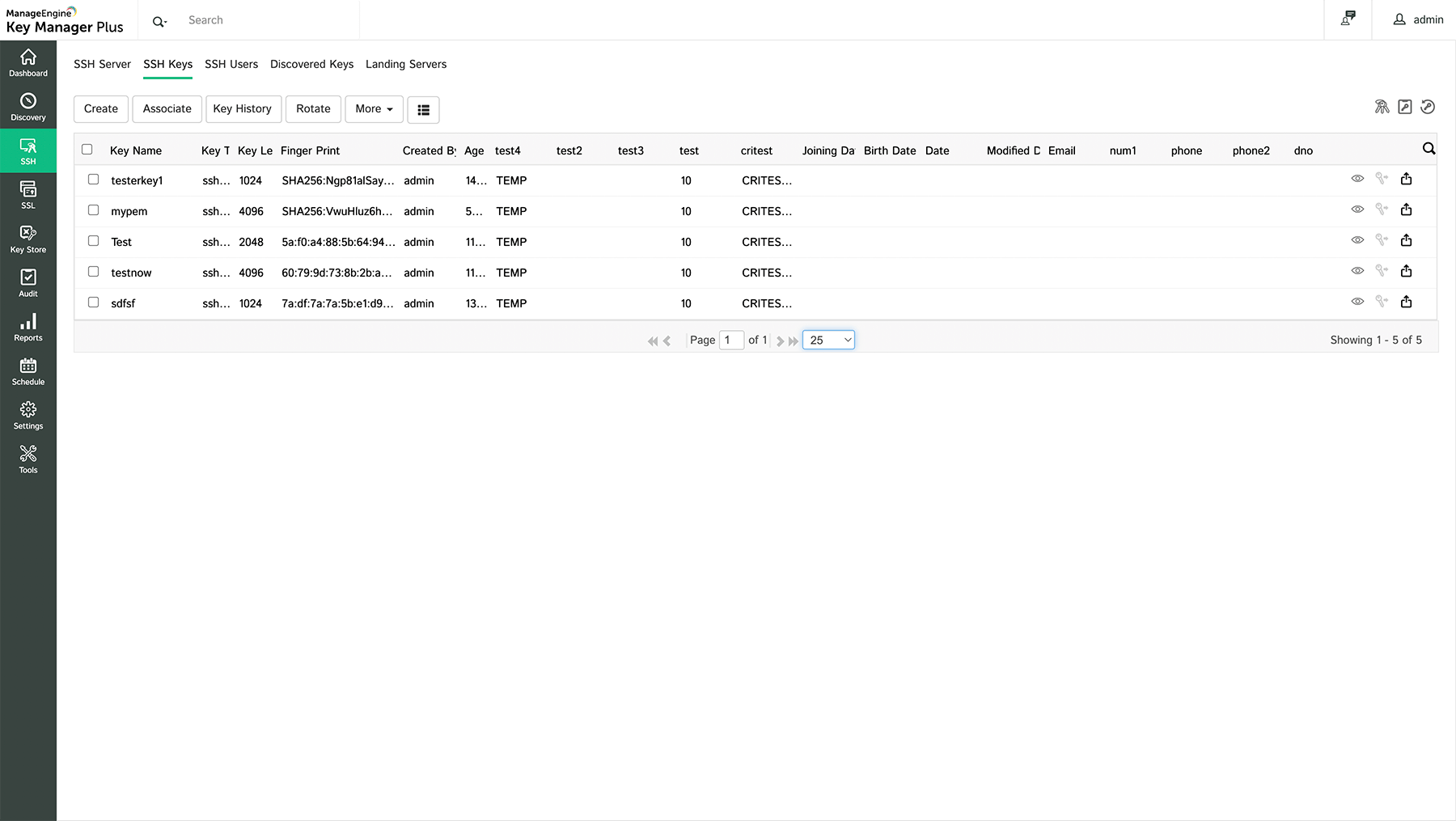
Top Tools for RemoteIoT SSH Key Management
Several tools are available to assist with SSH key management in remote IoT environments. These tools offer features such as key generation, distribution, storage, and monitoring, making it easier to manage SSH keys at scale. Some of the top tools include:
- SSH Key Manager: A comprehensive tool for managing SSH keys across multiple devices and systems.
- HashiCorp Vault: A secure solution for storing and managing SSH keys and other sensitive information.
- OpenSSH: An open-source implementation of the SSH protocol that includes tools for managing SSH keys.
These tools provide a range of features and functionalities to meet the diverse needs of organizations, from small businesses to large enterprises.
Steps to Implement SSH Key Management
Implementing SSH key management requires a systematic approach that involves several key steps:
- Assess Your Needs: Evaluate your organization's requirements and identify the challenges associated with SSH key management.
- Develop a Strategy: Create a comprehensive strategy that outlines your goals, objectives, and action plan for managing SSH keys.
- Choose the Right Tools: Select tools and technologies that align with your strategy and meet your specific needs.
- Train Your Team: Educate your team on best practices for SSH key management and ensure they understand their roles and responsibilities.
- Monitor and Audit: Regularly monitor and audit SSH key usage to detect and respond to potential threats.
By following these steps, organizations can implement an effective SSH key management system that enhances security and efficiency.
Security Tips for RemoteIoT SSH Keys
In addition to best practices and tools, there are several security tips that can help organizations manage SSH keys more effectively:
- Use Strong Keys: Generate SSH keys with sufficient length and complexity to resist brute-force attacks.
- Protect Private Keys: Store private SSH keys in secure locations, such as encrypted files or hardware security modules (HSMs).
- Limit Key Lifespan: Set expiration dates for SSH keys to ensure they are replaced regularly.
- Monitor Key Usage: Track and analyze SSH key usage to identify and address potential security issues.
Implementing these tips can significantly enhance the security of your SSH key management system.
Real-World Case Studies
Several organizations have successfully implemented SSH key management solutions to improve their security and efficiency. For example:
- Case Study 1: A multinational corporation implemented SSH key rotation policies, reducing the number of unauthorized access attempts by 80%.
- Case Study 2: A healthcare provider adopted HashiCorp Vault for SSH key management, achieving compliance with HIPAA regulations and enhancing data protection.
These case studies demonstrate the effectiveness of SSH key management in addressing real-world challenges and improving security outcomes.
Compliance and Regulatory Considerations
SSH key management is closely tied to compliance and regulatory requirements. Organizations must ensure that their SSH key management practices align with relevant regulations, such as:
- GDPR: Ensures the protection of personal data and privacy rights.
- HIPAA: Governs the security and privacy of health information.
- PCI-DSS: Sets standards for securing payment card data.
By adhering to these regulations, organizations can avoid penalties and maintain trust with their customers and stakeholders.
Future Trends in SSH Key Management
The field of SSH key management is evolving rapidly, driven by advancements in technology and changing security requirements. Some of the key trends to watch include:
- Automated Key Management: The increasing use of automation to streamline SSH key management processes.
- Cloud-Based Solutions: The growing adoption of cloud-based tools for managing SSH keys across distributed systems.
- AI and Machine Learning: The integration of AI and machine learning to enhance SSH key monitoring and analysis.
These trends highlight the importance of staying informed and adapting to new developments in SSH key management.
Conclusion
Managing SSH keys in remote IoT environments is a critical task that requires careful planning and execution. By adopting best practices, leveraging advanced tools, and staying informed about emerging trends, organizations can enhance their security and efficiency while maintaining compliance with regulatory requirements.
We encourage readers to take action by implementing the strategies and tips outlined in this article. Whether you're just starting your SSH key management journey or looking to improve an existing system, the insights provided here can help you achieve your goals.
Feel free to leave a comment or share this article with others who may benefit from it. For more information on cybersecurity and IoT security, explore our other articles and resources.